Montana ransomware aims to encrypt your files
Contents
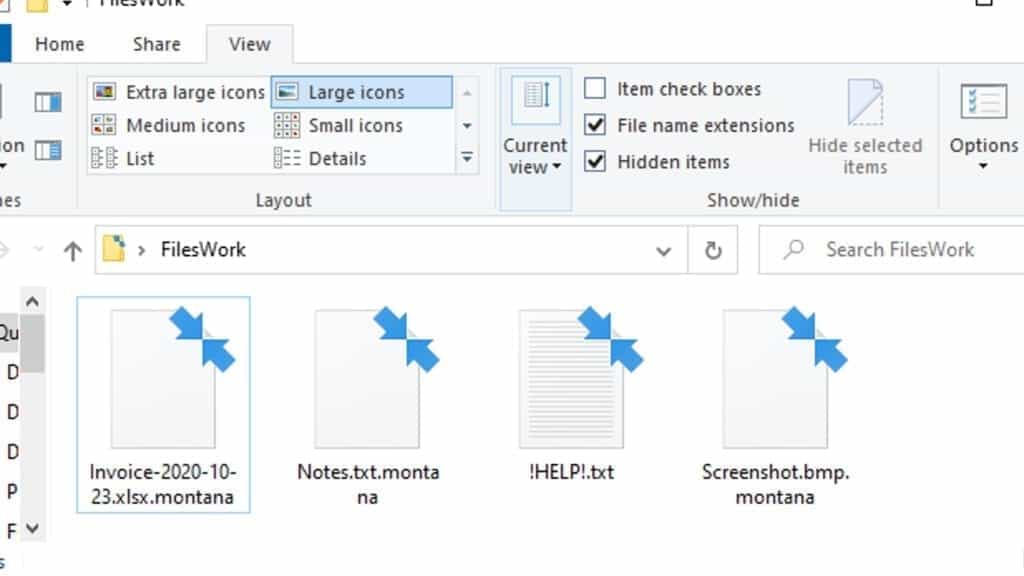
Montana virus belongs to ransomware category and is recognized as a variant of LeakThemAll. This virus variant encrypts all files on the target system and marks them with .montana extension. For example, a file that originally was named 1.jpg becomes 1.jpg.montana after the encryption. Following a successful attack, the virus leaves ransom notes called !HELP!.txt. The note instructs to contact the cybercriminals via provided emails and pay a ransom to get file decryption key. This virus can also belong to extortionware category, since it promises to leak ‘stolen data’ if the victim plans not to pay the ransom.
The primary aim of viruses like Montana ransomware is to infect as many computers as possible, make all files on them inaccessible by encrypting them, and collect ransoms from the victims.
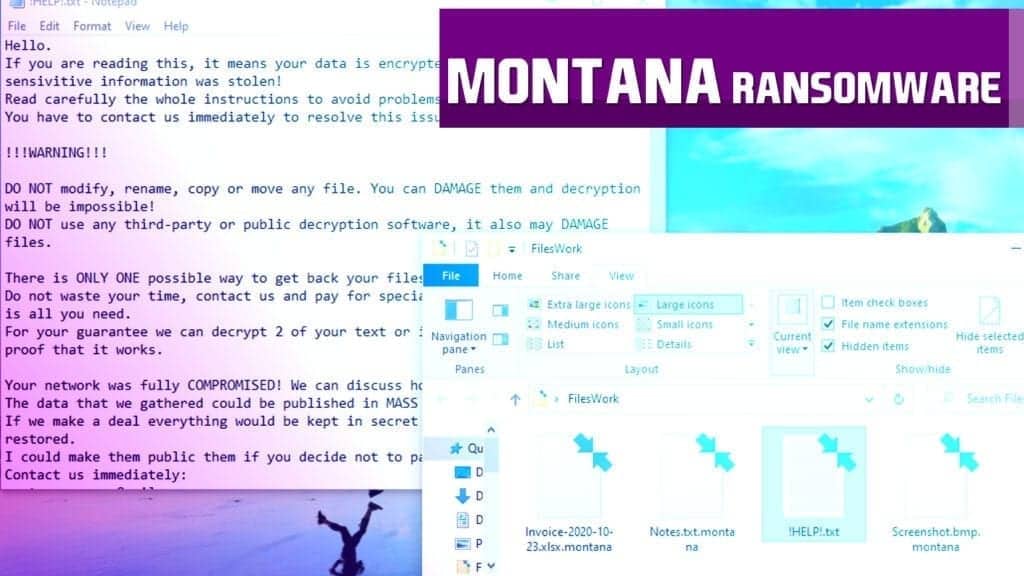
Contents of the ransom note explained
The ransom note left by this virus, called !HELP!.txt, is a file generated by the virus that contains a message from the cybercriminals who developed the program. The message states that the data on the computer was encrypted and that some sensitive information was stolen (transmitted to the criminals).
