Nesa ransomware continues attacking victims worldwide
Contents
Nesa ransomware is a malicious crypto-virus that belongs to Stop (DJVU) ransomware family. The malware mainly spreads via malicious emails and, once executed on victim’s computer, encrypts all files with RSA-2048 algorithm, adding .nesa file extensions to them. After that, the malicious program leaves _readme.txt ransom note which contains instructions regarding data decryption.
STOP/DJVU ransomware is currently the most active ransom-demanding virus which produces new versions daily. The main indicator of a new version is a new file extension used to mark locked files.
In this case, it is .nesa file extension virus, and if you have been infected with it and cannot access your files, continue reading this article. We’ll cover data decryption and Nesa ransomware removal process in detail.

The aforementioned ransom note left on victim’s computer instructs to purchase Bitcoins and pay $980 worth of them to cybercriminals. If the victim manages to collect the said sum and contact the attackers within 72 hours, then the ransom price drops to $490. The attackers leave two email boxes to contact them:
- gorentos@bitmessage.ch;
- gerentoshelp@firemail.cc.
The ransom note suggests sending one encrypted file to the attackers via email and receive a decrypted file as proof that Stop/DJVU or Nesa decrypter exists and is fully functional. The note also contains a personal ID which is basically a long set of digits.
IMPORTANT: If your ID ends with “t1”, you may be able to decrypt your files for free.
The ransomware is essentially similar to Sodinokibi, WannaCry or any other malicious crypto-virus as it aims to extort inattentive computer users who either don’t have backups to restore their files or antivirus to keep their computers protected from malware. If you are one of such users who have been infected by this Djvu variant, you must remove Nesa ransomware virus immediately.
There is no way to decrypt files locked by the ONLINE key. You can only restore part of your files using OFFLINE key or a backup. See decryption steps at the end of this self-help guide.
Threat Summary
| Threat Name | Nesa ransomware virus |
| Threat Type | Ransomware (STOP/DJVU family) |
| Ransom | $490-$980 |
| Encryption Used | RSA-2048 |
| Decryption | Not possible. Recover files using a backup |
| Distribution | Infected emails, software cracks, software bundles, compromised websites |
| Removal | Remove using antivirus software |
Stop/DJVU ransomware distribution scheme
The said ransomware family is mainly distributed via untrustworthy websites, illegal software cracks, and even spyware bundles. Also, some Nesa victims have reported that they were infected via malicious email attachments. As reported by BleepingComputer, the ransomware can lurk in malicious KMSPicoActivator setup.
The only way to keep ransomware viruses at bay is to keep your operating system and installer programs up-to-date, avoid shady links or software, never open suspicious emails and have a backup. Besides, installing real-time antivirus is a highly recommended option. You can learn more about ransomware prevention with this guide.
Remove Nesa ransomware now and restore your files
To remove Nesa ransomware virus, use a decent anti-malware software. The described ransomware tends to install password-stealing Trojans on the victim’s machine, so we suggest staying away from manual removal guides in this situation. However, if you’re willing to try, use the instructions provided below.
