LockBit ransomware warns to pay the ransom or it publishes files online
Contents
- LockBit ransomware warns to pay the ransom or it publishes files online
- Ransomware operation in detail
- Lockbit launches a website to leak victims’ data
- Ransomware distribution explained: how to protect yourself or your company?
- LockBit ransomware developers push new versions
- Remove LockBit ransomware safely and restore your files
LockBit ransomware is a file-encrypting virus that is being used as a cyber weapon to perform targeted attacks on large companies. Once infected, all files on the target network will be encrypted, marked with .lock2bits, .abcd or .lockbit extension and become impossible to open. Compromised folders will also contain ransom notes called Restore-My-Files.txt. Since this virus is known to be part of MAZE ransomware cartel, it also threatens to publish victim’s files online if ransom won’t be paid. In September 2020, Lockbit ransomware operators launched data leak site to publish victims’ files if they refuse to pay the ransom. The malware first emerged in September 2019 and has been actively updated and distributed since then. It is a highly active threat because its malicious code is being sold as Ransomware-as-a-Service (RaaS) on dark web forums, meaning that criminals can join an affiliate-like program and earn commisions by helping to distribute virus faster.
The Restore-My-Files.txt ransom note tells the victim that all of his/hers important files are encrypted. According to the note, there is only one way to get files back – contact the criminals, send one encrypted file to them, receive its decrypted version (this is done to prove that the decryption tool exists), then pay for a decryption software and recover files. In other words, LockBit developers corrupt victim’s files temporarily, then ask the victim to pay a ransom to set the data free using a decryption software and private decryption key. The message says that the file used for decryption testing should not exceed 1MB in size.

The virus’ developers insist that using third-party software will cause permanent data loss, and also inform about scammers who claim to decrypt files for a certain price (usually higher than the ransom itself), but pay with victim’s money to the original ransomware developers instead. The ransom note also says that the victim should send identical messages to both provided emails – goodmen@countermail.com and goodmen@cock.li. It is pretty ironical that the email boxes created by the cyber criminals use “goodmen” as username. However, based on virus version, the ransom might contain a different contact email address.
Currently known Lockbit ransomware contact emails are:
- pcabcd@countermail.com;
- recoverymanager@cock.li;
- goodmen@cock.li;
- goodmen@countermail.com.
The LockBit ransomware note also includes a personal ID in the message. The personal ID is a lengthy string of characters, which is used to identify the infected host among all other victims.
The described ransomware is essentially similar to other ransom-demanding virus examples, such as COPA, STOP/DJVU, PHOBOS, NEMTY or NEFILIM. All of such programs infect victim’s computer or network silently, apply crypto-ciphers on personal or work files, then leave text files with a message from the attackers. The ransom notes usually demand paying large sums of money, typically starting at $500, in Bitcoin. The cybercriminals demand payments in such currency because it helps to keep their anonimity.