The note then warns the victim not to modify the files, also not to rename or move them. According to the criminals, this might make file decryption impossible.
The developers of the ransomware claim that there is only one way to recover encrypted files – to pay a ransom. To prove that they actually have the decryption key and software, they suggest testing them. The victim can send up to 2 encrypted .montana files for free decryption.
The note then suggests that the network was compromised and the criminals can provide recommendations on how to secure it as a “bonus”. However, the further lines state that if the victim refuses to pay the ransom, the criminals will publish the stolen information to media. Finally, the note provides victim’s personal ID and two contact emails – montanarecover@mail.ee and montanarecover@cock.li.
If you have been hit by this virus, we recommend you remove MONTANA ransomware from the system using malware removal software. To repair damage caused for your computer system components, scan and apply fixes with RESTORO.
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
| Name | Montana ransomware |
| Type | Ransomware; File Locker; Extortionware |
| Family | LeakThemAll |
| Detection name | Gen:Variant.Ransom.Hermes.140 (Bitdefender), Gen:Variant.Ransom.Hermes.140 (B) (Emsisoft), TR/FileCoder.hiflh (Avira) see full list on VirusTotal |
| Executable file | <random>.exe |
| Ransom note | !HELP!.txt |
| Criminal contact | montanarecover@mail.ee and montanarecover@cock.li |
| Extension | .montana |
| Distribution | Infectious torrents, malicious email attachments, fake software update ads in untrustworthy websites |
| Removal | Remove malware using anti-malware software. To repair virus damage, install and use RESTORO. |
Ransomware-type viruses are extremely popular extortion tools used by cybercriminals worldwide. The most active viruses of this kind nowadays is STOP/DJVU family (MMPA, FOQE, NYPG) and DHARMA (FLYU, LCK). We never support paying ransoms to criminals, because it simply helps to grow this cybercrime industry, which is why there are so many viruses if this kind nowadays.
Ways to avoid ransomware infections
Computer users should beware of ransomware distribution tactics in order to avoid installing these viruses by accident. That said, the first method you should know is malicious email spam including attachments. The criminals might try to disguise themselves as representatives of well-known companies such as DHL, TNT or eBay and offer a fake “shipment tracking information” or invoice documents. Unfortunately, as soon as the victim opens such attachment, the malicious script inside of it will download and execute malicious payload on the computer.
Another ransomware distribution method doesn’t even involve targeting the potential victims via email. The attackers can simply insert the malware into a fake software crack torrent. Many crypto-malware victims have reported downloading similar viruses via software cracks, keygens, and similar files. We would like to remind you that if you want to obtain a legitimate and secure software version, you should visit the software vendor’s official website and purchase it from there rather than searching for unconfirmed and illegal spin-offs online.
Needless to say, one of the best ways to avoid ransomware damage is to keep your antivirus up-to-date, avoid visiting suspicious domains, clicking on shady ads and downloading illegal files via peer-to-peer file sharing agents. In addition, you simply must create regular backups for your files, or at least to the most important ones (work files, family memories and similar). Data backups help to recover lost data in case of an unexpected malware attack.
Remove MONTANA ransomware immediately
Our team has prepared in-detail Montana ransomware removal guidelines which are provided down below. You must follow each step carefully to ensure a successful virus elimination. Make sure you use a robust malware removal software to cleanse the system from malware remains.
