Remove Ragnar Locker Ransomware Virus (Decrypt .Ragnar Files)
Ragnar Locker ransomware encrypts data and also terminates essential processes on the PC
Contents
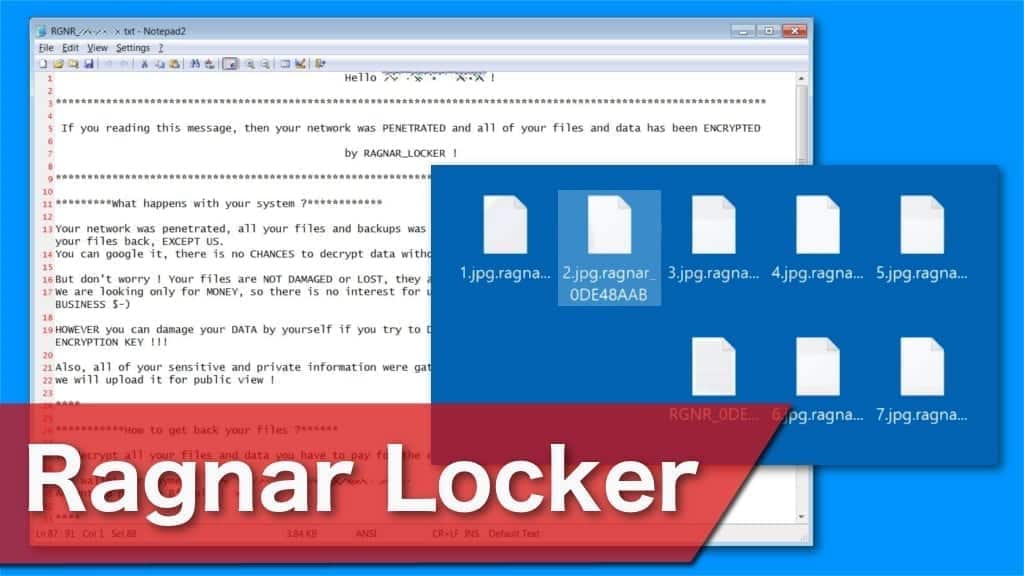
Ragnar Locker is a file-encrypting virus that is designed to encode almost all information on the affected computer. It is also programmed to terminate widely used applications on Windows operating systems, such as Kaseya or ConnectWise. Encrypted files are marked with .Ragnar_[random-string] extension and a string of unique characters. Cybercriminals leave a RGNR_0DE48AAB.txt text file as a ransom note and urge to reach out via hello_psecu@protonmail.com email or use qTox messenger. They demand to pay 25 Bitcoins for the decryption key.
Usually, when the ransomware infiltrates the system, it begins the encryption process immediately. The malicious program scans all files on the computer to identify its targets. Unfortunately, file-encrypting viruses encode almost all data, including videos, photographs, audios, documents, and others. Once the encryption is done, files are no longer accessible for regular use. Victims can notice that they are unable to open files marked with .Ragnar_[random-string] extension.
Furthermore, file encryption is not the only action that this ransomware performs. As mentioned before, it terminates some essential processes run by programs on the attacked systems. Those processes are related to managed service providers and help the crypto-malware to remain undetected and unstoppable. In other words, there is no way to avoid encryption once the ransomware infiltrates the system.
However, it is vital to remove Ragnar Locker virus despite the fact that you cannot stop it at first. Just like WastedLocker, Maze, MAKOP, these types of cyber threats are highly dangerous for regular computer users and should be eliminated with the help of the professional. Our suggestion is to download and install a reputable antivirus to get rid of all malware-related files safely. Although, the encrypted files will remain inaccessible.
Criminals threaten to double the ransom price
After successful encryption, victims receive a RGNR_0DE48AAB.txt file as a ransom-demanding message. Attackers indicate that all information stored on the computer and connected devices is encrypted with a powerful cryptographic algorithm. They state that there is no other way to restore it without their help. For that, criminals urge to reach them via a provided contact on qTox messenger or write to hello_psecu@protonmail.com email.
Victims are demanded to contact the crooks within 2 days and pay 25 Bitcoins for Ragnar Locker decryption key. If people do not reach out, the price is doubled after 14 days of infection. Additionally, the price is altered according to the network size of the company, number of employees, and annual revenue. Likewise, it is right to say that the attackers target large scale organisations more than regular computer users.
Cybercriminals also try to prove that they are able to decrypt affected data. They offer to restore one file for free as proof. Also, they threaten their victims to expose sensitive information and permanently delete the decryption key if they refuse to make a contact within 21 days of the infection. Despite how scary it may seem, we do not recommend dealing with the attackers under any circumstances.
The wisest decision would be to perform Ragnar Locker removal as soon as you notice any symptoms. For that, it is essential to get a reputable malware removal software and scan your computer. Our team advises using RESTORO. After elimination, you can proceed to restore the affected data from backups.
