Unfortunately, There Are Some Bad News For You Email Scam
“Unfortunately, there are some bad news for you” scam email threatens to expose video
Contents
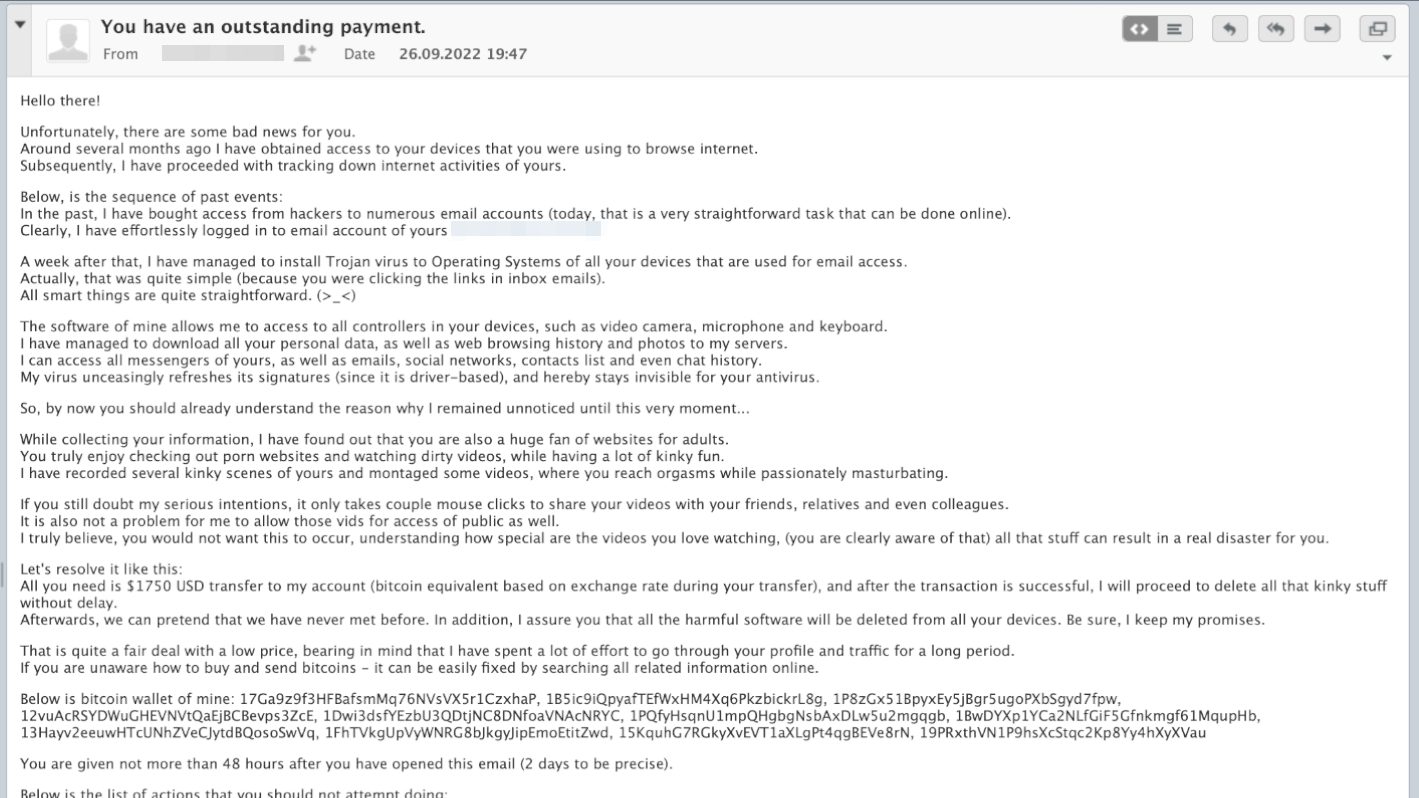
“Unfortunately, there are some bad news for you” is a fake sextortion email scam campaign. The scammer falsely claims to have obtained access to user’s devices, hacked email accounts, installed Trojans, downloaded files from user’s computer, and also recorded a sexually explicit video of the computer user. The email sender asks to pay a ransom, and threatens to share the video with recipient’s friends, colleagues and relatives, or even release it to public, if the scammer’s demands’ are not met.