Remove MONTANA virus safely in Safe Mode as explained below. Do not forget to repair virus damage caused by this ransomware variant using RESTORO, a well-known PC repair and maintenance tool.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS
Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
MONTANA ransomware virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
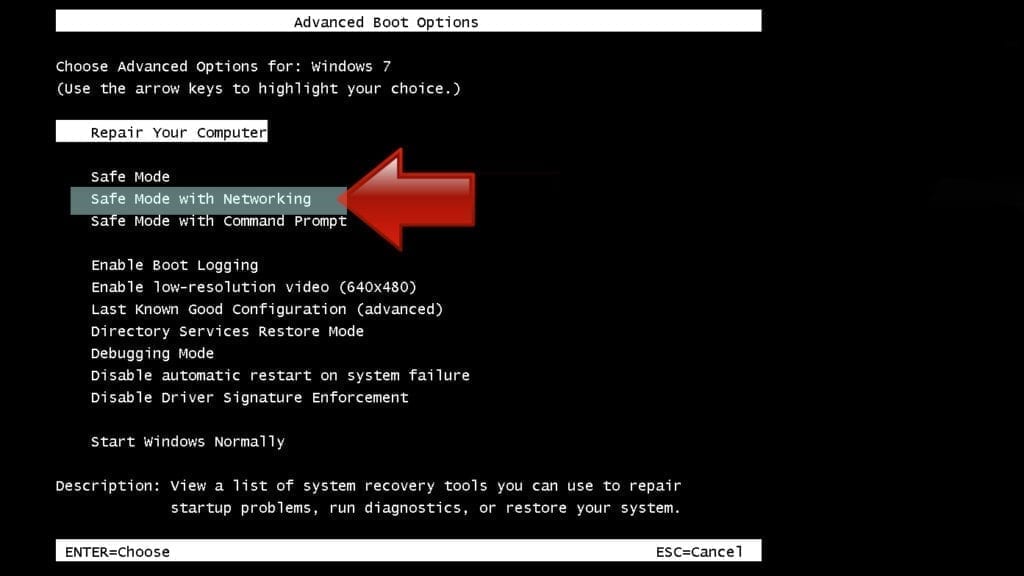
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
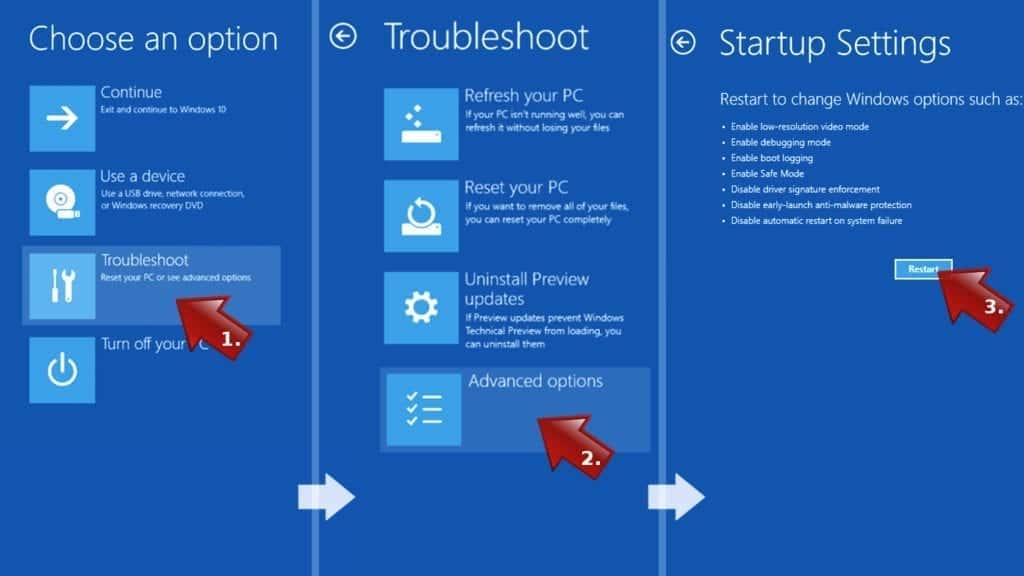
