LCK ransomware aims to encrypt your files
Contents
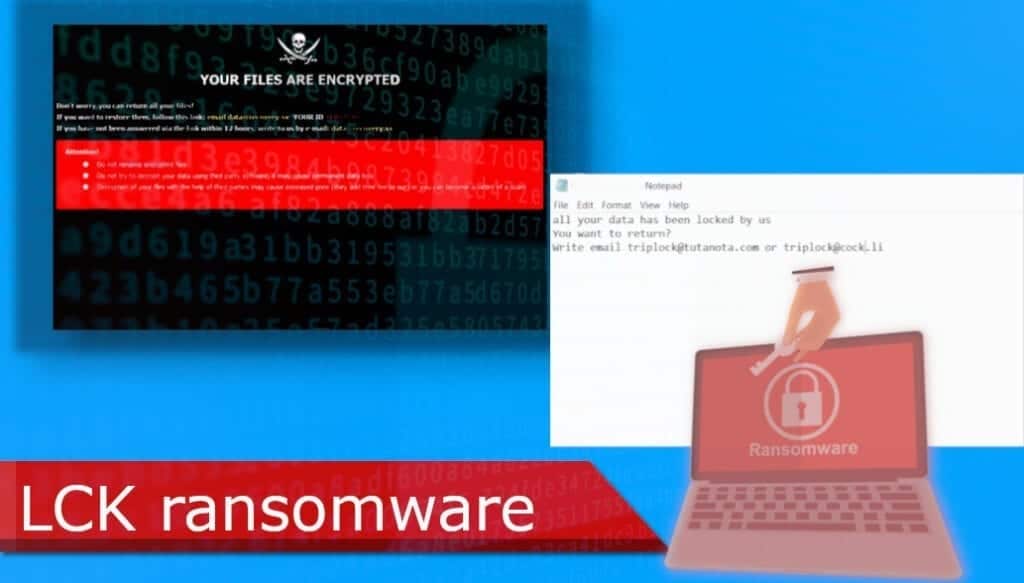
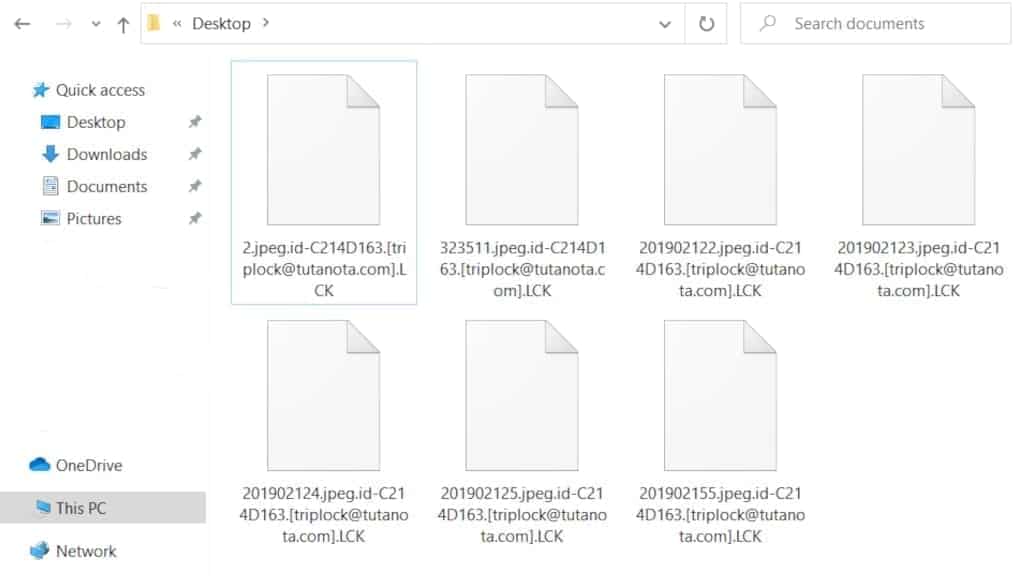
LCK is yet another type of Dharma ransomware that uses high-grade encryption algorithms to deny access to your files. This virus is a ransom-demanding type which means that its main goal is to ger financial benefit from the encryption. Infected files can be easily identified since their names are appended with the victim’s ID, triplock@tutanota.com email address and .LCK extension. For example, a file named A.doc is changed to A.doc.id-A423R236.[triplock@tutanota.com].LCK. In addition, after the initial changes to your system are made, a ransom note called FILES ENCRYPTED.txt and a pop-up window appears that is containing certain cyberattack related information.
