Remove FRESH Ransomware (Virus Removal Guide)
Fresh ransomware makes your files inaccessible by using cryptography
Contents
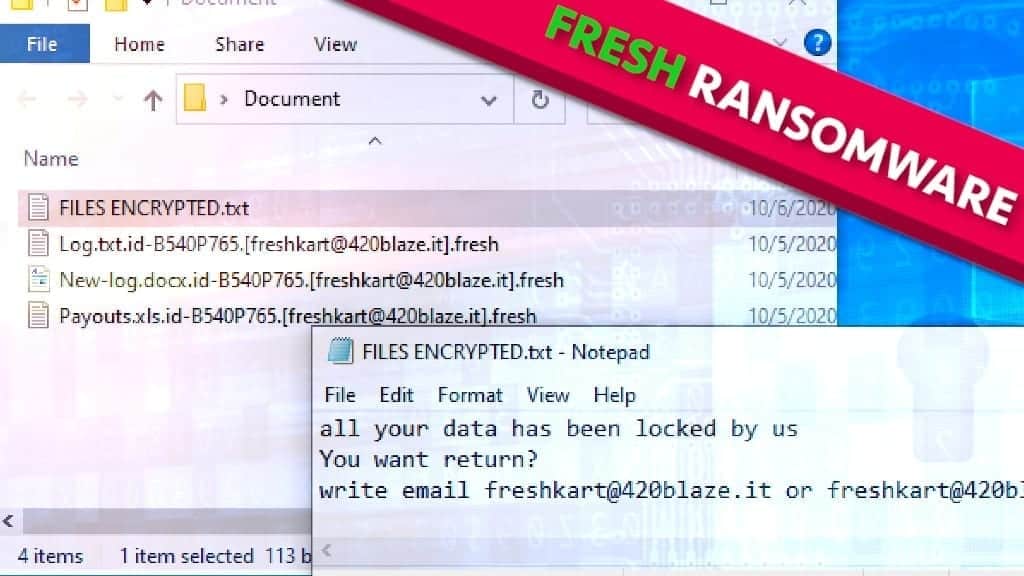
Fresh ransomware is a new variant of DHARMA ransomware – this virus family uses a combination of RSA-AES cryptography to deny access to your files and developers of this malware demand a ransom in order to revert these changes. The corrupted files can be identified easily since the virus marks them with a combination that consists of victim’s ID, cybercriminal’s contact email address and .fresh extension. For example, the encrypted file may appear as 1.jpg.id-144314.[freshkart@420blaze.it].fresh after the attack. Following the file encryption, a ransom note called FILES ENCRYPTED.txt appears in every affected folder. This message states that all of your files have been encrypted. It also contains instructions on how to supposedly resolve this situation. Another message from the criminals is launched as info.hta file on the screen.
Ransom note contents: pay the price to access your files
After the intrusion and successful encryption, hackers leave ransom notes in every affected folder, as well as the desktop. This file contains an unambiguous message – either you pay the price demanded a chance to regain the access, or you lose your files permanently. In addition, the hacker‘s contact email is provided which is freshkart@420blaze.it. The user is also encouraged to make a trial test – sending one encrypted file to the email provided and later receiving it back decoded.
It is currently unknown how much money the ransomware authors demand for file decryption tools. The victim is also forbidden from attempting any third-party decrypting software since it might damage the files. It is important to note, that all of these actions are designed to provoke panic from the victim so that he would do rushed decisions.
Having this in mind, never make any contact with the cybercriminals for one simple reason: they are not trustworthy. These crimes are made by profit-driven people – if they see an opportunity to extort you more, they will do it.
Therefore, following their instructions might leave you with significant financial loss, that, even worse, might be completely pointless. Security experts receive many reports about cases in which the victim is left with nothing even after the payment is made. When dealing with these kinds of situations remember, that there is simply no guarantee that you will receive the promised decryption tool.
What has been done to your files
To understand the whole Fresh ransomware concept better, first of all, you need to have some context knowledge on what RSA-AES encryption is. RSA-AES is a cipher technology that was created to safely transmit data between military peers. It is no exaggeration when people call it military-grade cipher since it was used by various countries’ militaries. Every single act of using it creates a unique encryption/decryption key that is in the message sender’s possession.
Unfortunately, there is no real way to regain access to the affected files if they have been touched by RSA cipher unless you posses the previously mentioned key. However, as more and more ransomware variants emerge, novice hackers tend to leave mistakes inside their code which could be exploited in the victim’s favor. Nonetheless, that is rarely the case, so the only viable option might be to remove Fresh ransomware from your system and then importing lost files from a back-up.
