Beware of scammers asking to verify your identity for Coinbase
Contents
Coinbase Verify Your Identity is an email scam campaign actively distributed by cyber criminals. The letter asks to click on a provided button to verify user’s identity because the ability to login to Coinbase account has been disabled. The scammers ask to click on a phishing link and provide ID document to them. However, the link provided in the message leads to a fake website and if you provide any personal information or a photo of your ID there, it will be sent straight to cybercriminals who will use your ID for other criminal activities. Needless to say, you do not want to share your sensitive information with such parties.
The scam is designed to imitate the design of official digital currency exchange service provider emails. The message includes the following lines: “Please log into your Coinbase account below from a web browser to verify your identity. You will not be able to verify your identity from the Coinbase App.“
In other words, scammers behind this email invite you to a fake Coinbase website and ask you to provide your login credentials (name or email and password), as well as your ID. If they get this information, they can hack your actual account and steal your funds or perform unsolicited transactions in your name.

It is important to point out that the real currency exchange service provider is entirely legitimate and safe, but the attackers are simply using its name illegally. Phishing email scams are extremely popular nowadays as people spend more time at home during the pandemic lockdown. Other examples of scams circulating around the web are DPD delivery scam, FastSupport.com-based scams, $750 Cash App Transfer and others.
It is important to remind you that you should never click on links provided in such messages as they always lead to deceptive websites. These websites are designed to look like their original copies, however, usually there are a lot of details that reveal true nature behind it. For example, majority of the links don’t work on such sites, except of the forms designed to collect sensitive information from the victim.
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
We also recommend avoiding any interaction with email messages that you didn’t wait for. For instance, never allow displaying images on such emails. Typically, email security systems block included images by default, suggesting that this protects user’s privacy. It is true, because if you enable remote images to be displayed, the cybercriminals will notice that you have accessed included images, meaning that you have opened their message. This can result in a larger flow of spam targeted at you.
If you have been asked to verify identity again and you have recently verified it to the legitimate service, we strongly recommend you to rush to official Coinbase website and change your login credentials. Next, you will have to import your local authorities about a theft of ID details.
In addition, we strongly recommend scanning your PC with anti-malware to check whether the phishing page didn’t land any malware on your computer. For virus damage repair, consider scanning with RESTORO.
| Name | Coinbase Verify Identity Email Scam |
| Scam catchphrase | Important Notice: Please Verify Your Identity |
| Type | Phishing, Email Scam |
| Scam target | The email is designed to redirect the victim to a fake website to login using Coinbase’s credentials and upload personal ID |
| Danger | Loss of personal information, login credentials, social security number, personal ID, financial losses, potential malware infections |
| Distribution | The spam is distributed via email |
| Removal | Delete the email and never open it again. For your PC’s security, scan computer with anti-malware. To repair virus damage on OS, use RESTORO. |
Dangers of email spam and how to avoid being infected
Cyber criminals typically use email scraping to collect a list of potential targets, but they can also buy these email lists on the dark web. Once they have the target list, they compose convincing emails, use email address spoofing techniques (this makes the sender’s email address appear legitimate) and URL shortening services to disguise anything suspicious-looking in the message.
While email spam without attachment typically means phishing-type attack (the one meant to swindle sensitive information from you), some scams include .DOCX, .PDF, .ACE, .IMG and other format attachments. You should never open these files as they deliver a malicious payload such as ransomware (f.e., QLKM, STOP/DJVU, DHARMA) or a password-stealer like Glupteba or Azorult.
If you suspect that you have downloaded or opened a malicious email attachment, do not delay the malware removal procedure. This will help to prevent additional damage to your computer.
Users who have received the fake message should remove Coinbase Verify Your Identity email and scan their computers for malware immediately. If you have interacted with the email’s contents (such as clicked on links provided in them, or provided sensitive data) should change their login credentials on official Coinbase website instantly, and report about personal ID data theft to local authorities immediately.
