Remove KOTI Ransomware (.Koti File Virus)
KOTI Ransomware makes personal files inaccessible by encrypting them
Contents
KOTI Ransomware (also known as Koti File Virus) is a malicious computer virus that encrypts personal or work files on Windows operating systems. It is the 226th extension variant of STOP/DJVU ransomware, which uses military-grade encryption method to make files inaccessible and add an extra .koti file extension after the original one. For example, a file called document.doc becomes document.doc.koti after the cyber attack. Following a successful attack, the ransomware drops ransom notes called _readme.txt in every folder that was affected by data encryption.
The ransomware uses a stealthy technique to get onto victim’s computer – it usually arrives along illegal downloads such as game or software cracks. During the data encryption procedure, the malicious ransomware showcases a fake Windows update screen to make the victim believe that there’s nothing wrong with the initial download. In addition, it disables Windows Task Manager, so that the victim could not view currently running processes and disable the virus.
In the meantime, the virus attempts to contact its Command&Control server to generate an unique encryption/decryption key and personal ID for the victim. If this connection fails, the virus uses offline key instead (same for all hosts with failed C&C connections).
Koti File Virus then begins scanning and encrypting files on all computer folders, bypassing essential OS data folders to keep the system running. It assigns additional file extension to mark affected files and creates a ransom note containing the personal ID to inform the victim about data encryption and possible recovery scenario.
It is important to note that this ransomware tends to modify Windows HOSTS file and prevent victim’s from accessing certain computer-related websites. In addition, it installs Azorult, a password-stealing malware on the system.
Ransomware aims to extort the victim
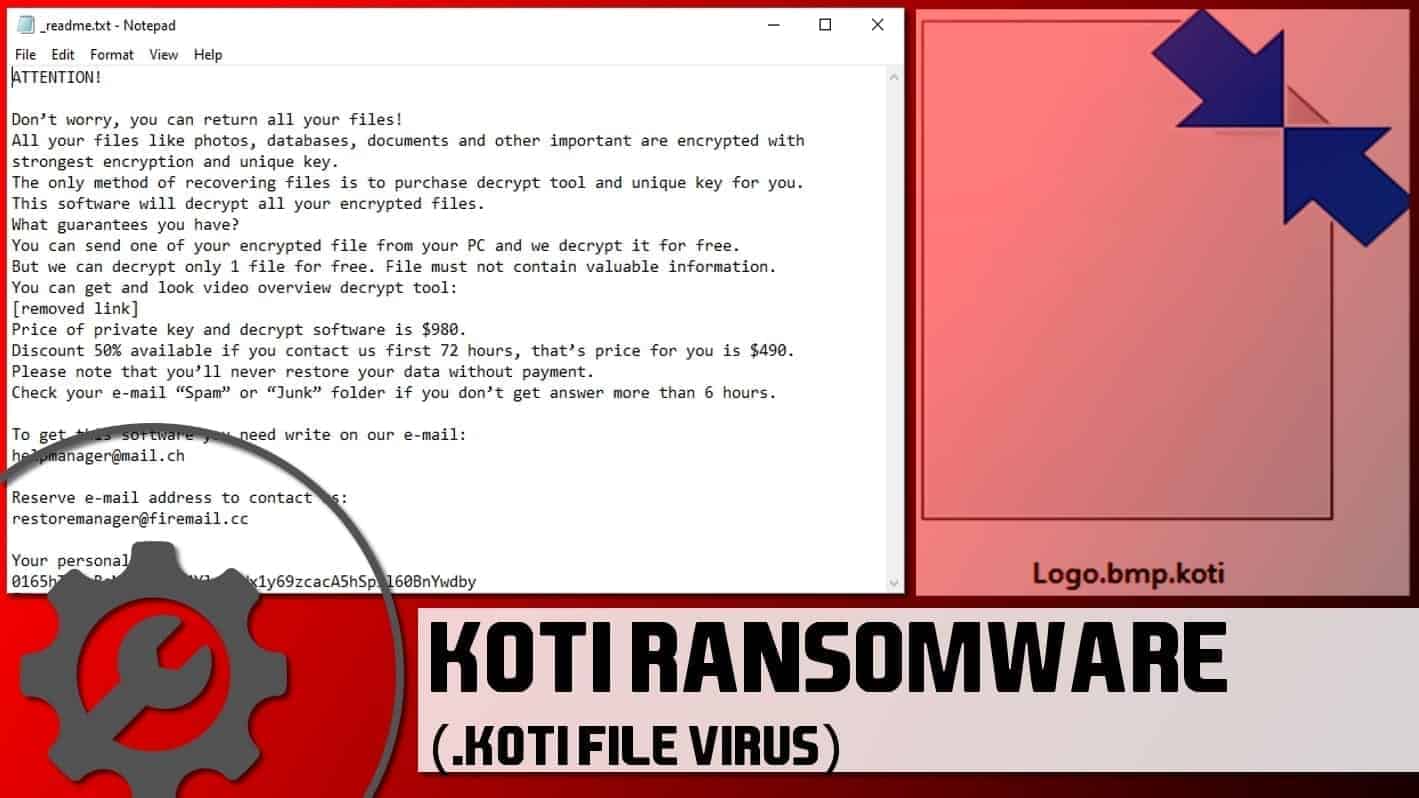
The primary aim of KOTI ransomware is to prevent the victim from accessing personal files, and force him/her to pay a specified ransom price in a certain cryptocurrency. The _readme.txt ransom note opens via default editor, Notepad, and contains a message from the cybercriminals. The crooks inform the victim that it is possible to restore encrypted files, but the victim must fulfill the attackers’ demand and pay them a ransom.
The note reads, “The only method of recovering files is to purchase .koti decrypt tool and unique key for you. This software will decrypt all your encrypted files.” The rest of the note informs that the attackers are willing to decrypt one file for free to prove that it is worth paying the ransom.