Ransomware Summary
| Name | LockBit ransomware |
| Type | Ransomware; File-encrypting virus |
| Extensions used to mark files | .abcd, .lockbit, .lock2bits |
| Ransom note | Restore-My-Files.txt |
| Contact Emails | goodmen@countermail.com, goodmen@cock.li |
| Damage | LockBit virus makes all personal or work files inaccessible by encrypting them. As a result, the victim can no longer open, edit, or view them. To restore corrupted files, virus’ developers demand sending them money in Bitcoin – paying a ransom. |
| Symptoms | All files now are modified and listed as LOCKBIT file type. Alternatively, they may be listed as ABCD file type data. There is no way to open these files, and even after opening them, they’re displayed as a pile of corrupted symbols. The victim can find Restore-My-Files.txt document in every affected file folder. |
| Distribution | The ransomware spreads via deceptive emails and resides as a malicious email attachment. Other known distribution vectors are deceptive ads and malicious torrents. |
| Antivirus or anti-malware detection names | BitDefender (Gen:Heur.Ransom.Imps.3), Avast (Win32:Malware-gen), ESET-NOD32 (A Variant Of Win32/Filecoder.NXQ), Kaspersky (Trojan.Win32.DelShad.bqj), Ransom.Lockbit (Malwarebytes). See full list of detection names on VirusTotal. |
| Detection names (new variant) | BitDefender (Gen:Heur.Ransom.Imps.1), Avast (Win32:Fraudo [Trj]), ESET-NOD32 (A Variant Of Win32/Filecoder.NXQ), Kaspersky (Trojan.Win32.DelShad.chy), Ransom.Lockbit (Malwarebytes). See full list on VT. |
| Removal Method | Remove LOCKBIT ransomware manually or automatically according to your computing skills. We recommend using the automatic removal option. After deleting the virus, you may want to restore affected Windows OS components using RESTORO. |
| File Recovery Methods | Recover encrypted files using data backups (stored on external data storage devices). |
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
Ransomware operation in detail
An in-depth LockBit ransomware analysis was recently provided by McAfee Labs. According to researchers, this particular ransomware variant often relies on brute force attacks to infiltrate a web server containing an outdated VPN service. After gaining access to Administrator’s account, it isn’t hard to compromise the whole computer network with ransomware then. The attacker then would run a specific PowerShell command to download LockBit ransomware in a form of a .png file (rs35.png for .NET 3.5 version and rs40.png for .NET 4 version) from a compromised website.
The PNG file contains a header of a portable executable (PE), which is a .NET launcher. The file contains a lenghty AES-encrypted base64 string which contains the executable for the actual ransomware program.
The virus is designed to bypass User Account Control windows and access Service Manager, which helps to terminate unwanted processes (such as security programs), delete Volume Shadow Copies and Recycle bin contents. Some examples of services that LockBit attempts to stop are: Symantec Antivirus, Norton Antivirus, Apache TomCat, and others. The virus then starts the encryption procedure, and drops ransom notes along its way through the system.
LockBit ransomware also creates several keys on the infected system, containing values full and public. These keys will be saved to HKEY_CURRENT_USER\SOFTWARE\LockBit. The purpose of creating these keys is to identify the victim host in the future. Finally, the ransomware changes desktop wallpaper with the attacker’s message.
Lockbit launches a website to leak victims’ data
In September 2020, Lockbit ransomware operators introduced a double-extortion tactic to convince victims pay the ransom sooner, and launched a data leak website to upload victims’ files. To understand what do we mean by saying “double-extortion”, let us explain how the majority of ransomware viruses operate.

Previously, the main factor that many ransomware developers used to leverage for their benefit is victim’s fear to lose access to personal files forever.
However, in 2020, cybercriminals introduced another tactic to push victims (home users and companies) even harder – they threaten to leak information stolen from computers online. This is known as double-extortion tactic.
The administrators of the infamous virus have posted a link in a dark web forum, leading to their new domain that is supposed to publish leaked data from victimized companies.
Lockbit ransomware operators were confirmed members of MAZE ransomware cartel, sharing their experience as well as data leakage site. However, for unknown reasons they have decided to release their own leak site.
The site currently contains links to published files stolen from two companies:
- Yaskawa Electric Corporation. Japanese manufacturer of servos, motion controllers, industrial robots, switches and AC motor drives.
- Overseas Express. Shipping company. Leaked data includes 5.8 customer records (full customer data leak), contains names, addresses, phone numbers, emails, tracking numbers and other data.
Ransomware distribution explained: how to protect yourself or your company?
Ransomware threats such as LockBit virus or other similar malware (STOP/DJVU, PHOBOS, NEMTY) can spread via traditional distribution channels such as:
- Infectious email attachments – obfuscated PDF, Word documents and other file types. Such emails typically have official-looking subject line and claim to deliver certain business-related document, such as invoice, report or similar. However, even if the attachment isn’t an EXE file, capabilities of documents nowadays allow insertion of JavaScript or Macros, both capable of downloading and executing an external file – malicious payload.
- Illegal downloads. Ransomware type threats can also be downloaded by the victim himself, in case one decides to get an illegal software version and activate it using a crack or keygen. One specific malware known to be using this particular distribution method is DJVU. Victims usually download the files via peer-to-peer download agents, for example, Torrent or eMule.