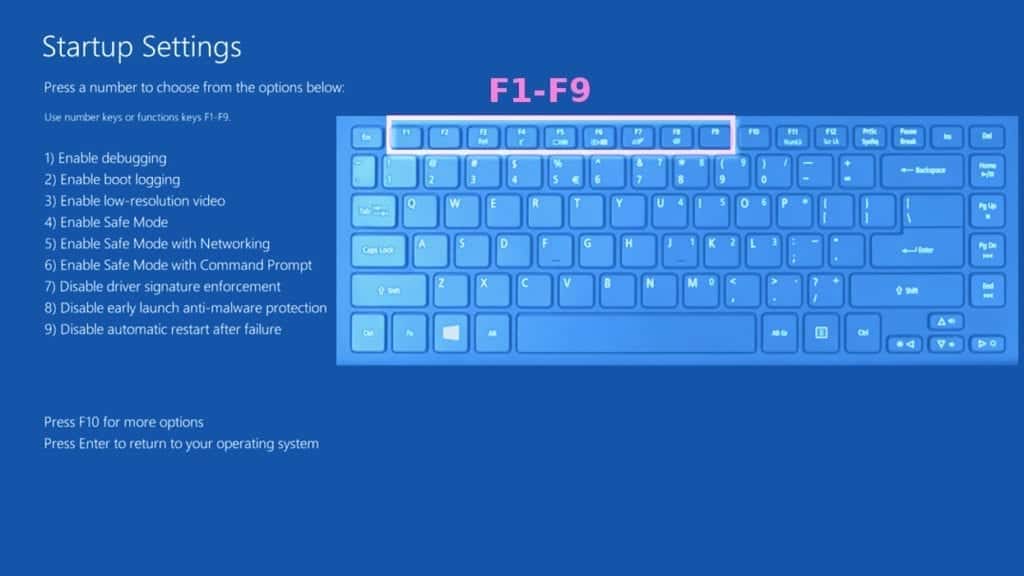
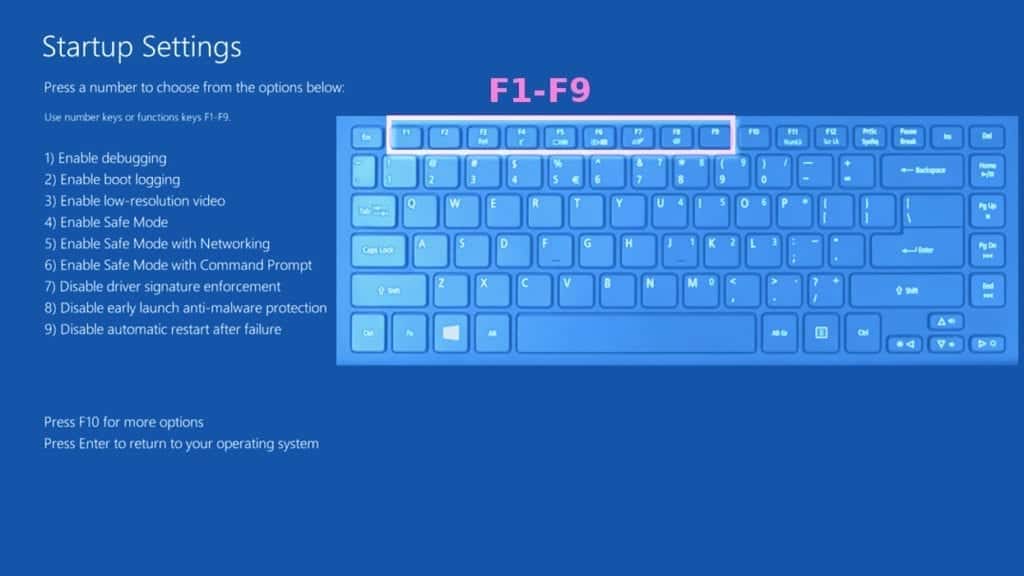
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove MONTANA ransomware virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
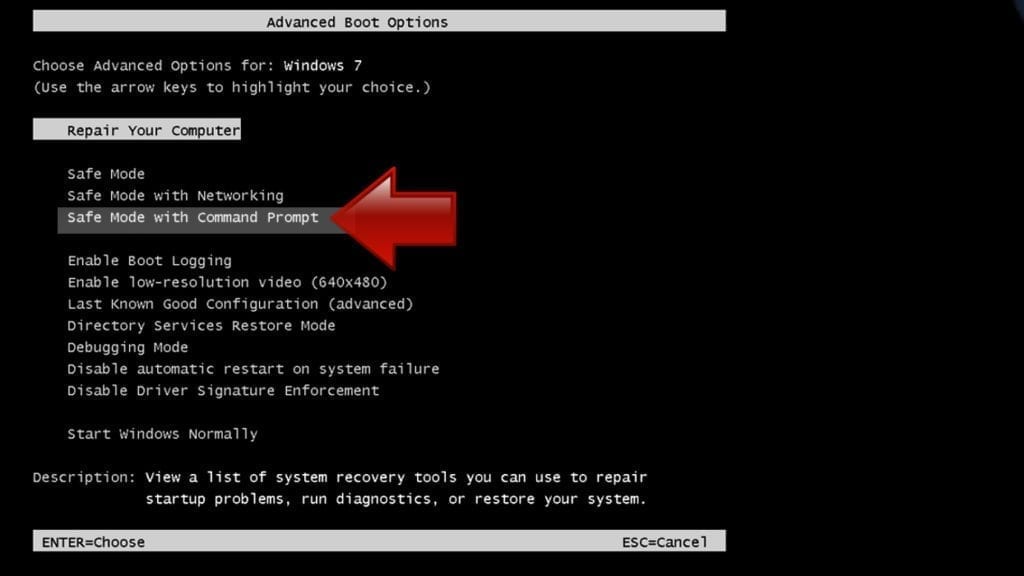