In this tutorial, we’ll cover all the essential information about LCK file virus and what you need to do to recover after such cyberattack.
Irreversible changes made to your files
If a user opens the ransom note it greets him with an unambiguous message – his files have been encrypted and there is no possible way to retrieve access to them. Hackers offer a solution – the user is urged to contact them via provided emails (triplock@tutanota.com or triplock@cock.li) and to pay a certain amount of money. After these actions are made, the victim supposedly will receive a decryption tool to revert the changes that have been made to his files.
Unfortunately, just like other Dharma malware, LCK virus possesses a really frustrating characteristic – it uses high-end encryption ciphers. For this reason, the options on how to regain access to infected files are quite limited.
The first theoretical option might be contacting the hackers and paying the ransom. However, we strongly recommend against this course of action for one simple reason – cybercriminals cannot be trusted. There are numerous cases of victims being scammed even after the payment is made. Paying the ransom will expose you to extensive and unnecessary financial damage.
The second and more rational option is to completely remove LCK ransomware from your computer and then recover the files from a backup. For this reason, we highly recommend you to do regular backups since anyone might be exposed to a cyberattack at some point. It is important to mention, that you should run files from your backup only after complete removal is done since the virus might infect those files as well.
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
| Name | LCK ransomware |
| Type | Ransomware; File-encrypting virus, File Locker |
| Family | DHARMA/CrySiS |
| Versions | XATI, LINA, LOG, BLM, DATA, FLYU, FRESH, DME |
| File Extension | .lck |
| Executive file | <random>.exe |
| Detection names | Trojan.Ransom.Crysis.E (Bitdefender), Ransom:Win32/Wadhrama!hoa (Microsoft), Ransom.Crysis (Symantec), W32.Ransom.Gen (Webroot), Win32:RansomX-gen [Ransom] (AVG) see full list on VirusTotal |
| Ransom Note | FILES ENCRYPTED, info.hta |
| Contact emails | triplock@tutanota.com, triplock@cock.li |
| Damage | Once executed on the target computer system, the virus scans the whole file system and encrypts all files belonging to the victim. Additionally, the virus deletes Volume Shadow Copies. |
| File decryption | Try recommended file recovery tools. We do not recommend paying the ransom to attackers. |
| Removal | To remove this virus, scan with well-known anti-malware tools. To repair virus damage on Windows OS, scan with RESTORO software. |
Ways used to distribute file-encrypting viruses
Generally, there are a few ways that could be used by malware developers to proliferate their viruses. The most used LCK ransomware distribution method is malspam campaigns. In principle, it works like this: thousands of deceitful emails are sent to random people every day. Developers of this social-engineering scheme ten to create all sorts of fraudulent messages that encourage the recipient to open a link or a file inside of it. If you open that file or link, your PC might get infected – especially if it does not possess sufficient cybersecurity measures.
The other common way to distribute this kind of malware is to proliferate it through illegal software downloads. Let us face it – most of us, at some point in the past, tried to download something illegally – piracy is an ever-growing problem that traces its roots back to the start of the internet. It is tempting to obtain a crack, keygen, or some sort of software activation tool for your pay-to-use programs. However, you should always keep in mind that the danger induced by this course of action might far outweigh the benefits.
There are other ways that could be used to distribute viruses like LCK – software bundling, adware campaigns, etc. Software bundling is a software-spreading scheme that uses harmless or even beneficial programs (that are usually free). Potentially unwanted applications (PUAs) are attached to the downloaded software and if the user is inattentive, it might slip through the installation process. Adware campaigns use intrusive ads, pop-ups, etc. to provoke interaction from you – once you press on them or allow notifications, it might install a browser hijacker. Browser hijackers make changes to your default browser settings in order to promote their fake search engine.
To avoid dealing with this kind of problem we highly recommend you download only from official and trustworthy sites. In addition, always pay attention when receiving suspicious-looking emails and ads. And most importantly – create regular backups. This will prevent you from losing your data.