After a successful Nesa removal, recover your files from a backup drive. You can also use the decryption instructions provided below the removal guide on how to recover files locked by offline key.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS

Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
Nesa ransomware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
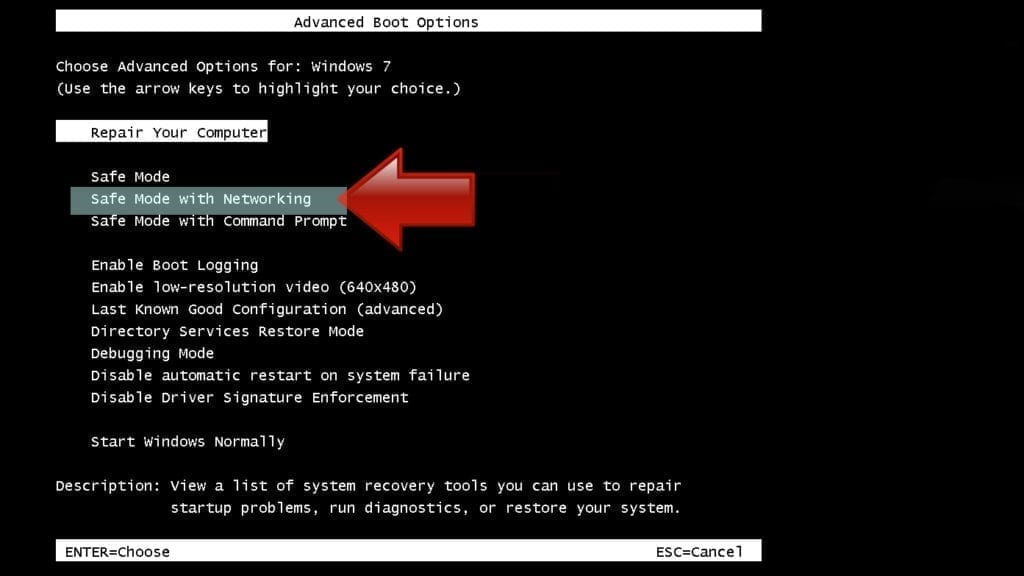
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

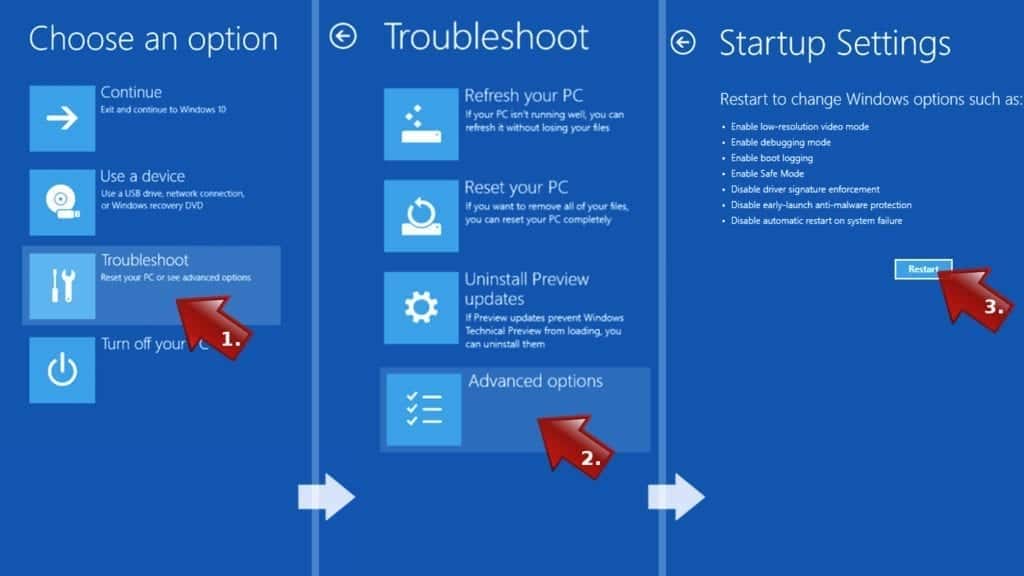