After Coinbase Verify Email virus removal, you should also contact the cryptocurrency exchange service and inform that your login information might be compromised.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS

Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
malware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in Safe Mode with Networking, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to start Windows in Safe Mode:
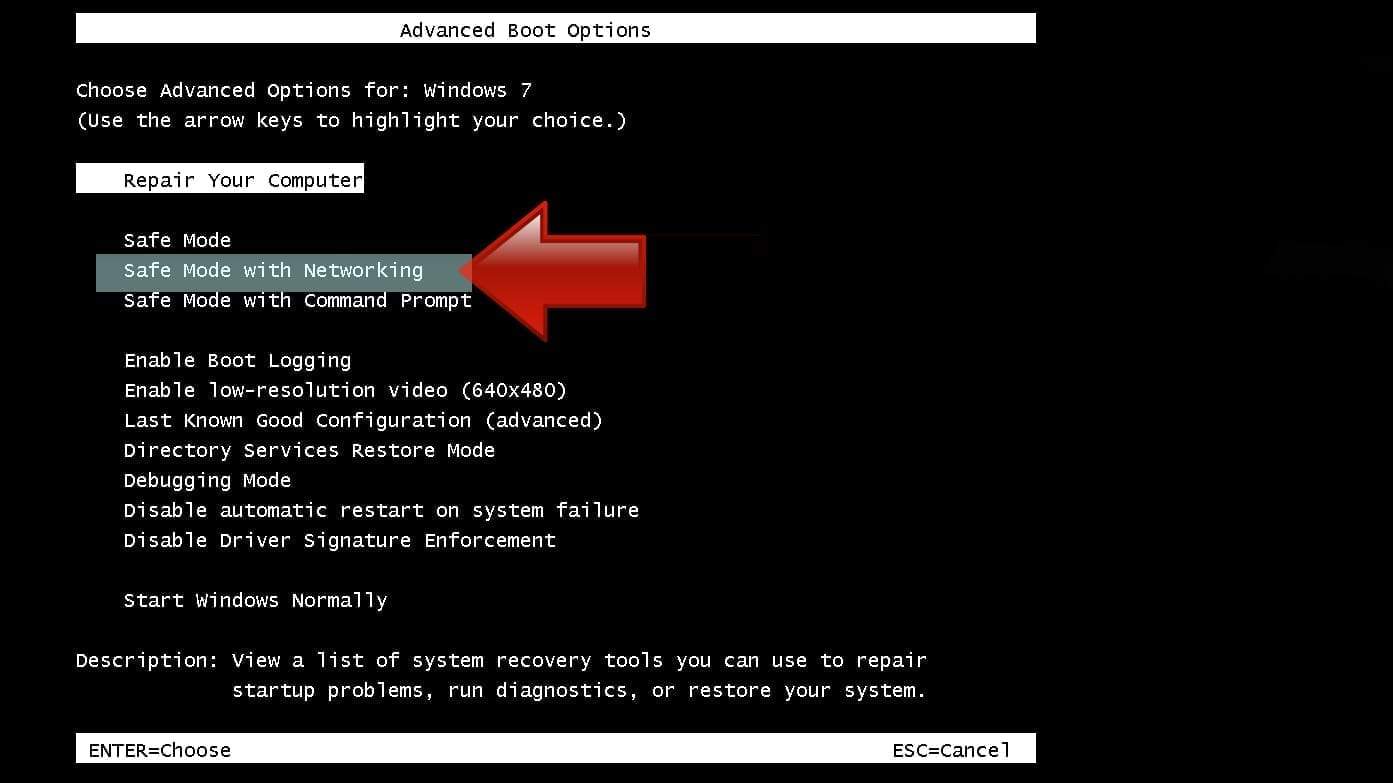
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

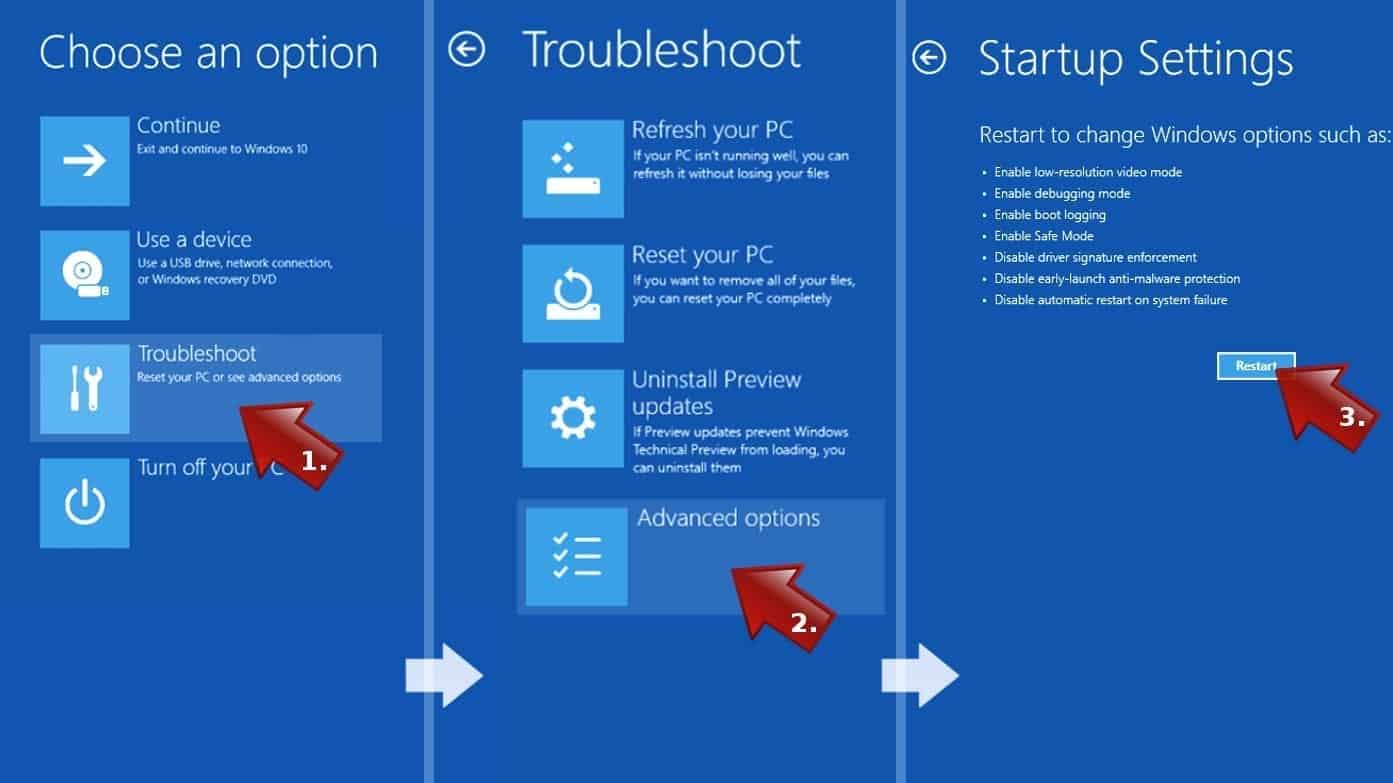
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
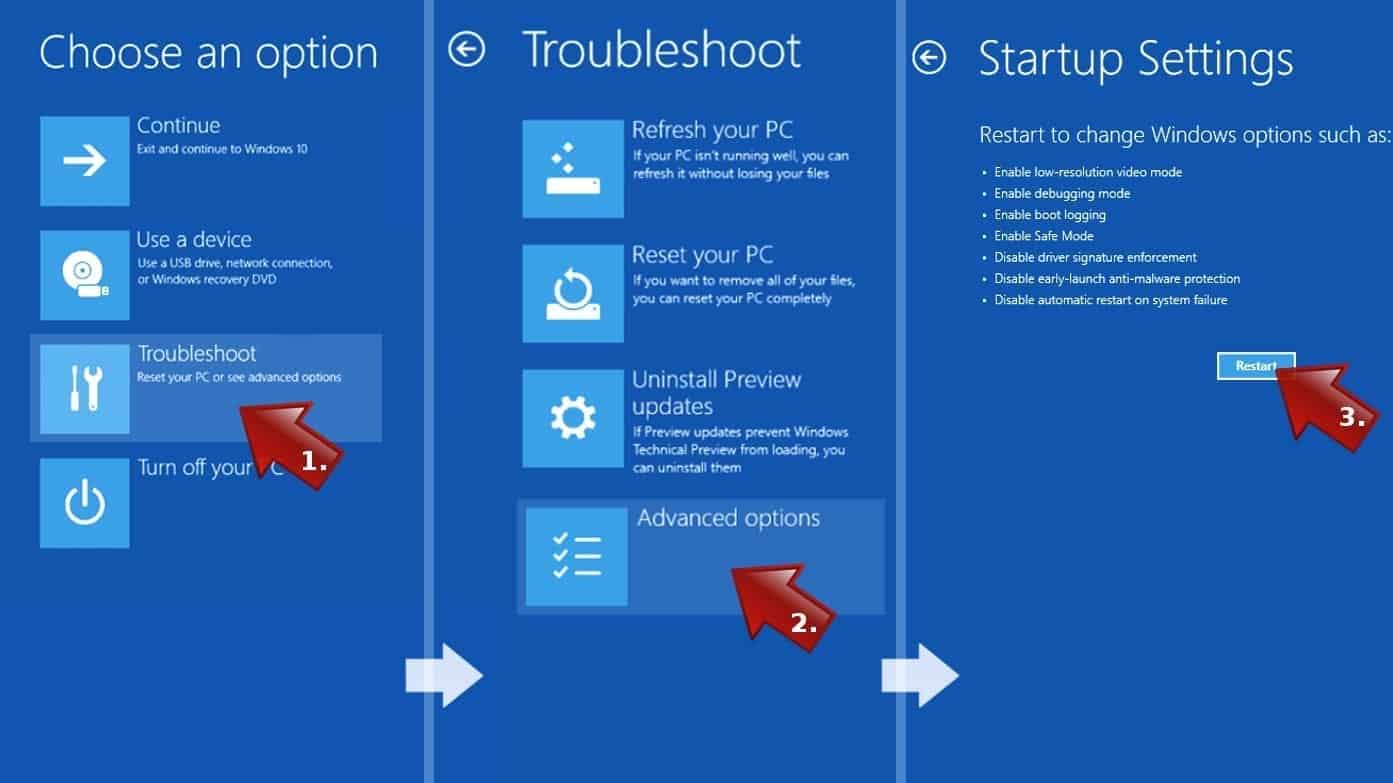
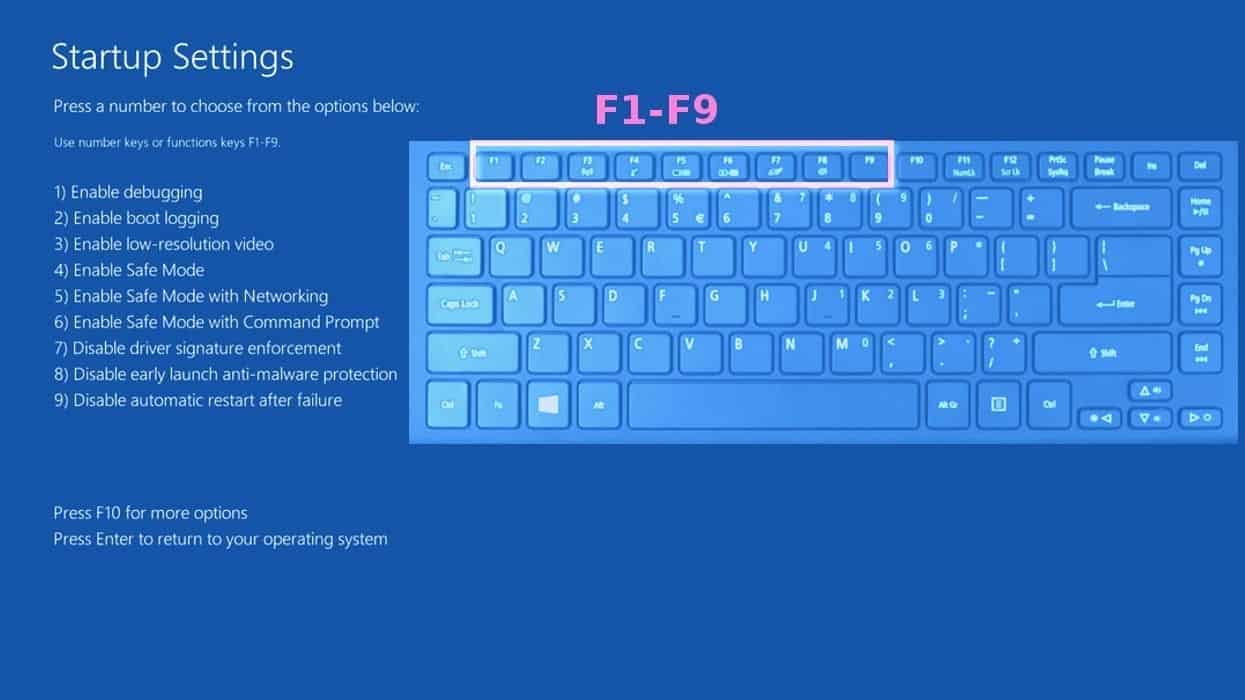
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove malware files. It is very hard to identify files and registry keys that belong to the virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. We recommend using SYSTEM MECHANIC ULTIMATE DEFENSE , which can also restore deleted files. Additionally. we recommend repairing virus damage using RESTORO.