Removing LCK ransomware from PC
It is important to understand that if you have been affected by LCK virus, you need to take immediate action to negate all of the potential damage that might be done to your system. Even though your files might be encrypted and irretrievable, this ransomware might do more extensive damage, especially if you try to restore files from a backup. Having this in mind, we recommend you use highly rated antimalware software to remove ransomware from your system.
In addition, you should always take care of your PC health after these kinds of cyberattacks – RESTORO is professional software that helps you repair the damage done to your system. To remove LCK ransomware from your PC, follow the steps below:
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
LCK ransomware virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
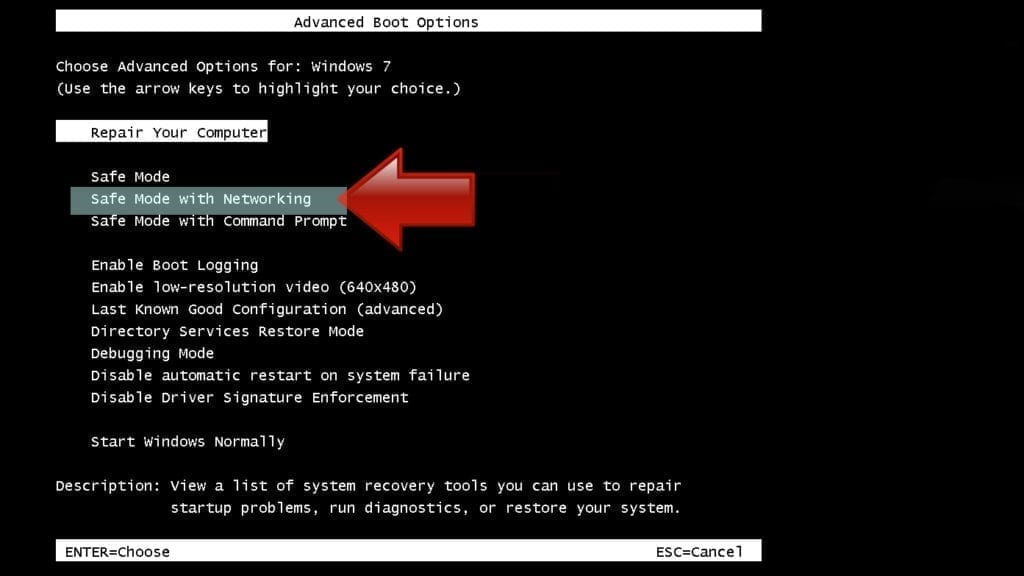
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
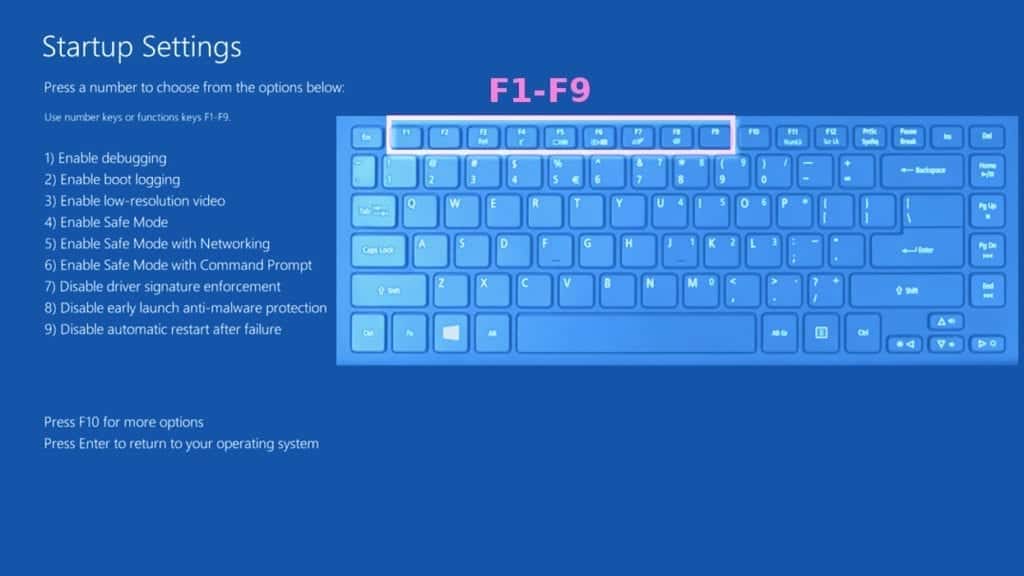
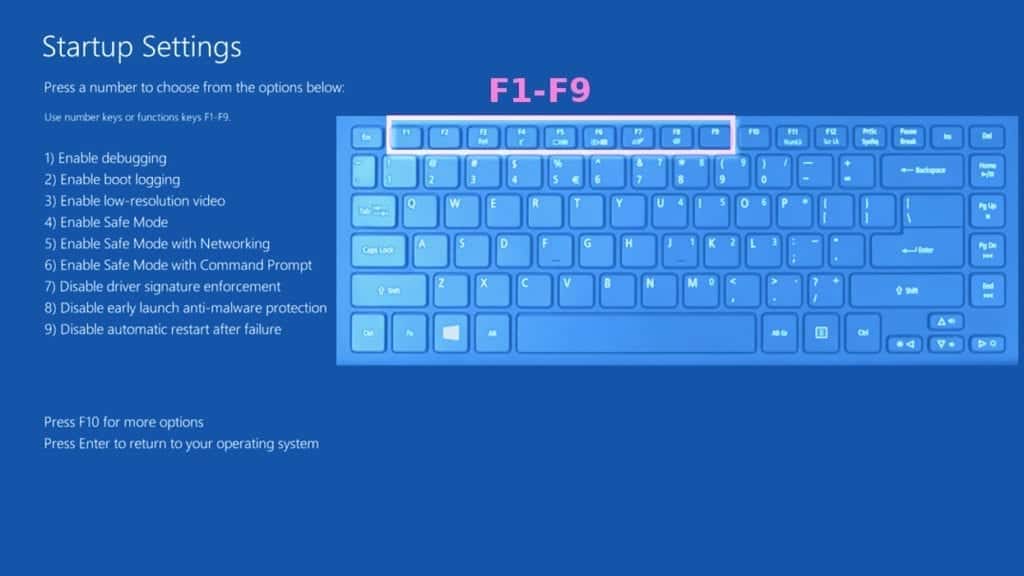
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
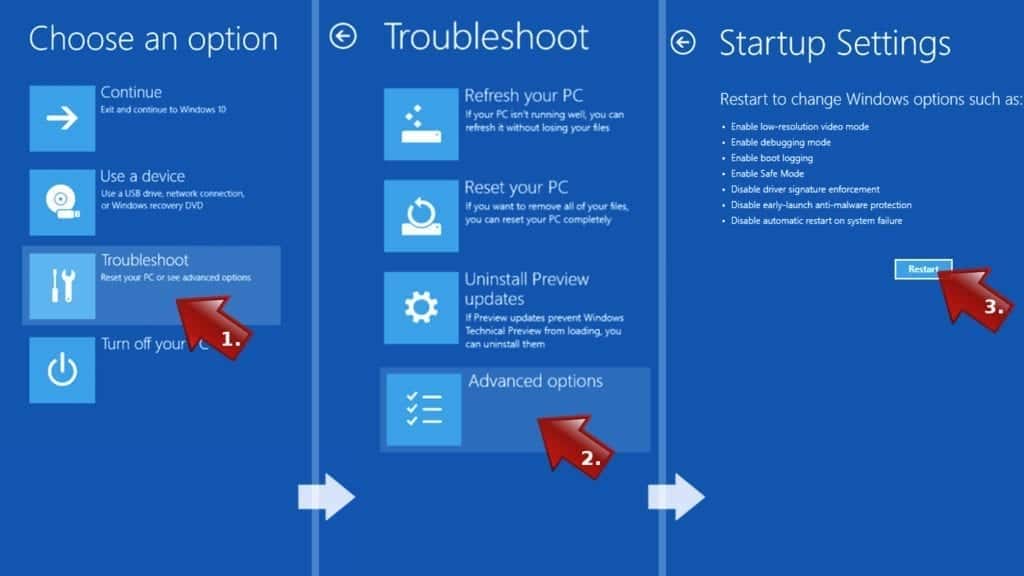
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove LCK ransomware virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
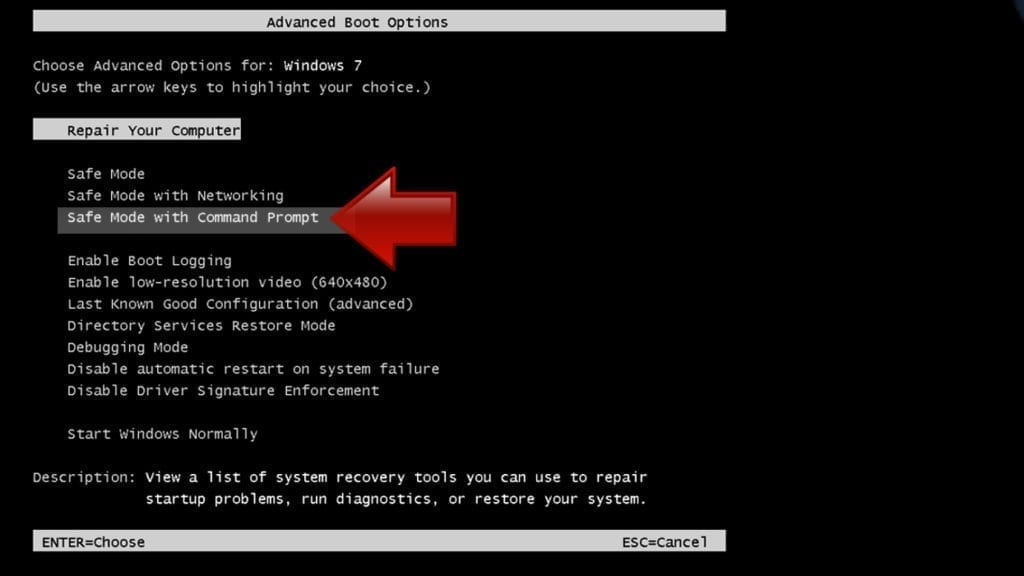