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
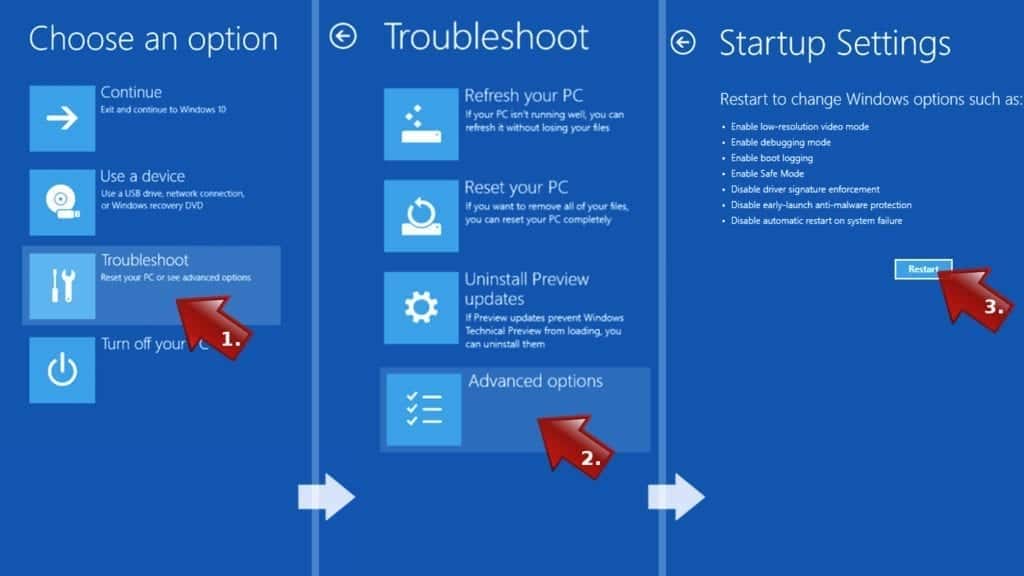
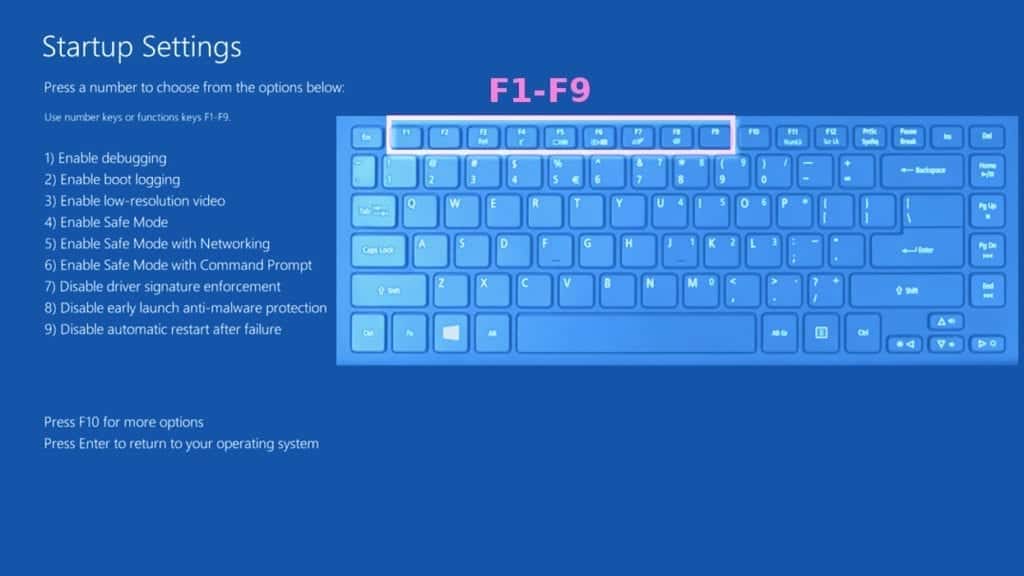
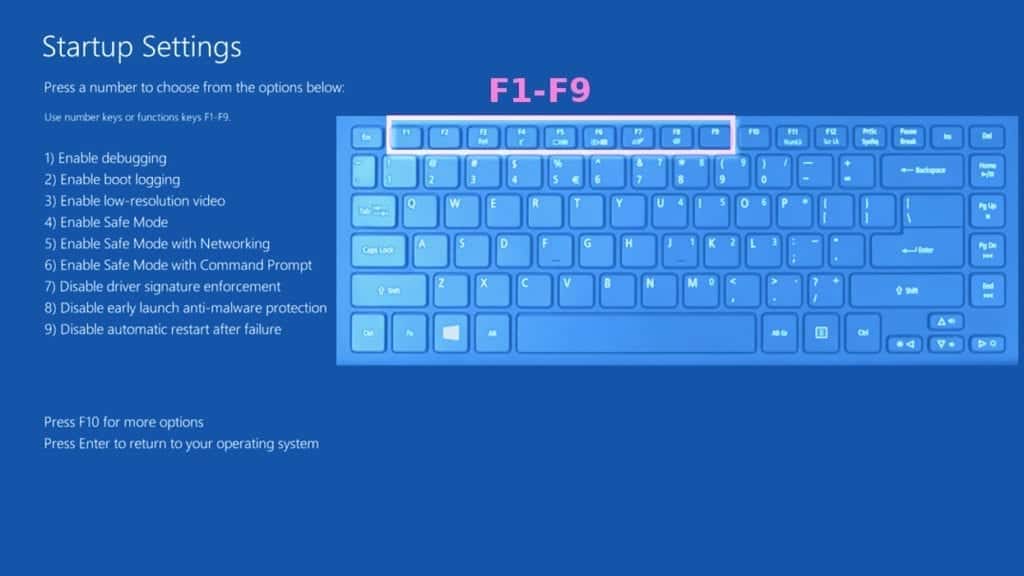
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove Nesa ransomware files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
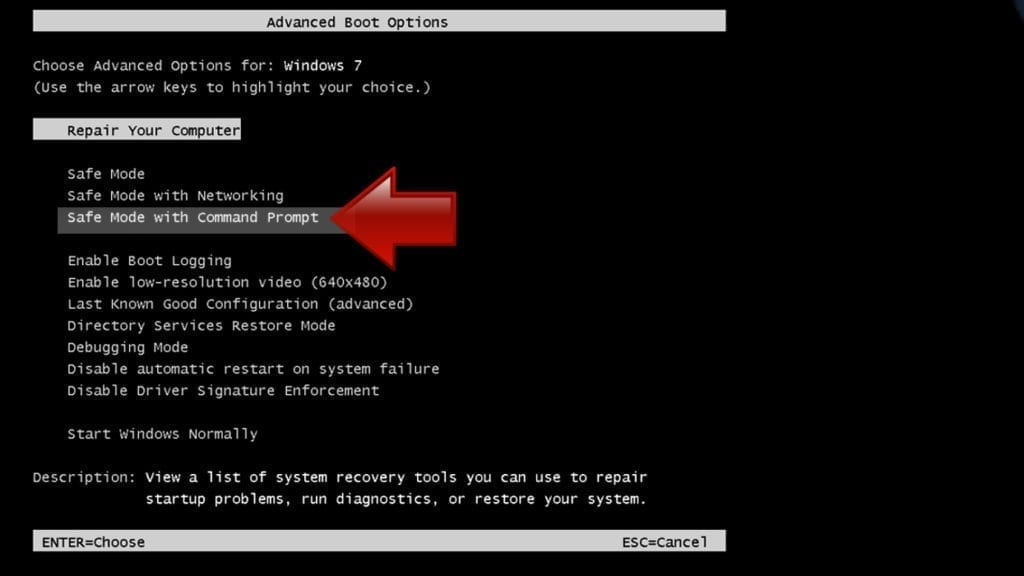
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
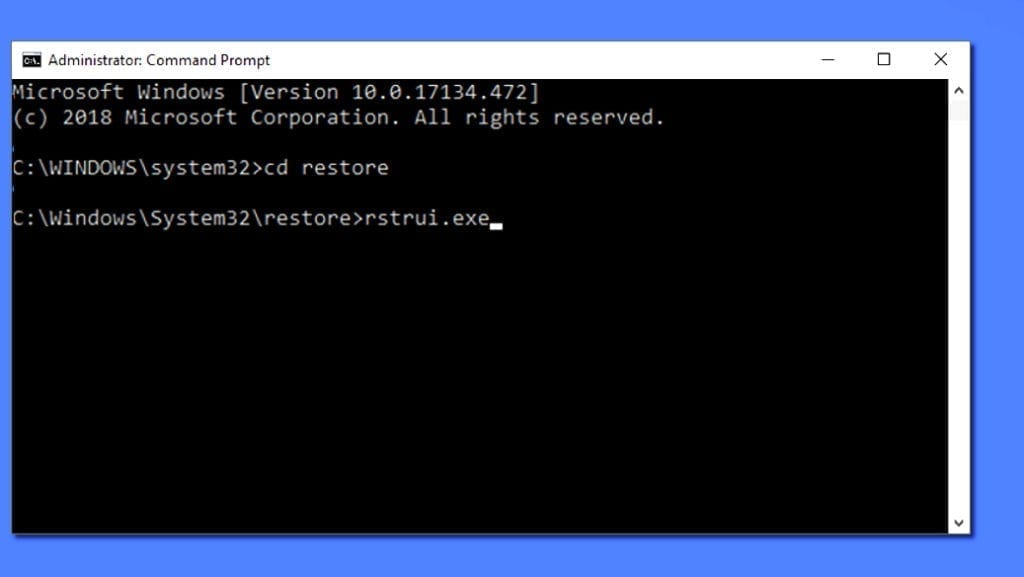
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