Special Offer
Compatibility: Microsoft Windows
See Full Review
RESTORO is a unique PC Repair Tool which comes with an in-built Avira scan engine to detect and remove spyware/malware threats and uses a patented technology to repair virus damage. The software can repair damaged, missing or malfunctioning Windows OS files, corrupted DLLs, and more. The free version offers a scan that detects issues. To fix them, license key for the full software version must be purchased.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
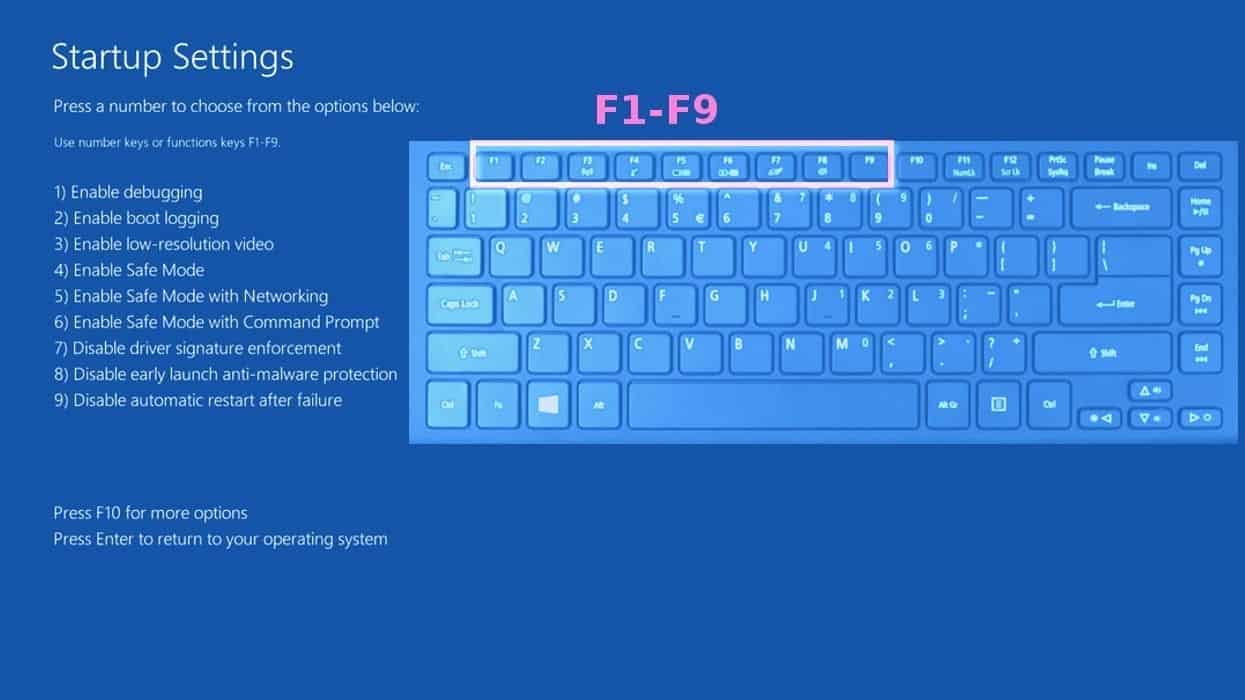
Step 1. Boot Windows in Safe Mode with Command Prompt
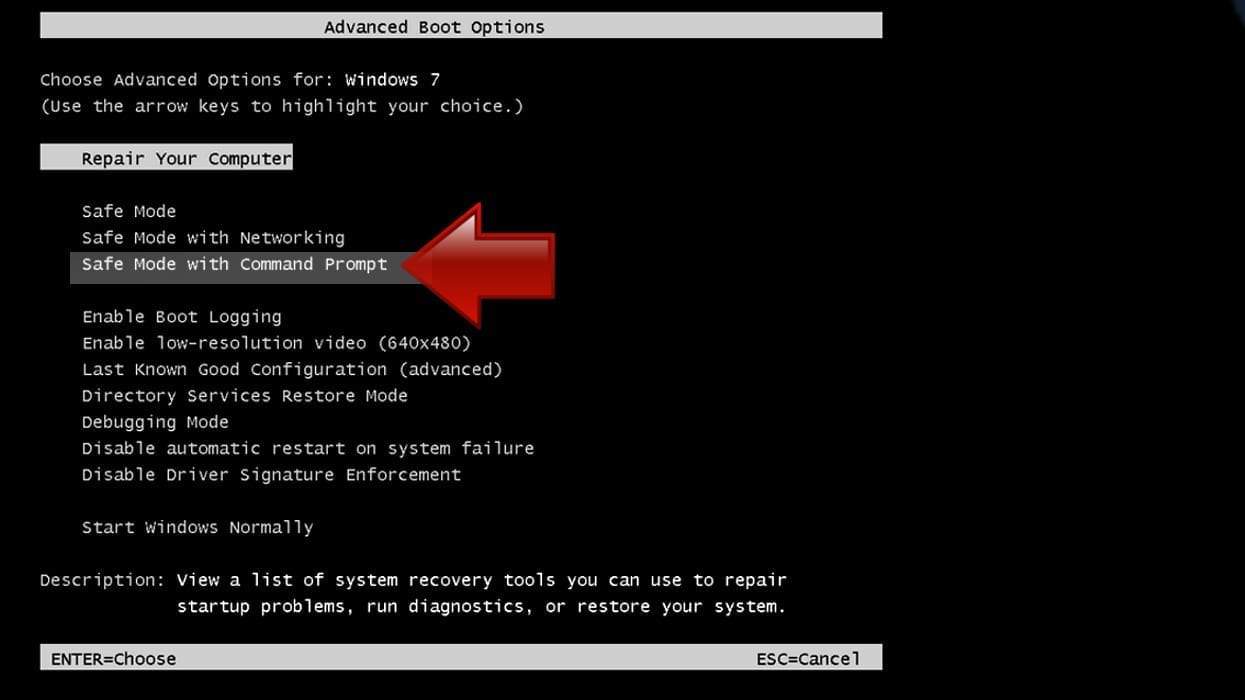
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.

- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before the malware infiltration.