If you have received this email, you should know that it is a complete scam and the email sender has no video of you. This email is being distributed to thousands of potential targets online and is intended to scare the computer user. Therefore, you should not worry that some compromising video of you exists, because the statements provided by the scammer are nothing else than lies.
Overview of the scam email message
The “Unfortunately, there are some bad news for you” email usually has a subject line that says “You have an outstanding payment,” although it varies depending on the case. The scammer then greets the target victim and suggests there are some bad news. The crook then proceeds to provide false statements about victim’s devices he/she hacked and browsing history accessed.
The lies continue further, as the cybercriminal provides alleged sequence of past events. According to the scam email, the sender has previously bought access to numerous email accounts and logged into the recipient’s email account. Furthermore, one has allegedly managed to install Trojan horse to the computer. This is backed up by a sentence that claims the user has been clicking links provided in inbox emails. Next, the scammer claims to have accessed the computer user’s camera, microphone and keyboard, as well as download various personal data, including contacts, emails, social networks, chat history, and more.
Finally, the email sender states that one has managed to find out that the user is a “huge fan of websites for adults.” Next, the scammer claims to have recorded and montaged several intimate videos of the computer user, and threatens to publish them, unless the user pays a ransom. The scammer demands paying $1750 via cryptocurrency. The note instructs to purchase Bitcoin worth the same amount and then transfer it to one of provided Bitcoin wallet addresses. The email also recommends doing so within 48 hours after reading the email.
Finally, the scam email includes a list of actions that user should not attempt taking, and list of things one should not be concerned about.
People who have received email threatening to expose video should know that it is a sextortion email scam. Its claims should be ignored. Do not try to reply to the email, or, even worse, send money to the scammer. Whoever is behind this email is simply trying to cause fear for you by claiming to have private recordings of you and control your device. Do not be afraid to use your devices and simply delete the email.
IMPORTANT. It is important not to click on attachments or links provided by the scammer, even if one claims to provide proof of collected material. Scammers often try to infect user’s computer with malware after causing frustration and sense of urgency for the recipient.
If you suspect that you may have installed some untrustworthy programs or malware lately, simply scan your device with a trustworthy antivirus. Our team recommends using INTEGO Antivirus for this task.
Threat Summary
| Name | Unfortunately, There Are Some Bad News For You Email Scam |