- Infected websites. Visiting compromised websites and clicking on a wrong link can instantly download malware to victim’s computer.
However, nowadays malware developers rely on a wide-range of intrusion tools. Often times, they leverage vulnerabilities in the target system (such as outdated software, weak security policy and practices in a company) to hack into the system and manually infect the computer network.
Therefore, following best cyber security pratices nowadays is simply a must. Needless to say, you should only rely on official software download channels, use the latest versions of software and operating system, and avoid clicking on suspicious links/attachments when surfing the web. In addition, using a trustworthy anti-malware software with real-time protection is simply a must. To learn more about ways to avoid ransomware, please read this guide.
LockBit ransomware developers push new versions
As mentioned earlier, Lockbit ransomware pushes new versions as it is being sold as Ransomware-as-a-Service on the dark web. Therefore, any criminal with sufficient hacking knowledge can join the affiliate program and use the ransomware toolkit to push the virus for a broader audience. Cybersecurity experts have observed and analyzed changes to the virus’ variants, all listed below.
The initial version
The initial version of Lockbit ransomware uses .abcd file extension to mark encrypted data. A screenshot of folder with affected files is presented below.

Text presented in Restore-My-Files.txt ransom note:

February 2020 version uses .lockbit extension
In February 2020, cybersecurity researchers notice a new variant of the virus which now marks encrypted files with .lockbit extension. The new version still uses Restore-My-Files.txt ransom note, but now points victims to a payment website available via Tor browser.
Screenshot of file folder affected by Lockbit ransomware new variant:

The slightly altered ransom note contents are shown below.

The link given in the ransom note says to download Tor browser and access a provided website. The website includes a chat box which can be used to contact cybercriminals.

New versions can self-replicate
In May 2020, security researchers notice a new change in ransomware, which is now capable to self-replicate. Therefore, all computers on the same network will be affected by data encryption procedure. The virus connects to them via SMB (Server Message Block Protocol), then runs aforementioned Powershell commands to download and execute LockBit ransomware. As a consequence, after infecting more computers, the ransomware developers can ask for a larger ransom.
It has also been noticed that new versions of the virus change desktop’s wallpaper with the one presented below.

LockBit 2.0 version (July 2021)
LockBit 2.0 ransomware is an updated variant that first emerged in July 2021. The malware uses AES + ECC to encrypt victim’s files and also uses .lockbit extension to mark locked files. The virus drops Restore-My-Files.txt ransom note, launches LockBit_Ransomware.hta file in a pop-up window, and changes victim’s desktop wallpaper with a ransom note-displaying image as well.

Remove LockBit ransomware safely and restore your files
If your computer has been infected, you must remove LockBit ransomware remains and check for additional malware on your computer. For this matter, we strongly recommend you to use the instructions given below and boot your PC into Safe Mode with Networking, then run (or if you don’t have, download) an anti-malware to delete all threats from your computer.