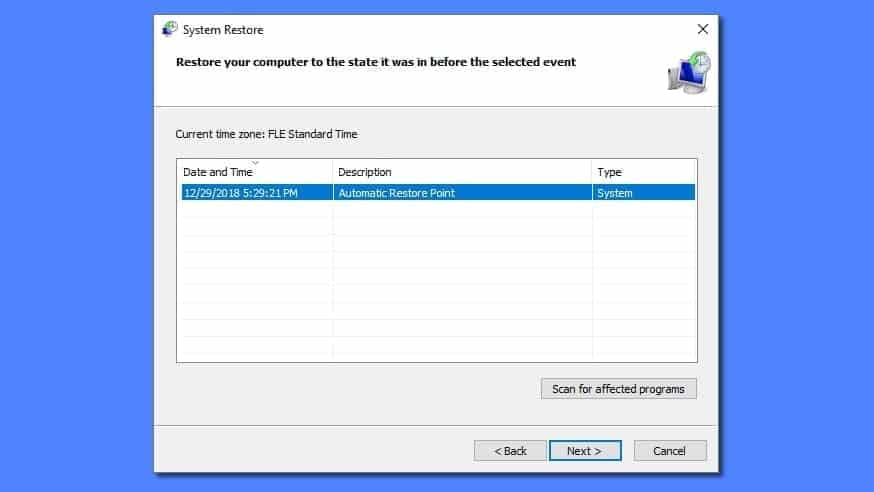
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
Coinbase is a scam!
Only influencier who give you referal code so that they get 10 euro says it is legitimate.
They are making money out of you and they even don’t tell you that. That is definition of scam.
I was losing money even when I was selling high and buying low. So I was suspicious of coinbase. So I decided to test.
I bought 100 Cardanos, I had to pay 177 euro.
Then immediately my portfolio drop to 172 euro.
Fine, market is be down, so let’s buy 100 more
And they want to charge me 177 euro for 100 cardano.
So they take 5 euro to just convert coins.
It is a huge margin. And they say that there is no fee. No fee your a**!
The price you pay is well hidden in their scam.