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
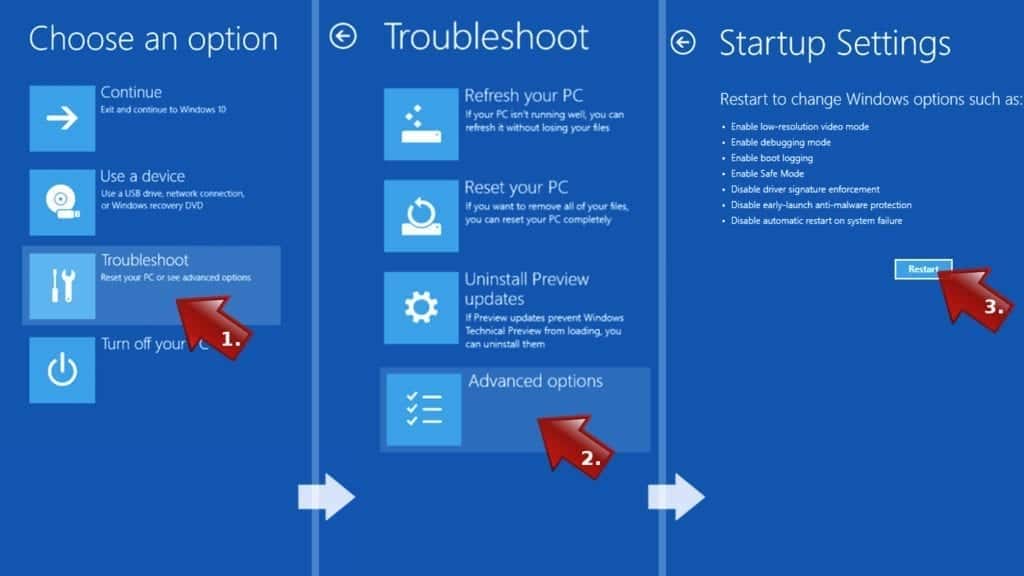
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
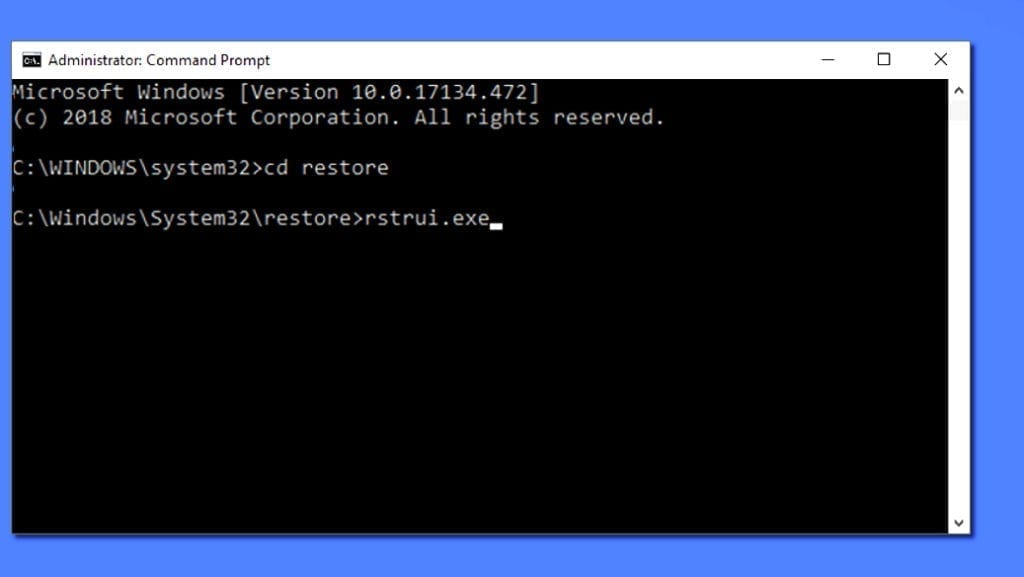
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
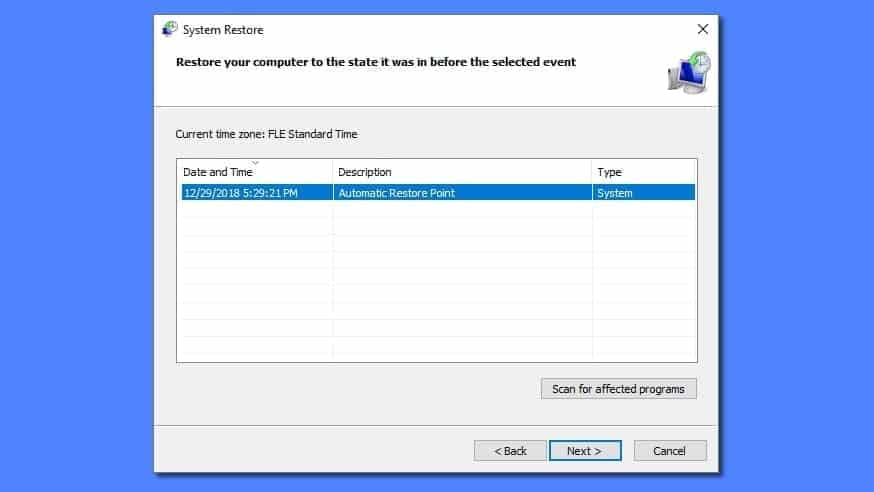
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
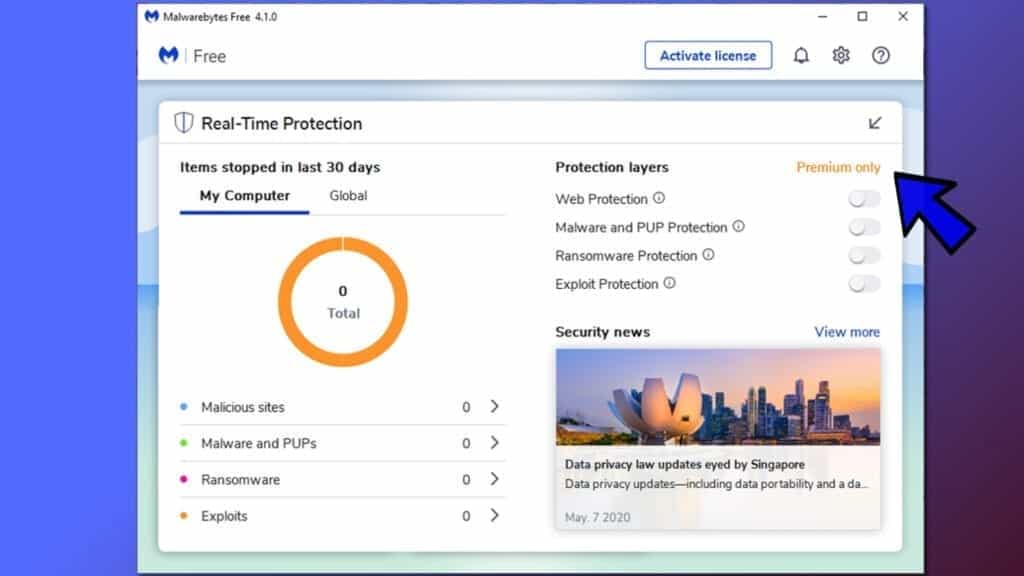
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