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
| Name | FRESH ransomware |
| Type | Ransomware; File-encrypting virus, File Locker |
| Family | DHARMA/CrySiS |
| Versions | XATI, LINA, LOG, BLM, DATA, FLYU |
| File Extension | .fresh |
| Executive file | e065bd3d92d7026c56862d11914d10d6.exe or similar |
| Detection names | Trojan.Ransom.Crysis.E (Bitdefender), Ransom:Win32/Wadhrama!hoa (Microsoft), Ransom.Crysis (Symantec), W32.Ransom.Gen (Webroot) and similar |
| Ransom Note | FILES ENCRYPTED, info.hta |
| Contact emails | freshkart@420blaze.it |
| Damage | Locks victim’s personal files (documents, photos, music/videos) using cryptographic algorithms, then leaves ransom-demanding notes across the computer. Erases VSS (Volume Shadow Copy Service). |
| File decryption | Try suggested file restoration software first. |
| Removal | Remove the virus using robust software like anti-malware. For virus damage repair, scan the system using RESTORO |
Ransomware is becoming a widespread threat to your security
If you wonder how it is possible to get infected by virus like Fresh, you need to understand the basic principles of malware-spreading. Nowadays, cybercriminals tend to get creative and find more unusual ways to scam you but some of the methods are circulating on the internet for years. For example, downloading from unofficial, unverified websites and file-sharing platforms like zMule, ThePirateBay or Mediafire could leave you exposed to harmful actions initiated by hackers.
Keep in mind, that when talking about illegal software downloads (like keygens, activation tools, cracks, etc.) nothing comes free, even if it is advertised as such since you might pay the price at the expense of your system’s security.
The other distribution method used by hackers is various forms of adware – whether that is intrusive ads or browser hijackers. For example, pressing on a pop-up ad when you surf the internet might trigger a browser hijacker infection that changes your default browser’s settings. After that, it is possible that it might trigger chain infection (downloading additional malware).
Last but not least – Fresh ransomware might spread through malspam campaigns. To explain, it is a pretty straightforward social-engineering scheme that sends thousands of deceitful emails to random internet users. These emails are designed to trick the person into clicking on a link inside it or a file attached to it. Once that is done, a virus might get inside your system. So we recommend you always check your emails carefully and do not open any suspicious-looking links or files inside of them.
Remove Fresh ransomware
If you see any signs of being infected with this ransomware, you should take immediate action to complete FRESH virus removal. Having present malware in your system for extensive periods of time is extremely dangerous – the more time it has, the more damage it can deal with, plus it can provide ways for other malware to sneak in.
For this reason, we recommend you use RESTORO – this PC repair software not only is capable of dealing with tasks such as this – it also possesses the necessary capabilities to help your system heal itself. To remove Fresh ransomware follow the steps provided below. Please be extremely careful not to miss any step and ensure secure malware elimination from the system.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
FRESH ransomware virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove FRESH ransomware virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
REMOVE MALWARE & REPAIR VIRUS DAMAGE
1 Step. Get robust antivirus to remove existing threats and enable real-time protection
INTEGO Antivirus for Windows provides robust real-time protection, Web Shield against phishing and deceptive websites, blocks malicious downloads and blocks Zero-Day threats. Use it to remove ransomware and other viruses from your computer professionally.
2 Step. Repair Virus Damage on Windows Operating System Files
Download RESTORO to scan your system for FREE and detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
Matt Corey is passionate about the latest tech news, gadgets and everything IT. Matt loves to criticize Windows and help people solve problems related to this operating system. When he’s not tinkering around with new gadgets he orders, he enjoys skydiving, as it is his favorite way to clear his mind and relax.
Recent Posts
Remove WDLO Ransomware Virus (DECRYPT .wdlo FILES)
WDLO ransomware uses encryption to lock your personal files WDLO ransomware is a malicious computer…
Why You Need a VPN and How Does It Protect You?
What is a VPN and how does it work? The term VPN stands for Virtual…
Remove PPHG Ransomware Virus (DECRYPT .pphg FILES)
PPHG ransomware encrypts your computer files, threatens to keep them locked until a ransom is…
Remove SSOI Ransomware Virus (DECRYPT .ssoi FILES)
SSOI ransomware aims to lock all of your data on a computer and then extort…
Remove KKIA Ransomware Virus (DECRYPT .kkia FILES)
KKIA ransomware sneakily encrypts your files KKIA ransomware is a newly emerged computer virus that…
Remove HFGD Ransomware Virus (DECRYPT .hfgd FILES)
HFGD ransomware aims to take your computer files hostage HFGD ransomware is a malicious malware…