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
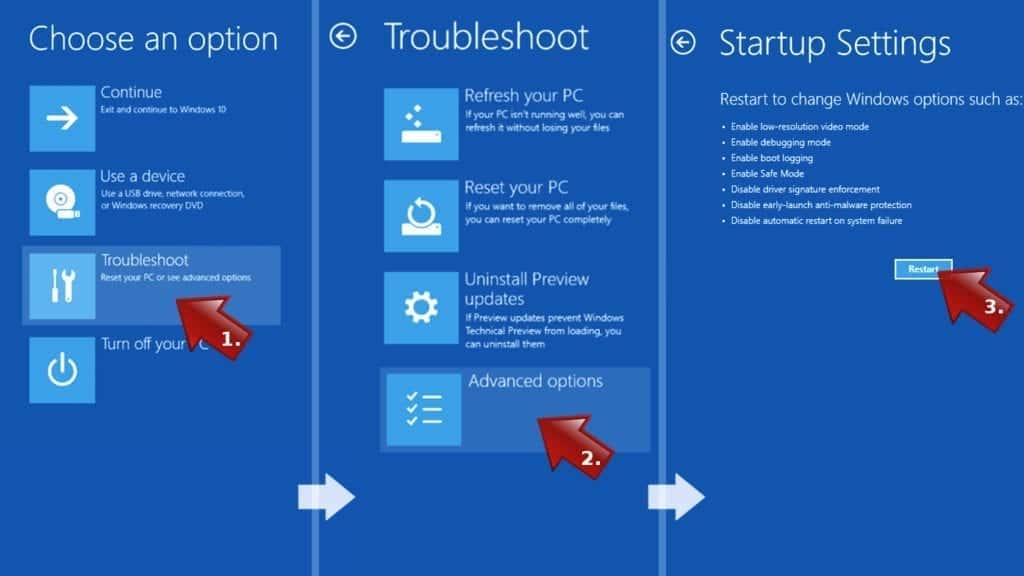
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
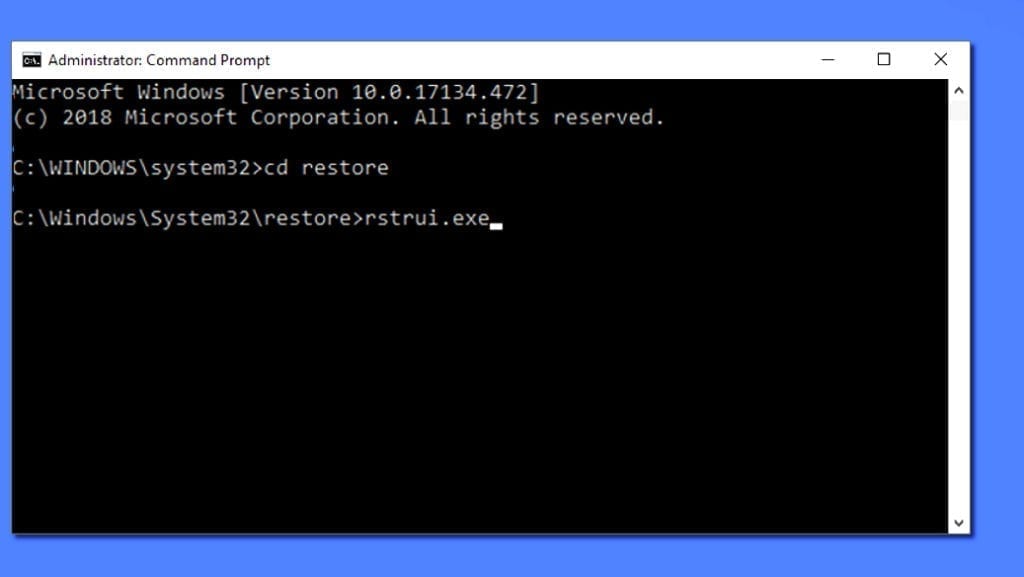
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
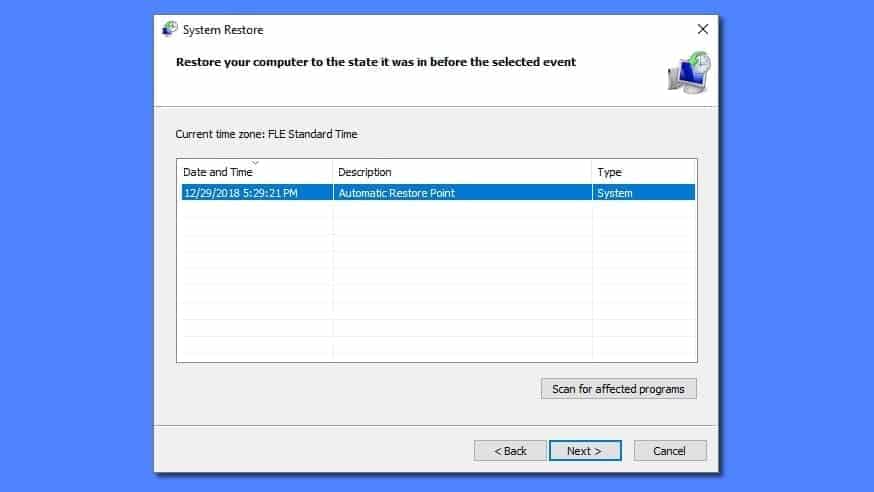