Speaking of the ransom price, Koti ransomware developers suggest 50% discount if the victim contacts them in three days (72 hours). This way, the ransom price is $490 in Bitcoin. If the victim contacts them later, the price rises to $980. Unlike similar viruses, this particular ransomware doesn’t have a payment website accessible via Tor browser. Instead, it suggests contacting the criminals via provided emails: helpmanager@mail.ch or alternative restoremanager@firemail.cc.
While we do understand that your data was important and that your primary goal now is to decrypt .koti files, we definitely do not recommend paying the ransom to cybercriminals. There are many reasons why you shouldn’t: crooks might not help you to recover the data, and by paying, you support the rising cyber crime industry. Instead of wasting your money this way, we recommend you to use it for your cyber security improvement and data backups.
You can successfully remove KOTI ransomware virus along with other malware it may have installed on your system (such as Azorult Trojan) using your anti-virus program. To repair damaged Windows system files, employ RESTORO.
Threat Summary
| Name | KOTI file virus |
| Type | Ransomware; file-encrypting virus |
| Version | 226th version of STOP/DJVU |
| Ransom note | _readme.txt |
| Ransom price | $490 or $980 |
| Extension | .koti file extension |
| Detection names | Trojan.MalPack.GS (Malwarebytes) Win/malicious_confidence_100% (W), A Variant Of Win32/Kryptik.HCSI, Trojan-Ransom.Win32.Stop.mh and others (full list on VirusTotal) |
| Symptoms | Ransomware starts the attack by disabling Windows Task Manager and displaying a fake Windows update screen. It then encrypts and marks all files with .koti file extensions. Additionally, the ransomware creates and drops files named _readme.txt will in every affected folder. The note tells that there is no way to restore files except of paying a ransom. |
| Contact emails | helpmanager@mail.ch or restoremanager@firemail.cc |
| Associated processes | FF86.tmp.exe or similar; Winupdate.exe (fake Windows update prompt) |
| Distribution | The virus typically arrives along with software cracks, KMSPico, keygens and similar illegal downloads, typically promoted via peer-to-peer download agents |
| Removal | We recommend using malware-removal programs to eliminate malicious remains from your computer. To identify and repair virus damage on Windows OS files, we recommend using RESTORO. |
| Post-removal steps | Restore files using data backups, or, if you have been affected by the offline encryption, wait for STOP Decrypter update. Change all of your passwords due to Azorult Trojan’s activity. |
Ransomware distribution explained
Ransomware-type viruses typically spread via:
- Malicious spam campaigns. Nowadays, cyber criminals can modify documents such as DOC or PDF to contain malicious macros or JavaScript to download and execute malware from external source as soon as the document is opened. Such files then are renamed into something like “invoice” or “report” and sent to work emails, urging the victim to open them as soon as possible. Such malicious campaigns often have words such as “URGENT,” “Confidential” or “IMPORTANT” in their subjects.