Developers collaborate with other ransomware creators
Security researchers identified that the developers of Ragnar Locker are collaborating with other ransomware creators, including LockBit and Maze. This cooperation grew into the so-called Maze Cartel and the stolen information from the victims of all three ransomware viruses is now being upload on the Maze website.
Additionally, the new version of this cyber threat uses a different ransom note and file extension for the encrypted data. From the middle of July 2020, researchers spotted the latest variant of this malware leaving $R4GN4R_[random-string]! file as a ransom note and appending .ragn@r_[random-string] extension.
Furthermore, the latest variant of the virus is capable to avoid detection by running in a Virtual Machine. It uses Windows Group Policy Object (GPO) task executing msiexec.exe Microsoft Installer process that installs MSI package. It includes Oracle VirtualBox hypervisor and a Virtual Disk Image (VDI) file that has Ragnar Locker virus. Once it runs in the Virtual Machine, it cannot be terminated.
| Name | Ragnar Locker |
| Type | Ransomware virus, File-encrypting virus, Crypto-malware, File Locker |
| Extension | .Ragnar_[random-string]; .ragn@r_[random-string] |
| Targets | Mainly focuses on organizations rather than individuals |
| Contacts | hello_psecu@protonmail.com or a private contact on qTox messenger |
| Ransom note | RGNR_0DE48AAB.txt; $R4GN4R_[random-string]! |
| Amount of the ransom | 25 Bitcoins at first and might be doubled to 50 Bitcoins later |
| Symptoms | After infiltration, files are encoded with a cryptographic algorithm and can no longer be accessed |
| Damage | Along the encryption, this malware terminates certain processes to avoid detection and interruption; Attackers claim to expose sensitive information if they do not receive the payment |
| Distribution | Software cracking programs and malicious spam emails |
| Decryption | Currently, victims can only recover data from backups |
| Removal | Remove malware using robust anti-malware solution. We recommend using RESTORO to repair virus damage afterward. |
Two types of crypto-malware distribution techniques
There are the two most common ransomware distribution methods currently employed. The first one is spreading malicious programs as links in spam email campaigns. The crooks create letters that resemble notifications from banks or software companies. They urge to click on the link to supposedly update their account information. Unfortunately, the link starts an automatic installation of ransomware on the system.
Another technique is to place ransomware executables on peer-to-peer (P2P) file-sharing sites as software cracks. People tend to browse on illegal websites to obtain paid programs for free. The ransomware is named as the well-known software and many users fall for this trick. Thus, end up installing file-encrypting viruses instead of legitimate applications. You should never browse on suspicious sites or avoid downloading content from unverified sources.
Explaining Ragnar Locker ransomware removal process
As we have already mentioned, ransomware-type infections are highly complex. Many crypto-malware are programmed to prevent their elimination and regular computer users do not necessarily have the skills to circumvent them. Likewise, security experts recommend getting professional antivirus tools to remove Ragnar Locker virus safely.
You can get RESTORO or another reputable software and run a full system scan. We have prepared a detailed guide showing how to start Ragnar Locker removal by booting your system into Safe Mode. You can find it at the end of this article. Once you get rid of the malware, try restoring data from the latest backup copies in the Cloud.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
Ragnar Locker ransomware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove Ragnar Locker ransomware files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
REMOVE MALWARE & REPAIR VIRUS DAMAGE
1 Step. Get robust antivirus to remove existing threats and enable real-time protection
INTEGO Antivirus for Windows provides robust real-time protection, Web Shield against phishing and deceptive websites, blocks malicious downloads and blocks Zero-Day threats. Use it to remove ransomware and other viruses from your computer professionally.
2 Step. Repair Virus Damage on Windows Operating System Files
Download RESTORO to scan your system for FREE and detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
Scott Bolton is a senior content strategist in our Geek’s Advice team. He is exceptionally passionate about covering the latest information technology themes and inspire other team members to follow new innovations. Despite the fact that Scott is an old-timer among the Geeks, he still enjoys writing comprehensive articles about exciting cybersecurity news or quick tutorials.
Recent Posts
Remove HFGD Ransomware Virus (DECRYPT .hfgd FILES)
HFGD ransomware aims to take your computer files hostage HFGD ransomware is a malicious malware…
Remove RGUY Ransomware Virus (DECRYPT .rguy FILES)
Description of RGUY ransomware which is designed to encrypt files on computers worldwide RGUY ransomware…
Remove MMUZ Ransomware Virus (DECRYPT .mmuz FILES)
MMUZ ransomware arises from the infamous STOP/DJVU data-encrypting malware group MMUZ ransomware is a dangerous…
Remove VLFF Ransomware Virus (DECRYPT .vlff FILES)
VLFF ransomware is a virtual menace to your computer files VLFF ransomware is a newly…
Remove UIGD Ransomware Virus (DECRYPT .uigd FILES)
UIGD ransomware encrypts all files on a computer, asks for a ransom UIGD ransomware is…
Remove EYRV Ransomware Virus (DECRYPT .eyrv FILES)
EYRV ransomware takes your computer files hostage, demands a ransom EYRV ransomware is a destructive…