Only after a successful LockBit virus removal you can plug your data backup device into the computer and start recovering your files. If you notice that the virus has damaged your Windows operating system files, you can repair them using RESTORO.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS

Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
LockBit ransomware virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
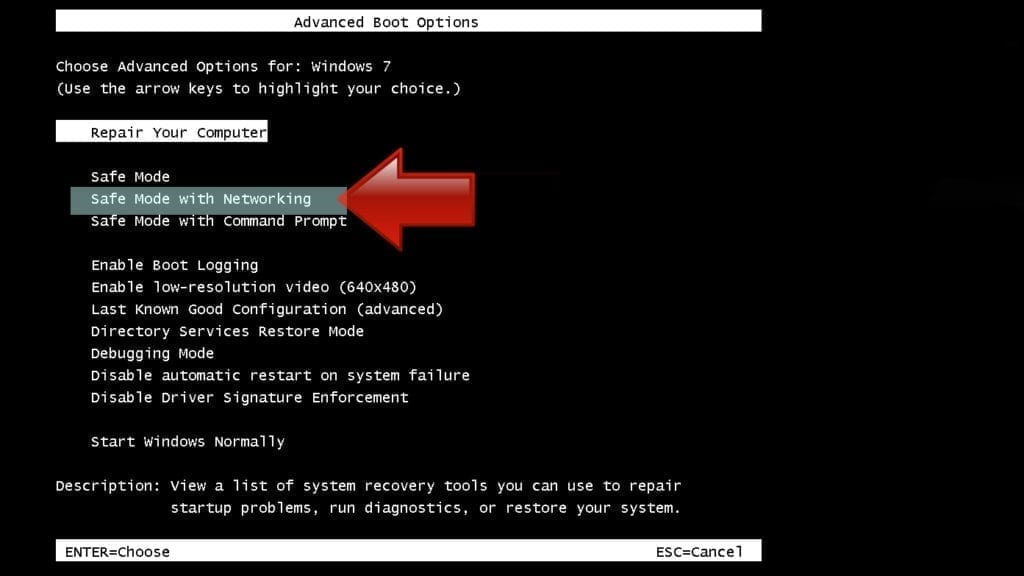
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

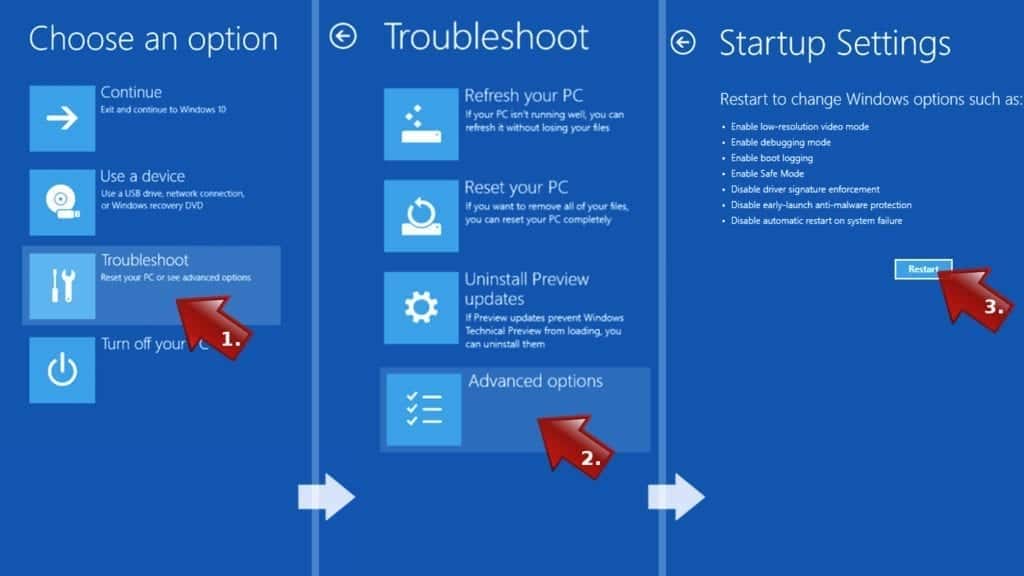
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