- Compromised websites. If hackers manage to break into a certain website and exchange downloadable files with malicious ones, they can speed up the malware distribution rapidly. Therefore, our suggestion is to have real-time protection enabled and save files to your computer instead of directly opening it. This way, you can set your antivirus to scan it first.
- Infectious downloads. Illegal downloads such as game cracks, movies and copyrighted music albums are very popular downloads, and hackers tend to pack them with malicious executables.
- Exploitable vulnerabilities in outdated software current on the target hosts. Please keep all your software, including operating system version up-to-date at all times. Software updates are issued to address not only various functionality improvements, but also security issues.
When it comes to STOP/DJVU ransomware variants such as KOTI file virus, MZLQ, SQPC, MPAL, QEWE and others, they all await victims in software cracks and similar illegal downloads. Many victims report downloading it along Adobe Photoshop Cracks, KMSpico and similar programs.
KOTI ransomware removal explained
You must remove KOTI ransomware to protect your privacy and security. To cleanse the system from the said virus and additional malware that it may have dragged into the system, we suggest using a powerful malware removal tool, such as RESTORO (includes Avira scanning engine). In addition, it can be used for fixing damaged system files, such as the affected HOSTS file.
You can find KOTI file virus removal guide down below. It was prepared by our experts and supplied with self-explanatory images to guide you through the process quickly.
PROFESSIONAL TIP. Do not forget to change your passwords after removing the malware from your system.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
KOTI Ransomware Virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove KOTI Ransomware Virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
REMOVE MALWARE & REPAIR VIRUS DAMAGE
1 Step. Get robust antivirus to remove existing threats and enable real-time protection
INTEGO Antivirus for Windows provides robust real-time protection, Web Shield against phishing and deceptive websites, blocks malicious downloads and blocks Zero-Day threats. Use it to remove ransomware and other viruses from your computer professionally.
2 Step. Repair Virus Damage on Windows Operating System Files
Download RESTORO to scan your system for FREE and detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
FAQ
You can’t, at least at the moment. Besides, you should check C:/SystemID/PersonalID.txt file to see if you’re affected by online or offline encryption. Offline encryption can be indicated by the string ending in t1. In this case, you should wait for STOP Decryptor update for Koti version. It can take months until such update will be issued.
You can restore your files if you had a data backup. However, you should remove the ransomware first.
Computer users are always advised to create regular data backups to keep important files safe in case the computer gets damaged physically or affected by file-damaging malware. If you do not have data backups, chances to restore files encrypted by ransomware are very low. However, it depends on a case. While many ransomware include flaws that can be leveraged by security researchers to create fully functional decryptors, KOTI virus isn’t one of them.
After removing KOTI ransomware, you should go to Chrome and see websites that you have saved passwords for. Change passwords for all these accounts. This must be done because the STOP/DJVU virus variants install password-stealers on compromised machines.
Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
Recent Posts
Remove WDLO Ransomware Virus (DECRYPT .wdlo FILES)
WDLO ransomware uses encryption to lock your personal files WDLO ransomware is a malicious computer…
Why You Need a VPN and How Does It Protect You?
What is a VPN and how does it work? The term VPN stands for Virtual…
Remove PPHG Ransomware Virus (DECRYPT .pphg FILES)
PPHG ransomware encrypts your computer files, threatens to keep them locked until a ransom is…
Remove SSOI Ransomware Virus (DECRYPT .ssoi FILES)
SSOI ransomware aims to lock all of your data on a computer and then extort…
Remove KKIA Ransomware Virus (DECRYPT .kkia FILES)
KKIA ransomware sneakily encrypts your files KKIA ransomware is a newly emerged computer virus that…
Remove HFGD Ransomware Virus (DECRYPT .hfgd FILES)
HFGD ransomware aims to take your computer files hostage HFGD ransomware is a malicious malware…