| Type | Email Scam, Phishing, Sextortion Scam |
| Email subject line | You have an outstanding payment |
| Deceptive statement | The scammer falsely claims to have hacked into the recipient’s email account and installed Trojans on all devices, plus recorded intimate recordings of user during visits to porn websites. The email threatens to publish these videos unless a ransom demand is paid. |
| Ransom amount | $1750 in Bitcoin |
| Criminals’ Bitcoin wallet addresses | 17Ga9z9f3HFBafsmMq76NVsVX5r1CzxhaP, 1CW1kBHJsuS9zRj5qvpoAgEwDJQA3bUVPW, 1JSrCb8fwX15475Jztt3yA7JWHXzzxTX9h, 1B4h63LjY8ZZBLuk1r5s6HkeVRV5W6uRE2, 17kmbhxxMsrFhmQNim1jbjD6AeBUQ2SbYp, 1HQWaFbMUvQqeRQsWzyX4HsAvzvhVLqZxL, 1C2ek9b57xdVY9rPUaUnczxN5vGjVS8EhA, 1pSw6eh5GoWtBrETzPbM36DGxc6Tes5Mp, 1LrBGezKti4m2cov7CKuurLnCfQvjp2o1A, 1LV8rSHsXYQ9JWUM4LRAGywH8RA6DXH6A7, 1Mjt2xobFExdZBGfjTVDcgzJWQxRxoHBdA, 153tGcwGFcj33YXxtjvgnzCYW1FhcPo1CM, 1771s891APz1wNKdn5fe3Vknmf5pN18cWu, 1Bg62SYMjRfcSVaUM9VoAcr8Fy6bX2qQbN, 1GvxuP9puQCMNQvEKuwNrLeGwp9LWV4822, 1LzA9kzQkGDTYSfbbLE8gK5RAJ5ke32ntC, 12vuAcRSYDWuGHEVNVtQaEjBCBevps3ZcE, 1EeaB9n9RKCsxbzzmVNNPbcu9Lrq89Bm4Y, 1PQfyHsqnU1mpQHgbgNsbAxDLw5u2mgqgb, 1Aohp9uhpReFfZirTimqD1LUYtZ2gpvBtP, 1kZ8v4CZ29izLdtacgkdsCkMU5P7uVqKJ, 19emozKjqs4dUv3JjsHSXtKPDcGYwW2e5X, 18QoRGdPTpu6wMVKjf8PA43ZXndAJfrHvM, 15kiZUAtEYRC3m5ZWo2DYkrCeGbj5fRhDN, 1EaTepwwBEDQhmHsjuwQtX5V3ZMnnTbnY8, 1P8zGx51BpyxEy5jBgr5ugoPXbSgyd7fpw, 1B5ic9iQpyafTEfWxHM4Xq6PkzbickrL8g, 13Hayv2eeuwHTcUNhZVeCJytdBQosoSwVq, 1FhTVkgUpVyWNRG8bJkgyJipEmoEtitZwd, 15KquhG7RGkyXvEVT1aXLgPt4qgBEVe8rN, 19PRxthVN1P9hsXcStqc2Kp8Yy4hXyXVau, 1MW4maqRuqi62YiRNMaBiHT65WJJMEAvQw, 1Dwi3dsfYEzbU3QDtjNC8DNfoaVNAcNRYC, 1BwDYXp1YCa2NLfGiF5Gfnkmgf61MqupHb, 17YJKh4TNBDrgFKfbjbQHCGEmZH8uvFoVp, 1B33LTohL4pWrZsjSpzLYjZ6WorWkwnoGE, 1K8g3n8Z9t265pMYuhpKc8jfmPS6cY7Qcr, 18wgLNrXoSqtCDSiTuAgQs9gfojHeecSnN, 1M4bujoHX8TVpWw65zxNHKeDTHZXouZcpR, 1GvZB6bVDrt6ynaR9YEUSE1H2K8DzPLtmq, 1YcRyyF4obSGLyh1QJ9jyxv67ksYmM2oc, 1Dgd4jfNiGPoRrRPNgwgw2vcr6TgNGJ2FB, 13jKLyAFhjVRiWyg1TTPVjweFBAyUyBiy8, 114vHR5SDqqX7DAtYcFe7hmCZD4Jsad3jH, 12gHyoR78pjHpfueWUYyMudnwNMc6NGEPY, 1KXiY1reDCotVXpYdar6zoNknqGAsi1WeG |
| Potential damage | The scammers might trick people into sending money to them over false claims. They might also request remote desktop connection to drop malware on your computer. Additionally, such emails may include links or attachments leading to a malicious file. |
| Distribution | Email spam campaigns |
| Removal | If you suspect that scammers dropped malware on your computer via remote desktop connection, remove it from your PC using trustworthy software. To repair virus damage on Windows OS files, consider scanning with RESTORO (secure download link). |
Intego Antivirus for Windows
Award-winning antivirus solution for your PC.
Robust security software that provides robust 24/7 real-time protection, Web Shield that stops online threats/malicious downloads, and Prevention engine that wards off Zero-Day threats. Keep your PC safe and protected against ransomware, Trojans, viruses, spyware and other forms of dangerous programs.
How to tell if sextortion email is real?