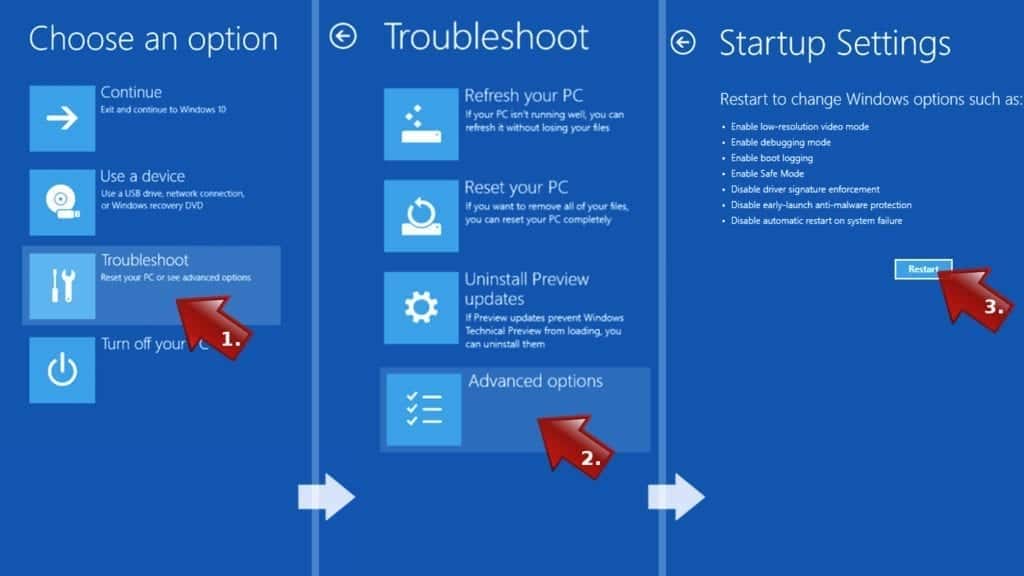
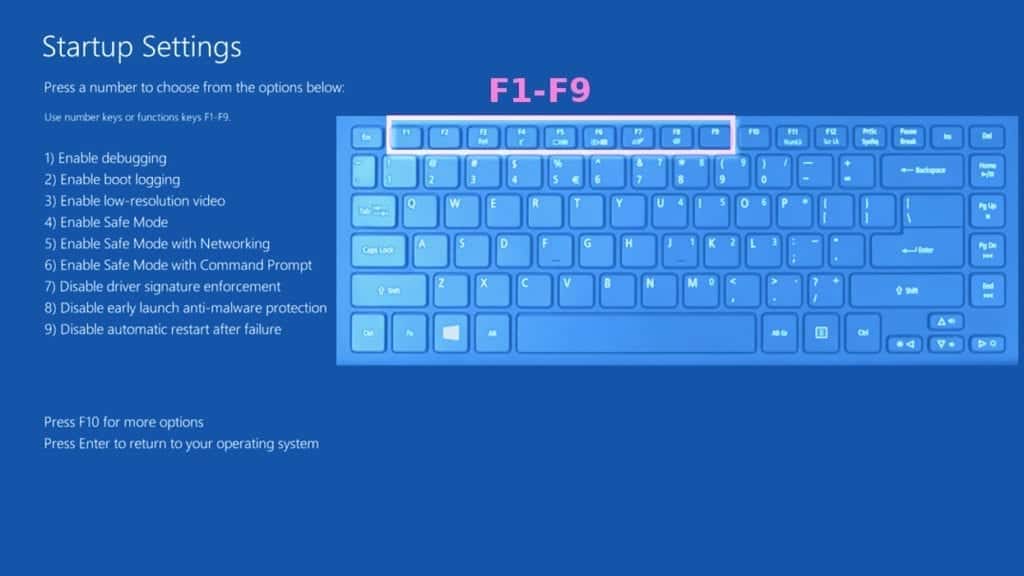
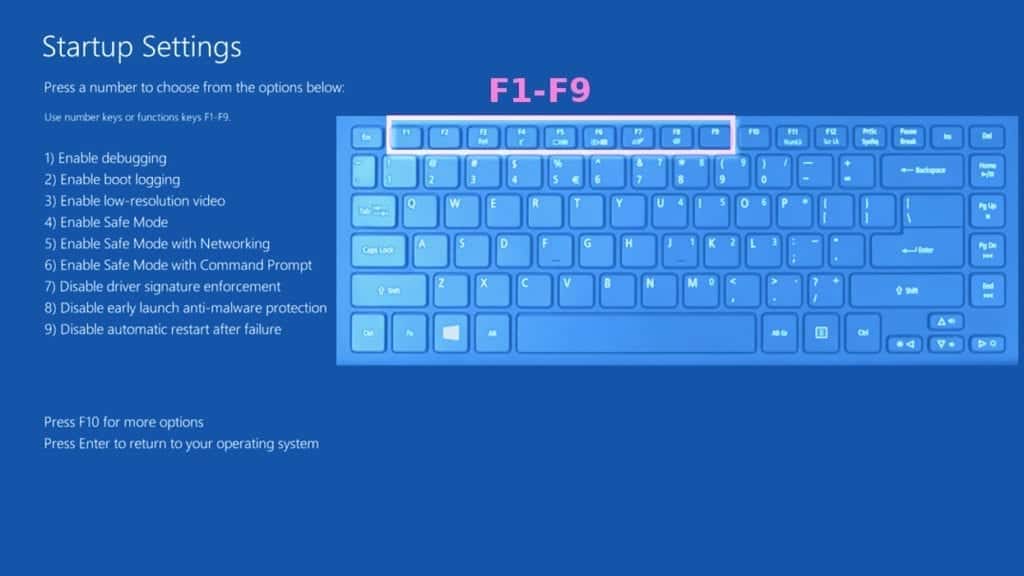
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove LockBit ransomware virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
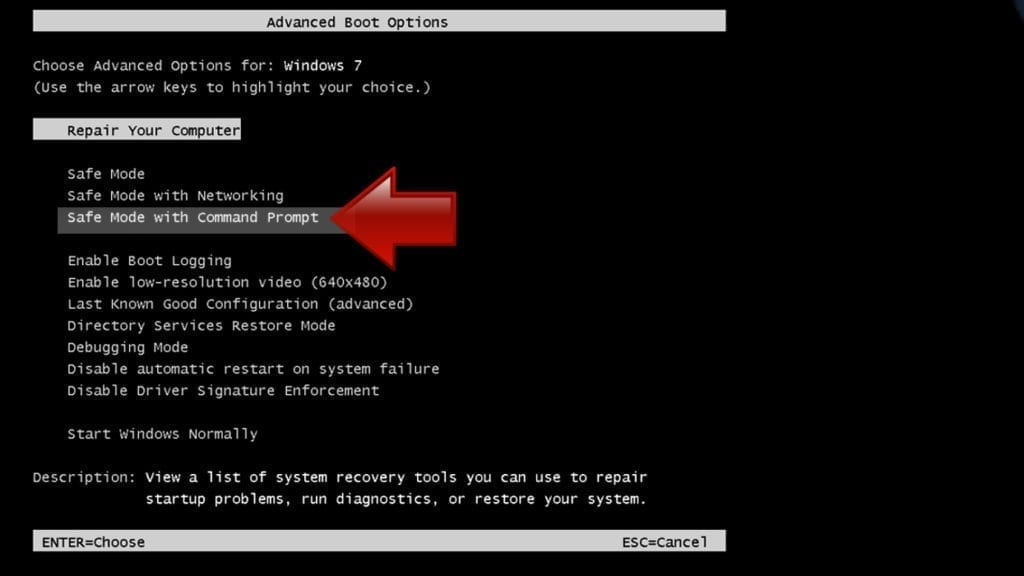
