FOOP ransomware infects computers to encrypt files on them
Contents
FOOP ransomware is a malicious file-encrypting virus which originates from STOP/DJVU. The virus uses AES/RSA cryptography to modify files and as a result, the victim can no longer access them. The virus marks each file with .foop file extension, creates _readme.txt ransom notes and saves them in affected data folders. The ransom note suggests contacting the attackers via two email addresses to get further instructions on how to pay the ransom. The note suggests that the ransom price is $490 if the victim contacts the criminals within 72 hours, and $980 later. This virus is dangerous not only because of the data encryption procedure, but also because it installs Azorult Trojan on the system.
Virus’ operandi explained
FOOP ransomware is the 213th version of DJVU ransomware. The virus also uses online and offline encryption methods to lock victim’s files. Once the victim downloads and executes the malicious payload-carrying file, it immediately starts disabling security software related services, some Windows programs, and deletes Volume Shadow Copies.

Next, the virus attempts to connect to the Command&Control server to obtain online encryption key for the victim. If the virus manages to do so and uses the online encryption on the personal files, the only way to restore them is to use a previously created data backup.
However, in some cases the virus fails to connect to its C&C server. In such case, it uses an offline encryption key which is the same for all victims affected by the offline attack. In such case, the encryption and decryption key pair is the same for victims of such attack. Once one of them pays the ransom and shares the obtained keys with security researchers, the STOP decryptor gets updated. So to answer your question – at the moment, there is no known ways to decrypt .foop file type data. Please check for updates in this guide about STOP/DJVU decryption.

If your files were corrupted by this virus, please remove FOOP ransomware as soon as you can. Having it on your system poses a threat to your security and leaves the system vulnerable to further attacks.
Ransomware Summary
| Name | FOOP ransomware virus |
| Type | Ransomware |
| Origins | STOP/DJVU |
| File marker | .foop extension |
| Ransom note | _readme.txt |
| Ransom demand | $490 if victim contacts the attackers within 72 hours or $980 later |
| Contact emails | helpdatarestore@firemail.cc, helpmanager@mail.ch |
| Distribution | Typically spreads in a form of software cracks or other illegal tools used to hack software licenses for free |
| Decryption possibilities | No ways to recover data without backups, unless affected by offline encryption key |
| Removal | Remove using antivirus while in Safe Mode as explained in the tutorial below |
The ransom demand stated in _readme.txt file
FOOP ransomware drops _readme.txt notes in folders containing personal data, such as Desktop, My Documents, Downloads, and other folders created or managed by the user. The note suggests that the victim shouldn’t worry as files can be recovered – however, one needs to pay a ransom in Bitcoin to access the decryption tool and key.
According to the note, the victim can test the decryptor. To do so, one needs to send one encrypted and small file that doesn’t contain valuable data to criminals via helpdatarestore@firemail.cc, helpmanager@mail.ch, including victim’s Personal ID. The attackers promise to send back the decrypted file and instructions how to pay the ransom. The criminals will need to provide crypto-wallet address and further details for you.
It goes without saying that paying the ransom isn’t a good idea. First of all, you might not recover your files even after paying. Next, supporting cyber criminals by following their demands is never a suggestion from cyber security experts.
STOP/DJVU variants’ distribution relies on illegal downloads
FOOP file virus, just like LOKD, REZM, OPQZ or NPPP variants are known to attack computer users in disguise. They often travel in a form of a software crack, key generation or another illegal tool. If you are willing to try to install licensed software versions for free, please remember that it is illegal. Moreover, it is highly dangerous – you can lose years of work or memories in seconds.
Therefore, we recommend staying away from suspicious games, photo/video editing or other software cracks and opt to pay for legitimate and real licenses instead. What is more, we advise being careful while browsing the web and avoiding suspicious email attachments. Finally, create a data backup regularly. This will ensure that you’ll have fresh copies of data on hand anytime. Do not forget to store data backup drive somewhere away from the computer – do not keep the device plugged in.
Steps to Remove FOOP Ransomware Virus
If you want to keep your computer safe, remove FOOP ransomware virus without any hesitations now. You will need to prepare your PC for the elimination procedure attentively. Please follow the steps given below to boot your PC in Safe Mode. Then carry out the next steps to complete the deletion of the virus.