“You have an outstanding payment” blackmail email that claims to deliver some bad news is similar to many other sextortion emails. The first thing you need to remember after receiving a similar message is to not panic. The absolute majority of such extortion emails turn out to be scam. There is no reason to believe the scammer’s claims about some video, even if they seem ominous.
Think about it this way – why is the email sender blaming you without showing any proof? The answer is because they do not have anything on you. Even if they attach some files, or URLs, clicking on them would be a bad idea because that’s a common way of infecting target’s device with malware.
Next, do not think about responding to the email. Doing so will only result in more threats as the scammer will try to convince you to pay the ransom.
Sometimes, these scammers will include a real password of yours in the email subject line. The reason behind this is that cybercriminals can buy leaked passwords and other data from dark web and use that information as an extra detail to scare you. Often times, these are old passwords that you no longer use, or have changed a while ago. If you’re concerned, you can change the mentioned password wherever it is still used, and consider using strong passwords for all of your accounts.
Another question that concerns recipients of this email threatening to expose video is that sometimes it appears to be sent from the user’s own email account. If you’ve noticed this, you should know that email addresses can be spoofed. There are hundreds of websites that allow doing this, and it is a common technique used by cybercriminals to conceal their suspicious-looking email address.
In addition, you can scan your computer with an up-to-date antivirus to detect malware, and remove it, if any is found. However, remember that cybercriminals are only pouring false claims to make you feel ashamed and scared enough to send them money.
Remove the scam email and check your computer for malware
If you have received the Unfortunately, there are some bad news for you scam email, just delete it. If you’re concerned about your privacy, you can check your passwords and update them with stronger versions, or set up additional protection by enabling two-factor authentication for your accounts.
Additionally, you can scan your computer with antivirus software to see if any threats are installed. It is highly recommended to do so, if you have clicked on some suspicious URLs or email attachments lately.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS
Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
malware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in Safe Mode with Networking, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to start Windows in Safe Mode:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove malware files. It is very hard to identify files and registry keys that belong to the virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. We recommend using SYSTEM MECHANIC ULTIMATE DEFENSE , which can also restore deleted files. Additionally. we recommend repairing virus damage using RESTORO.
Special Offer
Compatibility: Microsoft Windows
See Full Review
RESTORO is a unique PC Repair Tool which comes with an in-built Avira scan engine to detect and remove spyware/malware threats and uses a patented technology to repair virus damage. The software can repair damaged, missing or malfunctioning Windows OS files, corrupted DLLs, and more. The free version offers a scan that detects issues. To fix them, license key for the full software version must be purchased.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before the malware infiltration.
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
Scott Bolton is a senior content strategist in our Geek’s Advice team. He is exceptionally passionate about covering the latest information technology themes and inspire other team members to follow new innovations. Despite the fact that Scott is an old-timer among the Geeks, he still enjoys writing comprehensive articles about exciting cybersecurity news or quick tutorials.
Recent Posts
Remove Chromstera Unwanted Browser (Removal Guide)
Chromstera Browser gets installed with rogue software Chromstera Browser is a suspicious application that is…
Decrypt Files Locked by STOP/DJVU Ransomware (2024 Guide)
Data decryption solutions for STOP/DJVU ransomware victims STOP/DJVU ransomware virus (also known as StopCrypt) is…
Remove MagnaEngine Browser Hijacker (MagnaSearch Removal Guide)
MagnaEngine redirects lead to questionable websites MagnaEngine browser extension (also known as Magna Search) is…
Remove BGZQ Ransomware Virus (DECRYPT .bgzq FILES)
BGZQ ransomware locks files, demands a payment BGZQ ransomware is a file-encrypting computer virus that…
Remove BGJS Ransomware Virus (DECRYPT .bgjs FILES)
BGJS ransomware is a file-encrypting virus BGJS ransomware is a malicious computer virus that aims…
Remove KAAA Ransomware Virus (DECRYPT .kaaa FILES)
KAAA ransomware encrypts files and demands ransom payment KAAA ransomware is a file-encrypting malware targeting…