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
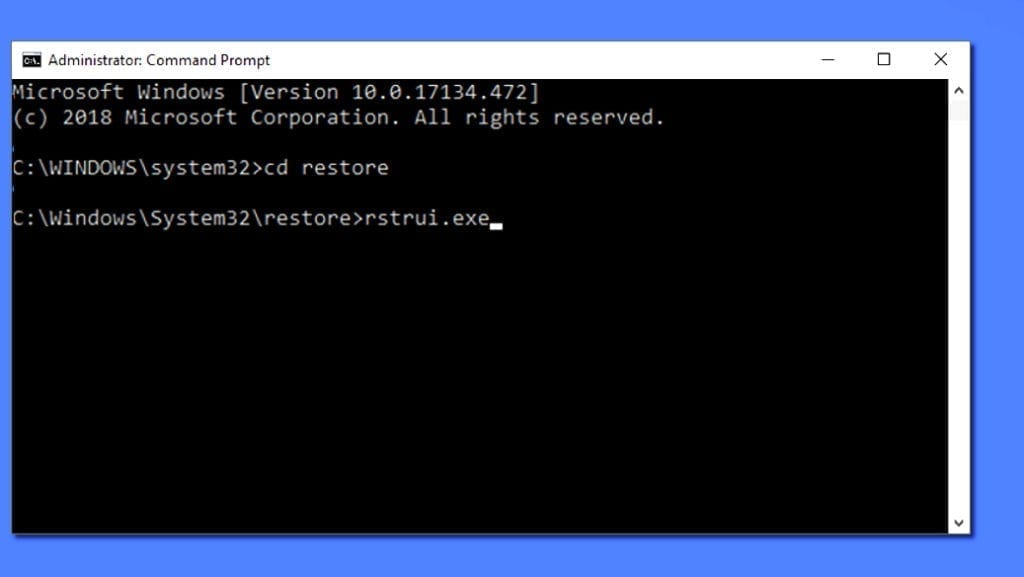
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
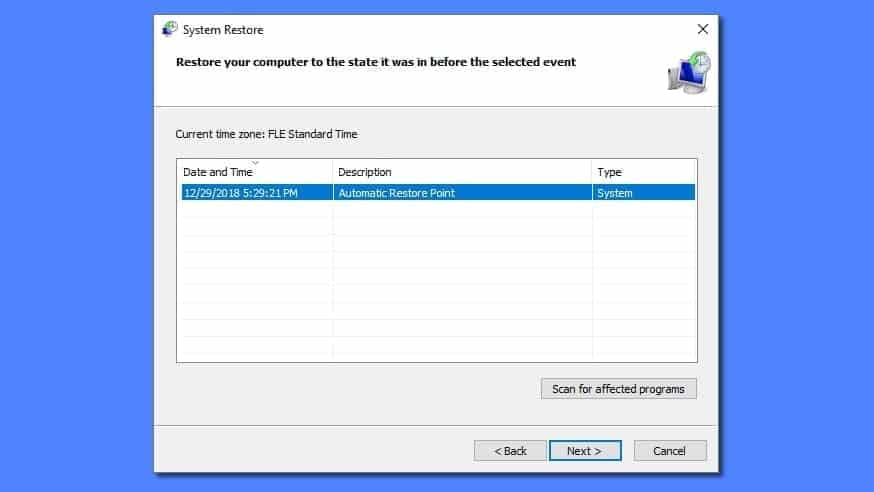
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
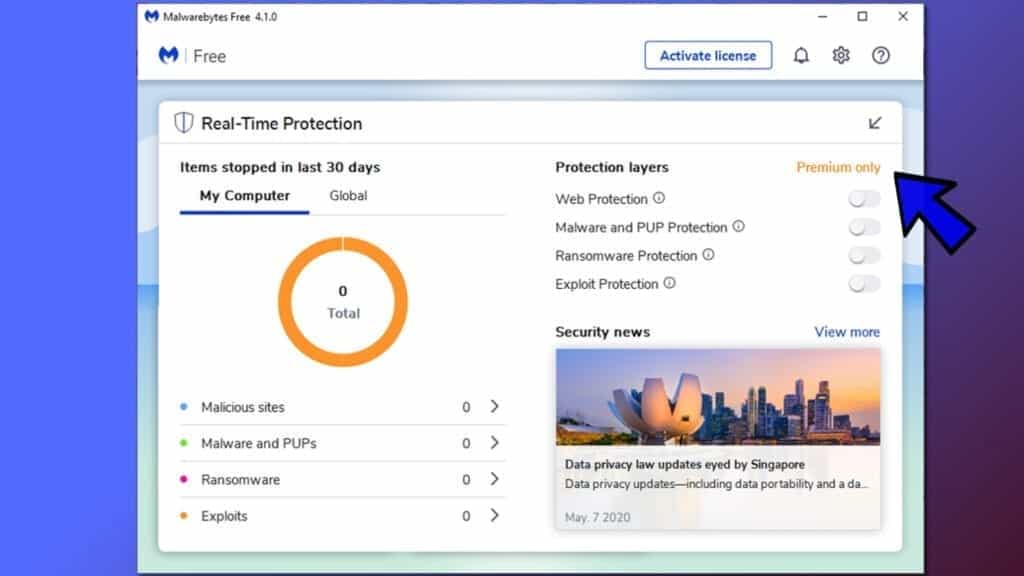
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