FOOP ransomware removal should be done using a trustworthy antivirus or anti-malware software. Make sure you read our reviews on them. Once the deletion is complete, do not forget to change passwords for all websites and accounts saved in your web browsers as soon as possible.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS

Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
FOOP Ransomware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
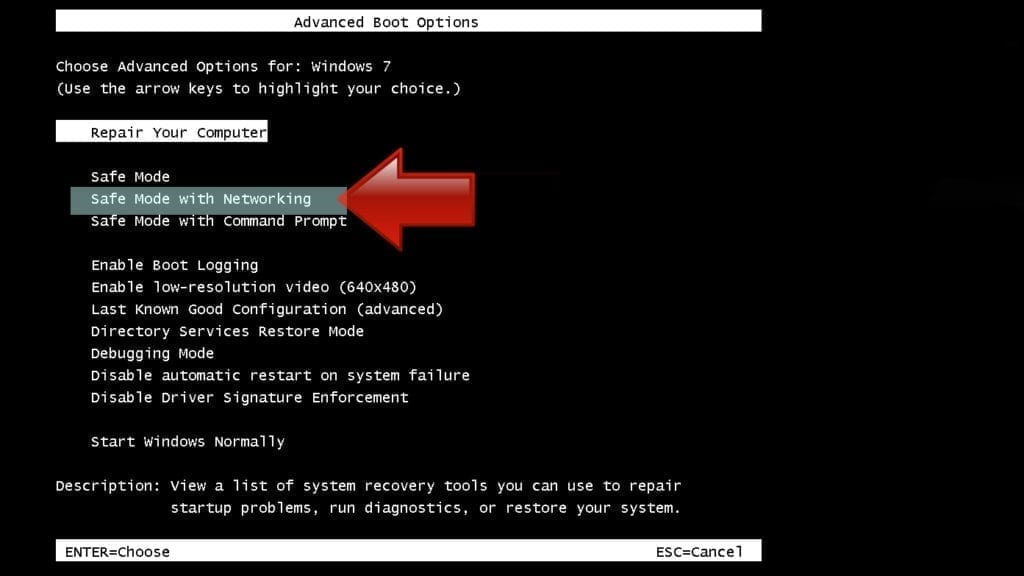
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
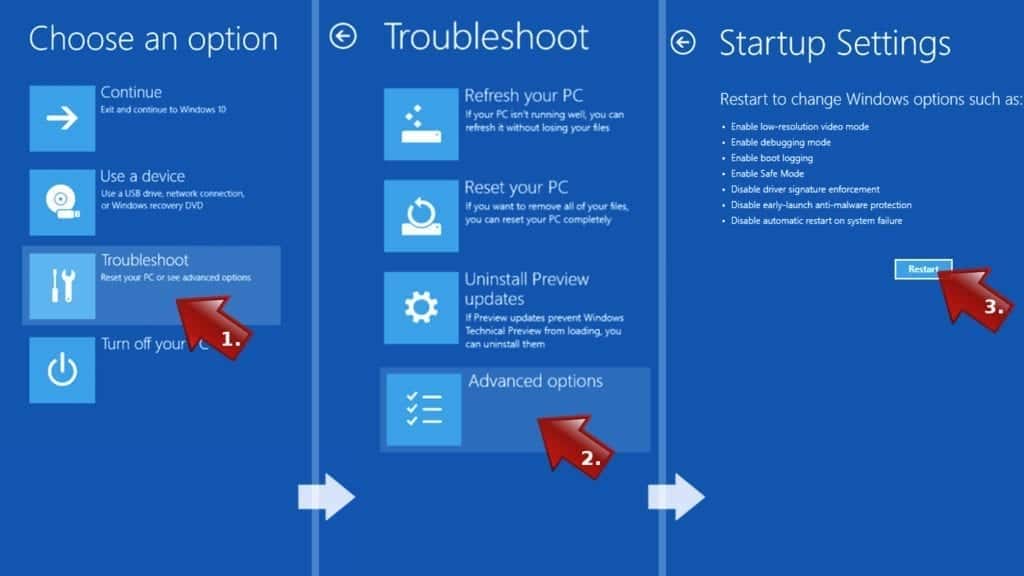
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
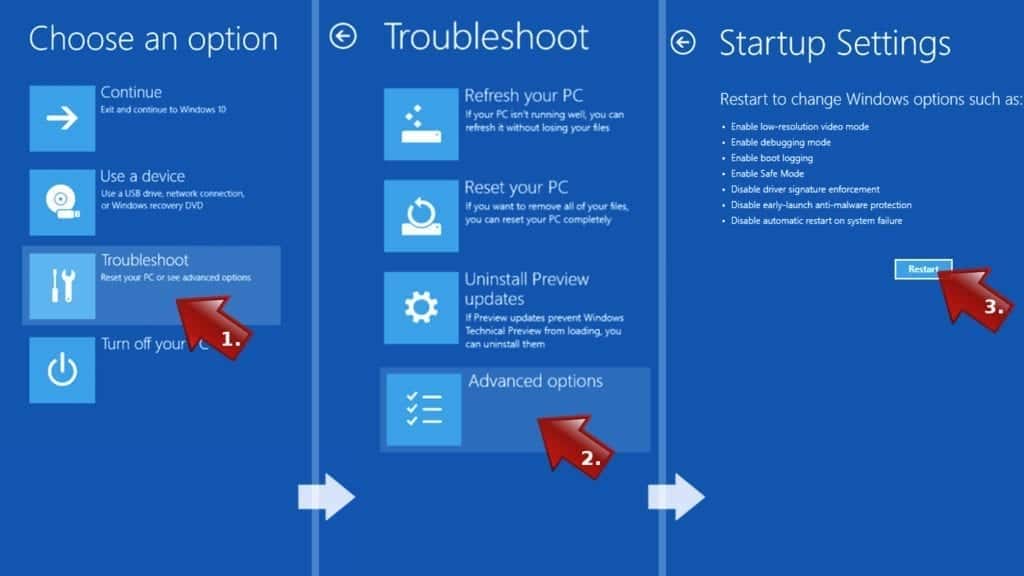
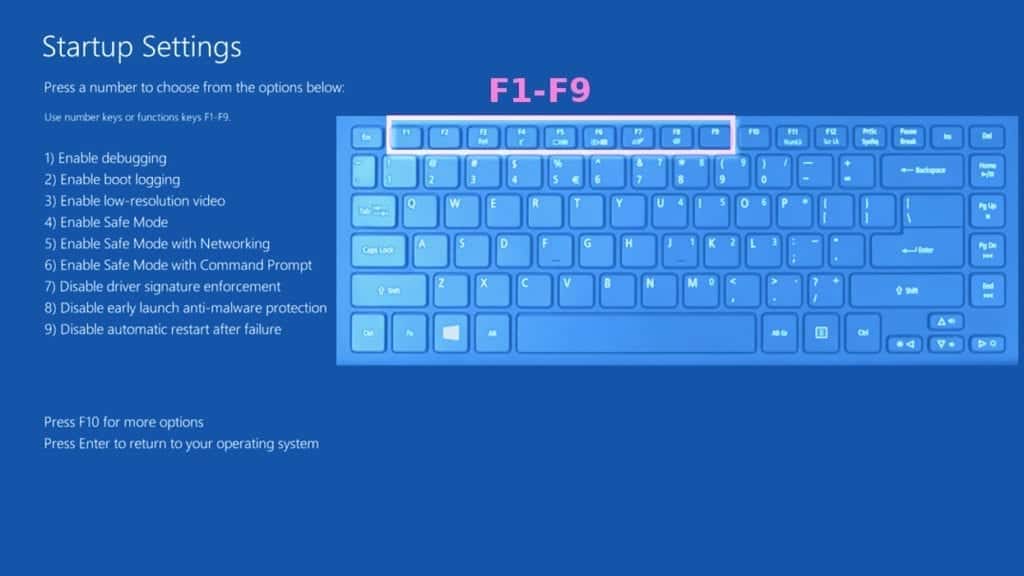
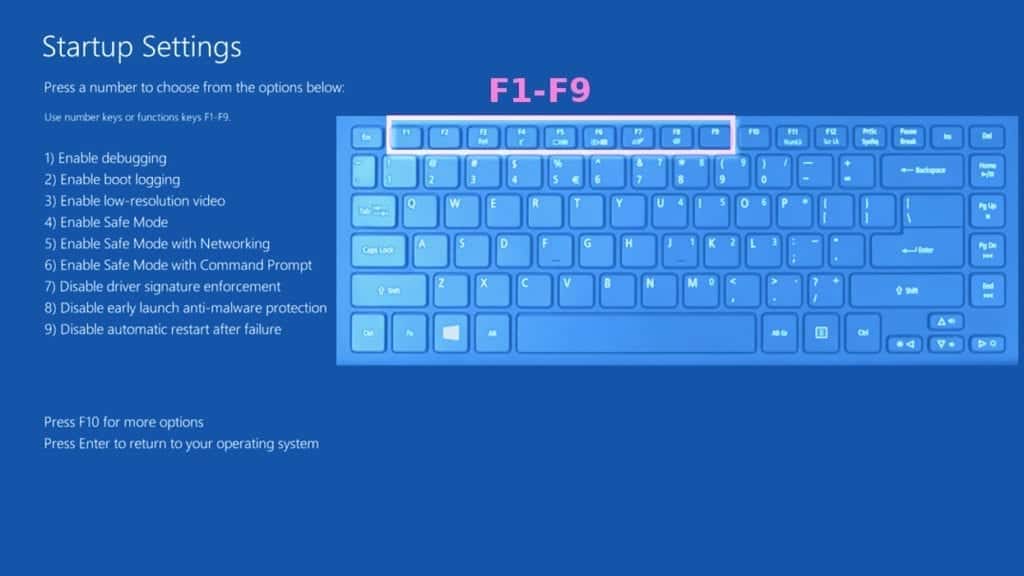