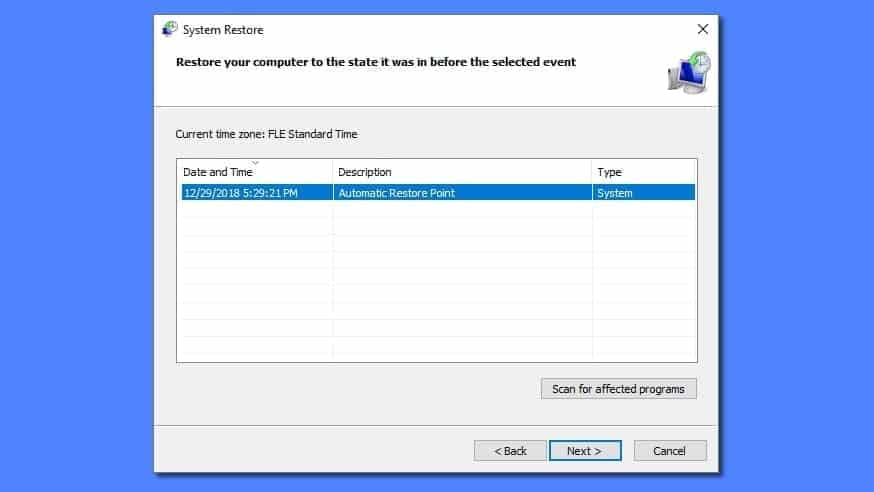
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
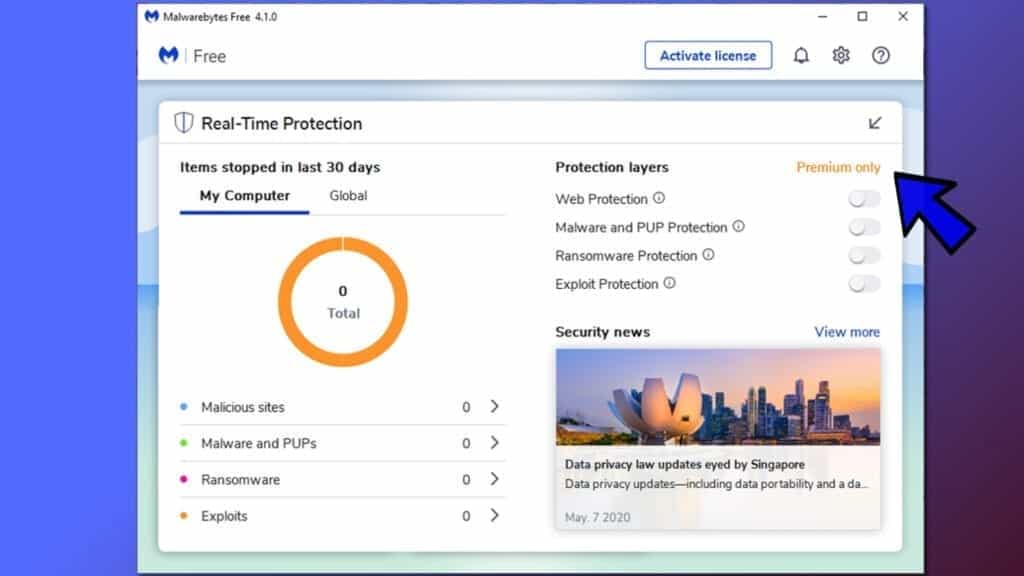
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
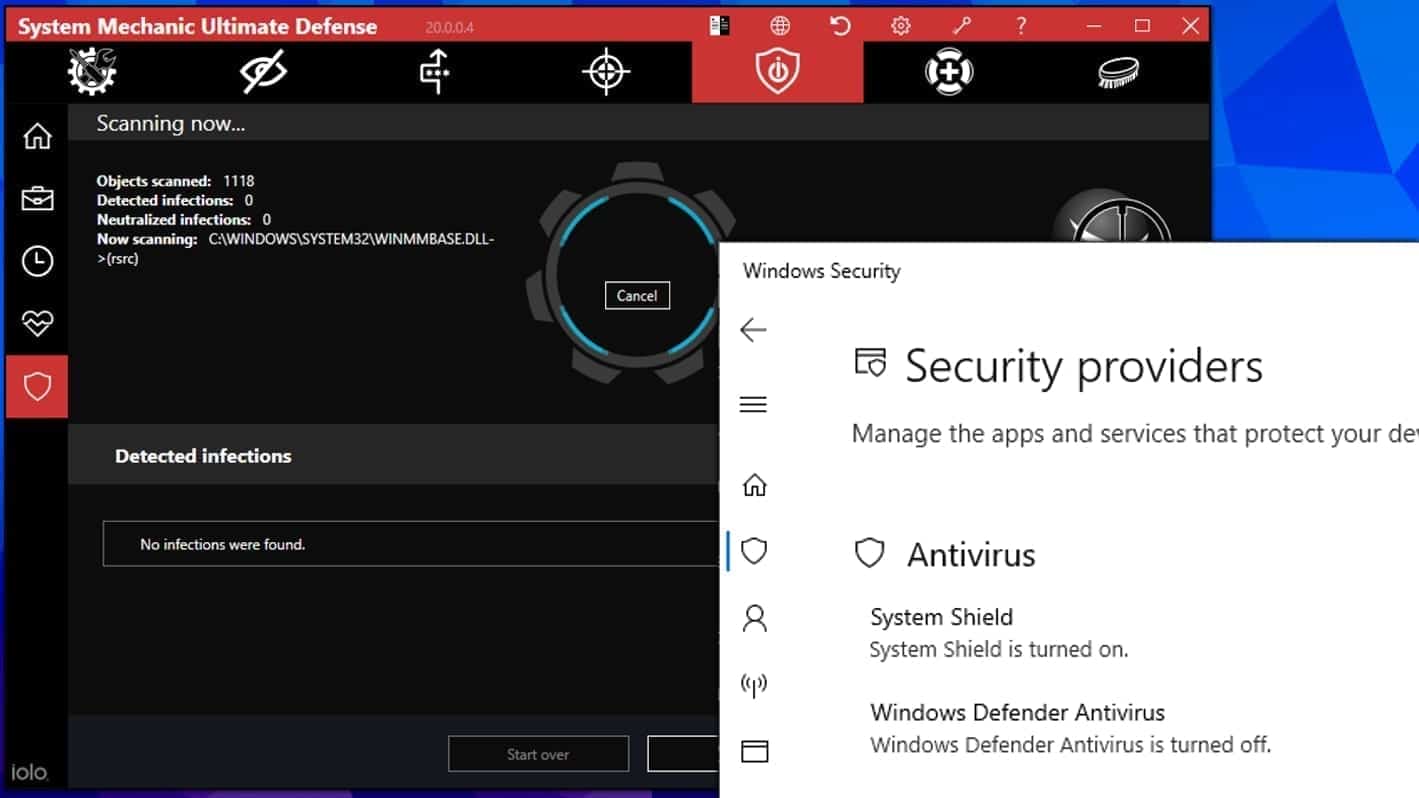
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
Nesa file decryption guide
The ransomware can encode files using either OFFLINE or ONLINE or both keys. You can decrypt Nesa files if they were locked by the OFFLINE key. The instructions provided below explain how to decrypt files locked by the offline key.
TIP: BACKUP all of encrypted data on an external storage device before you begin. Unplug it and put it away.
This is EXTREMELY important! Otherwise, the decryptor may corrupt data even more if it fails to work.
Note. If the decryption fails to work, it means your files were encrypted with ONLINE key, and recovery is not possible.
- After you create the encoded data backup, download STOP Decrypter from here. It is the original decryptor created by ransomware developers, but it is entirely safe file as tested on VT.
- Open the downloaded file.
- Copy the entire key (including the —–BEGIN PRIVATE KEY—- and —-END PRIVATE KEY—- parts and paste it into the Private key field in the decryptor.
- Fill in the next fields with your personal ID and the name of the ransom note (_readme.txt).
- To test decryptor on one file, choose Decrypt File.
- If you press Decrypt Folder or START, it will start decrypting all files on a computer.