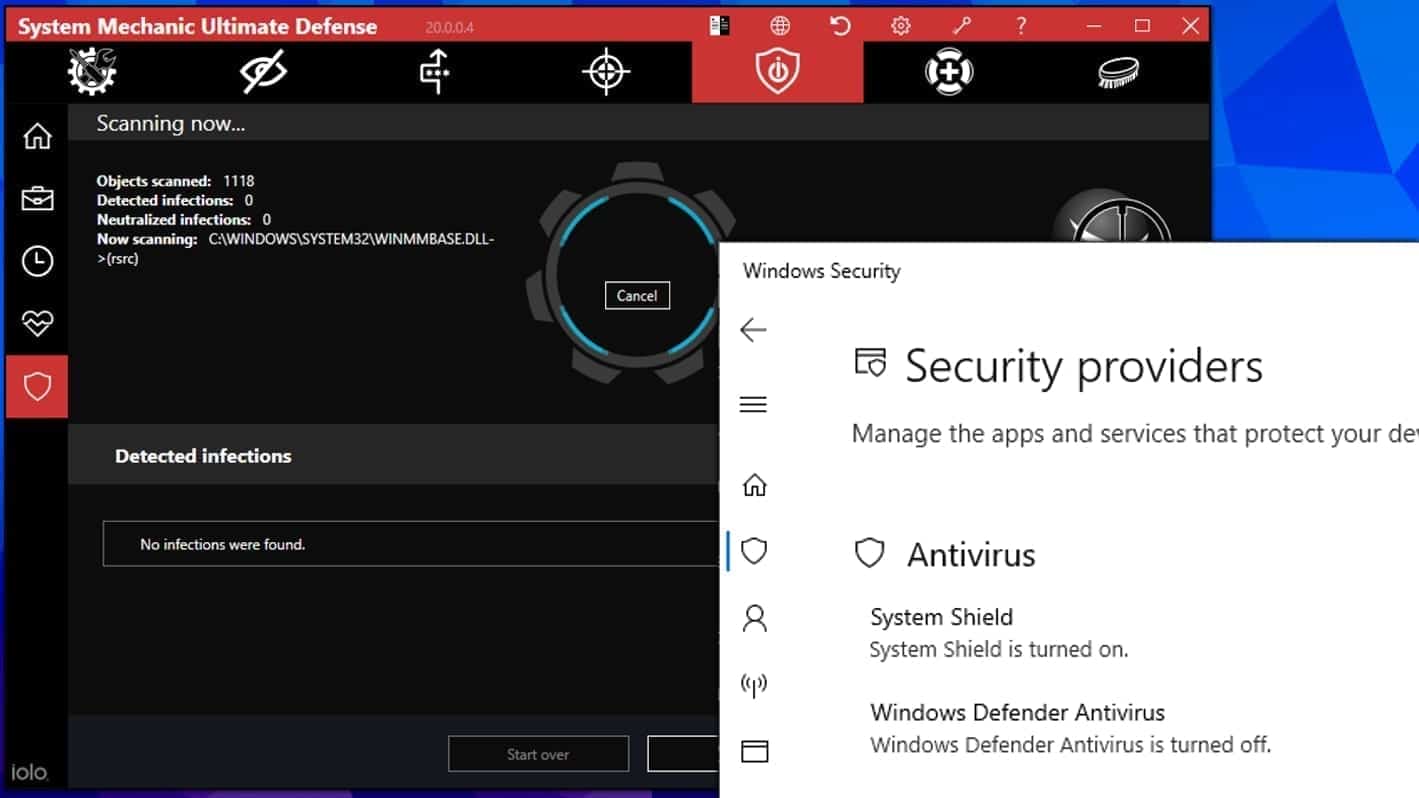
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
Estamos en la misma situación, necesito el software. Por ayuden a las personas que realmente lo necesitan.
My important files are locked by . lockbit extension. I need software through which I can remove. .lockbit extension.