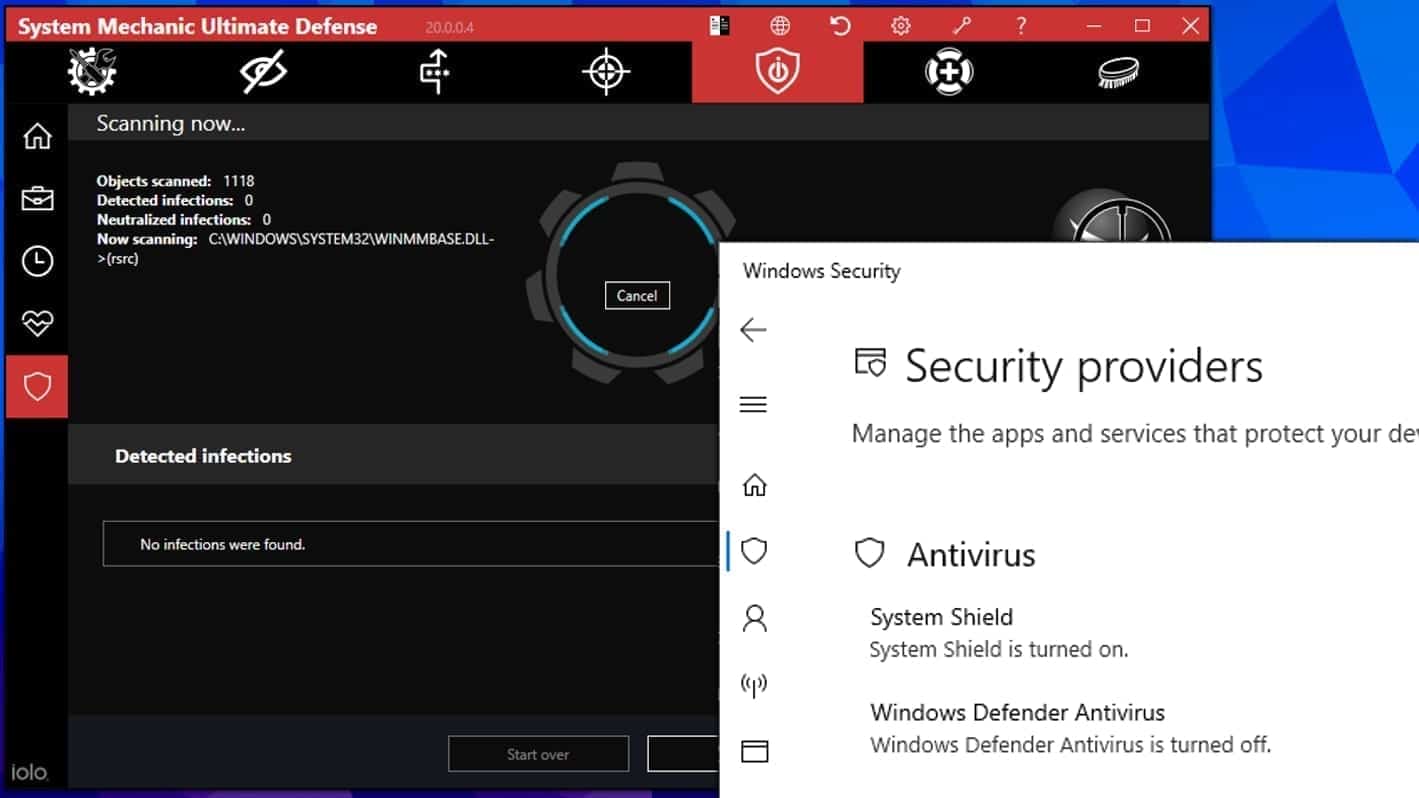
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Matt Corey is passionate about the latest tech news, gadgets and everything IT. Matt loves to criticize Windows and help people solve problems related to this operating system. When he’s not tinkering around with new gadgets he orders, he enjoys skydiving, as it is his favorite way to clear his mind and relax.

Leave a Reply