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
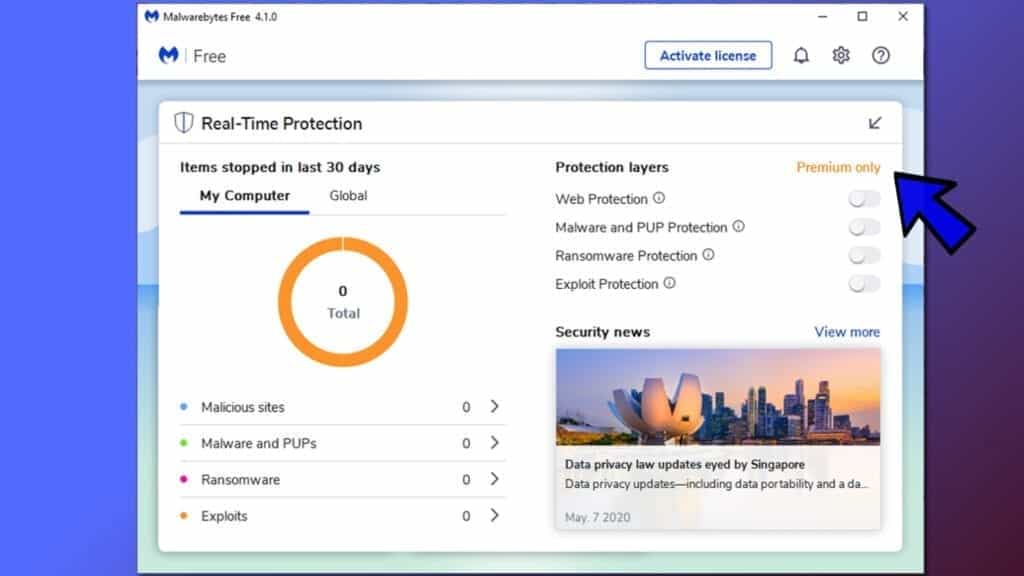
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
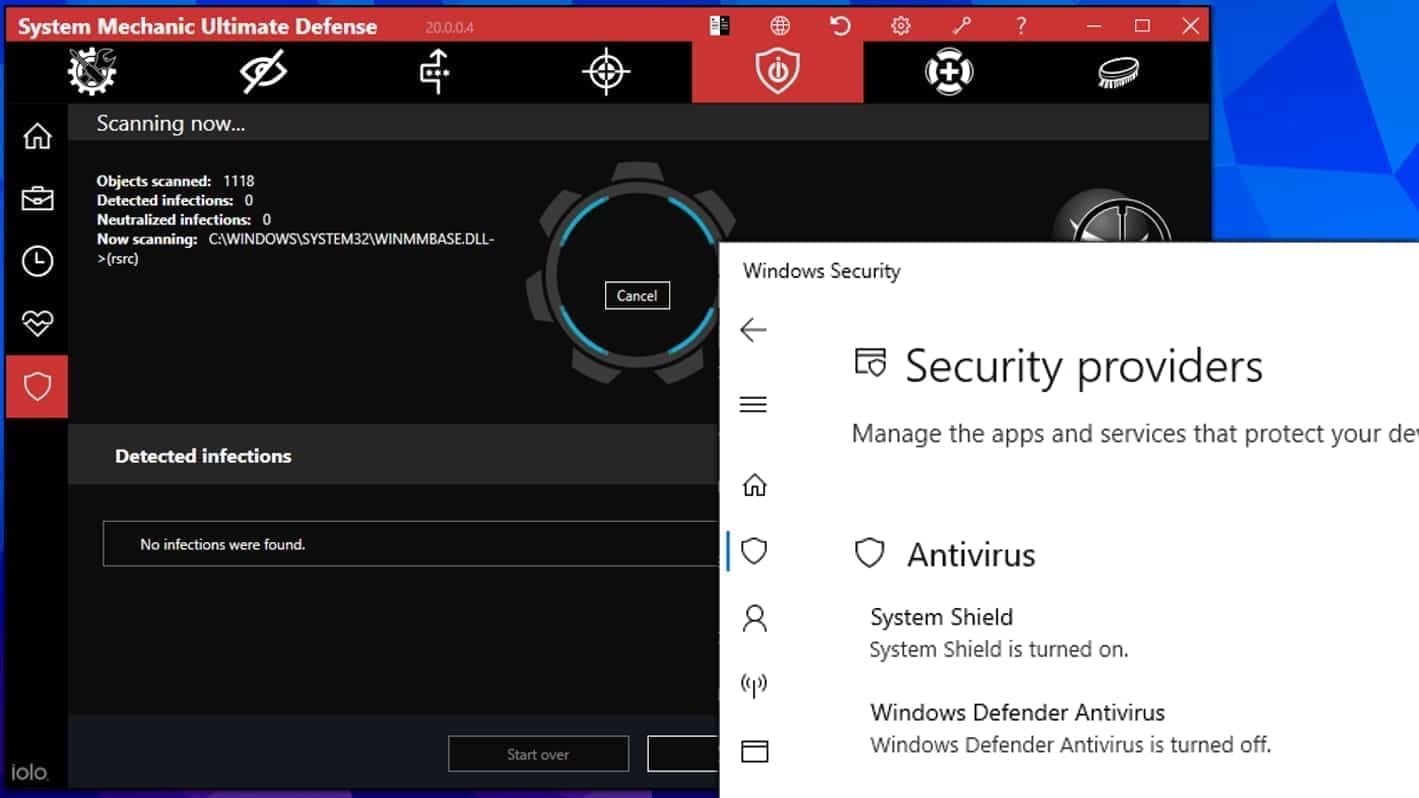
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
Leave a Reply