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove FOOP Ransomware files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
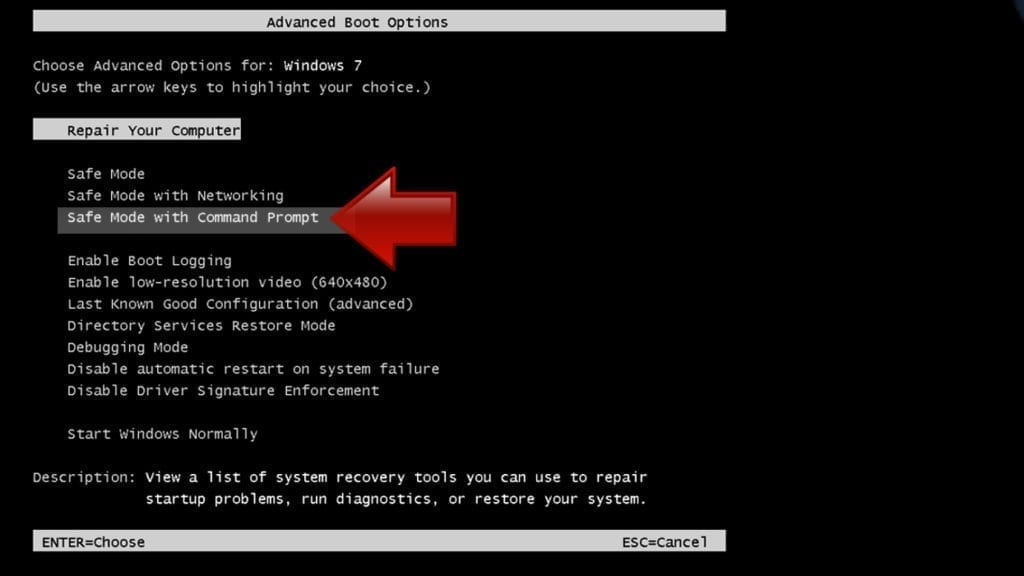
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
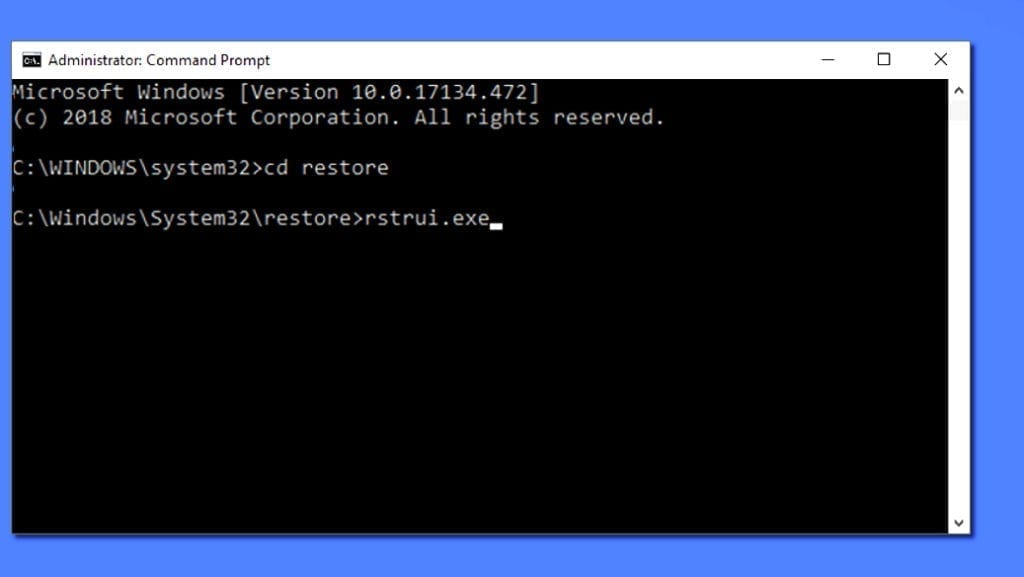
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
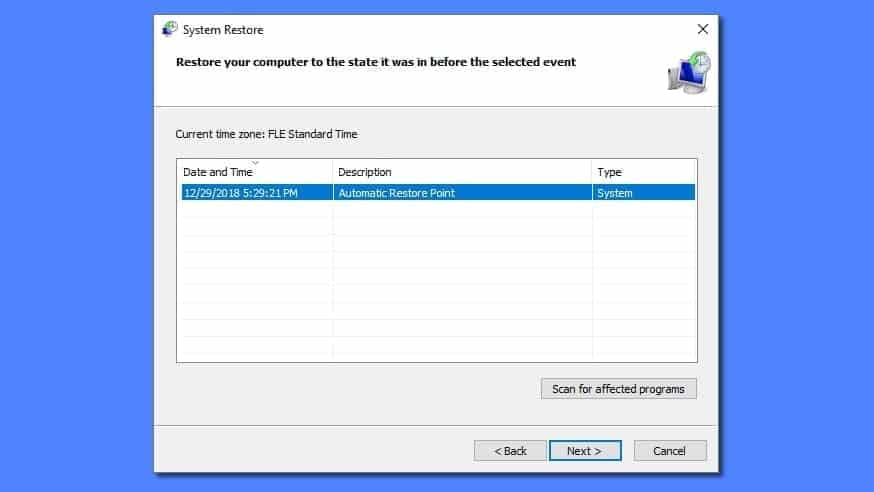
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