The OFFLINE .Nesa key:
-----BEGIN PRIVATE KEY----- MIIEvwIBADANBgkqhkiG9w0BAQEFAASCBKkwggSlAgEAAoIBAQDRkvpXT0muaEiD ZZkX4NBi/katwWnoQzi1GKK/AJovFUvDwu/Z1HFDz5muFF0OQHYl//D9vsAx2hG1 /qUSmCK/k81JtHTosrOmFIv5Va62e65eZIyMMu4qOUKJrZLfD4COCHlTR/SzxYD/ 7GKcOhbdK4rCiihZOf1EoUsbuNHM/xl0tiGTjfAUdrI/qlNDZ/bt4WpzkqwpLJm+ A91viz7aAE3kxiZZhae4n3cz6YtNNmXshWSbO9nW2SaNeNNdFxihCVT5RLdja9Iv p9ge2MMpH9pbgZoUt90JKARbKUc/jgDa5KhLLuGQRP+GWx+bSMZPggzbZtiOmj8g Mh3ovTVJAgMBAAECggEBAIc7UUDfj8rzzb7D41rOHYmTTKY4RQ+zuLba08FuMQ+q rT3/3udvtzqrjh4PU9CrddGlaqtB2CES9xS54WizNNDsHa6uvDWfgl7rqTrVuCxW eLi+JxcckiQ62J2gnEJFbY25GBjOOK98BXae4S6wKSrEOwC3R7vzuGL9tUqJIxAk bFKBZbSG5pbgByaF6Li4Bq/i0KhFtAaUSE6TzLPXlejN9DwWwkOcnNiq5eLShUYT 2XuP70RzJUc+c5WSTMk2M15anig9N4i69lii++r3OjTqMIzZ8voPAAgO4hD2/QXx x37Onh6DA6jntr+BywOSUvsU5ZpFTpgRv0ZDcI7VqIECgYEA+a5PT7q9zWPu0SRV bCPVsxPsZXPEaMSCiKfNeFnUvw7ZPCrXggSkhW42dbaNhOSvF7puiMKVzkTta3f4 Mjpq7JssP63niz23SEsd0hNlCGxzHVSTGSxioMo0nsEwly1R6mAGLYphFOcGSAg/ fdb/mwFYJGrGJEnJAfwEIFJv/BkCgYEA1uDQq+EaTzJmj2wj/QcGjUtD2iCSUy3j vviDUOkPVkgivyrRyEgTrCvjug2T3NpXWgQMnHBQBoHA2rOkE7oHxv9R3BnbAOzN +a/K0ukRHAX2jY+Ipy2ib6cPkcsk9Sxc+WnEWkl4A1mEW/qv+lWi6QKUU2lsrjT3 jMUla3bMKLECgYEAvKEb+jgyvMEK46Z3gsNv52Ld7aeQczZDB8r+SDZVrCIjrHkR Z4DqaoPhUP0h3YyHW33VlCyt0K/yTobMU+YecbKps1JG48M0fMGDPfq5EawdK8OB fjsyKBebuXRqqUvr3w28nRs2TPxcmn7guMl9QjW5yYmBOFkmKwGifGjLgcECgYBi msPnO+MQ2LYLtrpFEIZHLHS0kiHTnclXBz9rT6fEFlIrm4CtAbZVWcakyDpELMXM /vKyjy+J7N0M/0aZ7tJG1T9BW3QOVpymqa7PXjiFvY7Io0c4QE68IdOZObl58KOx qIF8VR6HmvqMItvCaq3Zc1+Rb116C8BVjtp/GALT4QKBgQDrQ7jZJz67TazlbdpD mNJ0OLHNmWY0Obpy4H3+QTXnNeZw7fML06ed9ybYIsulTHiA/FMvZL54ft9yaLBb 2+Ddt0dt17YC3t5XVaeD6M1eqJpPZw5XsEpNztz7AxcOJ7zaevNMtDEHeEPt3s6I Uz528lPVGvjO1bDkkD2wJ+TAwA== -----END PRIVATE KEY-----

Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
I have a Question same case came before me and after taking many efforts i was unable to decrypt so i formatted drive or we can say completely wipe out the data. now the question is if i recover it can i get the decrpted form data or same encrypted type.
decryptor looks like was working, but there´s none file decrypted lmaoo somebody pls help me to recover my files, im using stop Decryptor and decryptor 2
nothing works to decrypt Nesa Ransomware
Decryptor won’t work if your files were encrypted with online key, there is no point in even trying.
trying to insert your key, what is the password ?
my all data is effected by Nesa can u plz tell how to decrypet the files. thanks for your cooperation
i need recover data, i no have a backup. plrase help me.
is there any decription software ?
or any other way to recover the data back.
is there any decription software for nes virus plz rply
This has some wonderful guidelines regarding the recovery from ransomware attacks.
Thanks for sharing the article.