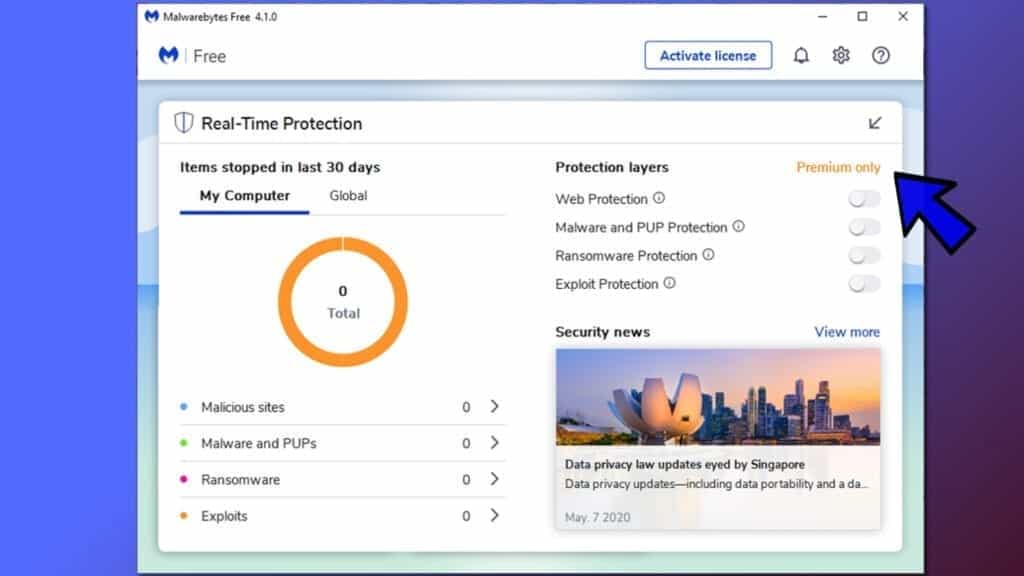
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
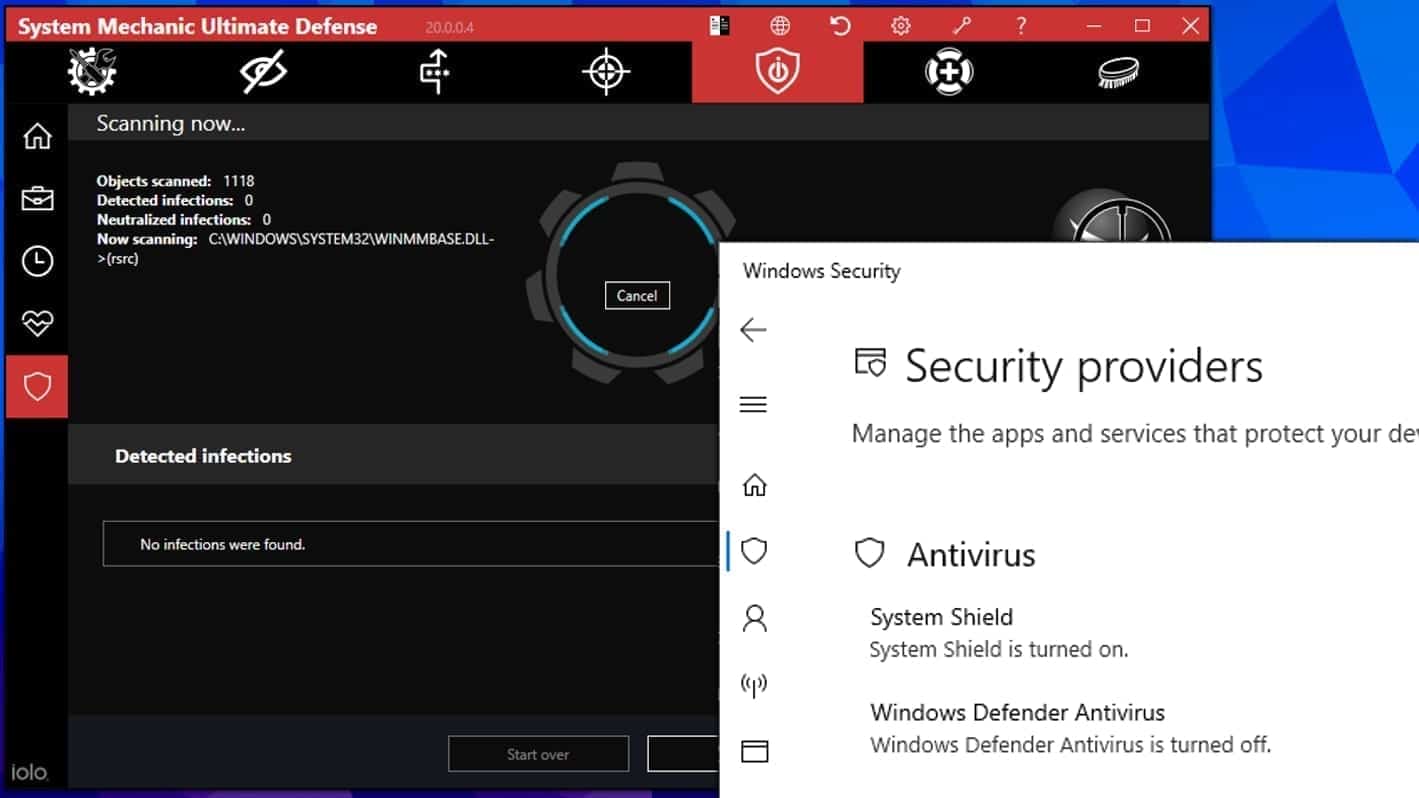
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Matt Corey is passionate about the latest tech news, gadgets and everything IT. Matt loves to criticize Windows and help people solve problems related to this operating system. When he’s not tinkering around with new gadgets he orders, he enjoys skydiving, as it is his favorite way to clear his mind and relax.
Is this system restore point automatically generated or it should have been done manually because I never created any. Also, does this actually work or it will end up wiping out all files?
The virus removes the restore points in this case, so you won’t be able to use them.