Wacatac Trojan – real threat or false positive?
Contents
Wacatac Trojan (alternative name Trojan:Win32/Wacatac) is a malicious computer virus which is usually used to steal private and sensitive information from ordinary user in order to exploit him financially. This threat often comes with various illegal torrent-based downloads and is typically quarantined by user’s computer’s security software. The name of this Trojan is more of a generic threat detection name, signaling about malware that could possibly steal your passwords, open specific ports, drop additional malware and complete other harmful actions on your computer. Therefore, it is crucial to know what actions to take if you have encountered wacatac.b!ml virus detection in the first place.
Some users wonder is wacatac a false positive or not. The truth is, if you have come across this threat’s detection name, you probably have downloading something suspicious from the internet, most likely a software crack, movie or another piece of software that raised suspicion for your computer’s security software. Our general recommendation is that you should always stay on the safe side and quarantine and remove any suspicious downloads marked as suspicious by your antivirus. Otherwise, if you ignore these warnings, you risk losing private data and even access to your files.
Wacatac virus’ characteristics
As previously mentioned, Wacatac is a Trojan virus. People usually get infected with it through various spam email campaigns and illegal software downloads (especially software or game cracks). This virus is typically used to steal victim’s information in order to receive some financial gain. As soon as the intrusion to your system happens, this software starts to collect and transmit your sensitive information, such as bank account information, logins and other personal information. Collected data may be transferred to criminals C&C server.

Additionally, you should know that Trojan viruses are so immensely dangerous because of the fact that they are designed to intrude victim’s system stealthily and remain silent, therefore such viruses might remain active and unnoticed for long periods of time. This malware might also trigger so called ‘chain infections’ and these are notably dangerous – chain infections might download even more malicious programs, malware and ransomware (such as DJVU) to your system thus making your PC completely unusable.
Trojans are notorious for many other abhorrent capabilities as well, such as connection to botnet or dropping a cryptocurrency miner on compromised system. In this case, your desktop’s resources will be used extensively to reach a certain goal, which might end up in permanent damage to the hardware. For this reason, it is essential to take actions to remove Wacatac Trojan as soon as possible. We recommend using malware removal software of your choice and finalising the removal procedure with software like RESTORO.
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove detected issues manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
Threat Summary
| Name | Wacatac |
| Type | Trojan |
| Detection Names | Trojan:Win32/Wacatac.D!ml, Trojan:Win32/Wacatac.a!ml |
| Associated processes | biddulphia9.exe |
| Symptoms | Acts silently: steals private data (passwords, logins, banking details, etc.), installs additional malware |
| Danger | Might cause private data or financial loss, damage personal files |
| Distribution | Malicious email attachments or links, infected websites, untrustworthy online downloads (peer-to-peer file sharing sites) |
| Removal | Remove using trustworthy anti-malware, then scan with RESTORO. |
Trojan distribution techniques
Firstly, previously mentioned spam email campaigns are designed to send huge amounts of malicious emails in the hope of corrupting their systems with certain software. These emails might contain various information, from trade/business requests, to job CVs and notifications from dating websites, in order to trick you into downloading or opening certain files or links. This might end in breach of your computer’s security system.

In other words, pretty much all of your computer data gets compromised and might be used to exploit you financially. So, getting infected by email is easier than one might think – in some cases, especially without proper security system on your PC, the infection could happen due to a single press on a link. Because of this, the problem is widespread, and many users suffer from Trojans such as Wacatac.

The other method which is used by cyber criminals is the proliferation through illegal cracks and other downloadable software. This approach is aimed more at people who tend to download from the internet inattentively. To explain, there’s a lot of internet users who still use various file sharing networks (i.e. eMule, Torrent, zippyshare etc.) carelessly. This also contributes to the fact that Trojan viruses like the discussed one or AZOrult are so widespread.
Infecting victim’s computer through installation, especially with .exe files is the easiest way for the intruder. In short, you should mind that almost nothing comes free through illegal downloads from the internet.
Usually, when choosing to download something free, instead of paying the price to the product creator, you simply face the danger of getting your system infected with viruses such as wacatac.b ml Trojan. In order to avoid the problems catalyzed by this virus, you need to do keep in mind a couple of things. Do not open suspicious-looking links in emails and files attached to them and do not download software from unreliable sources.
Since Trojans are designed to slip into user’s system unnoticed, you can never be sure if you have it or not, therefore it won’t hurt to check your system.
How to detect and remove Wacatac Trojan easily
If your antivirus alerted about detection of the described Trojan, do not hesitate and take recommended actions to remove Wacatac Trojan as soon as possible. Additionally, we strongly recommend downloading RESTORO to repair virus damage on your computer system caused by the Trojan.
To carry out complete wacatac.b!ml removal we recommend following the steps listed bellow attentively. Even if you suspect that you antivirus shows trojan:win32/wacatac.b!ml false positive, it typically means that the suspected software shares code similarities with the infamous virus, so you need to double check it.
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS

Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
WACATAC TROJAN Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in Safe Mode with Networking, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to start Windows in Safe Mode:
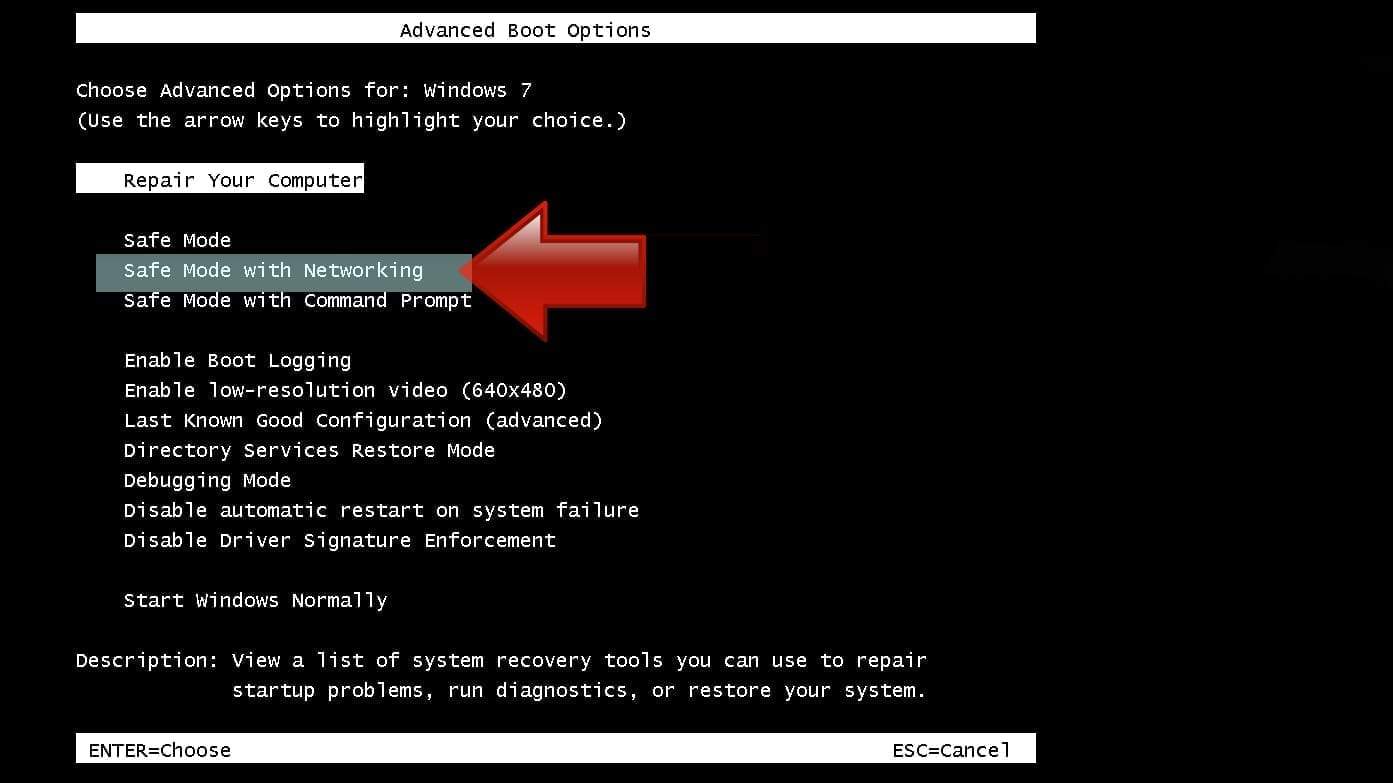
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
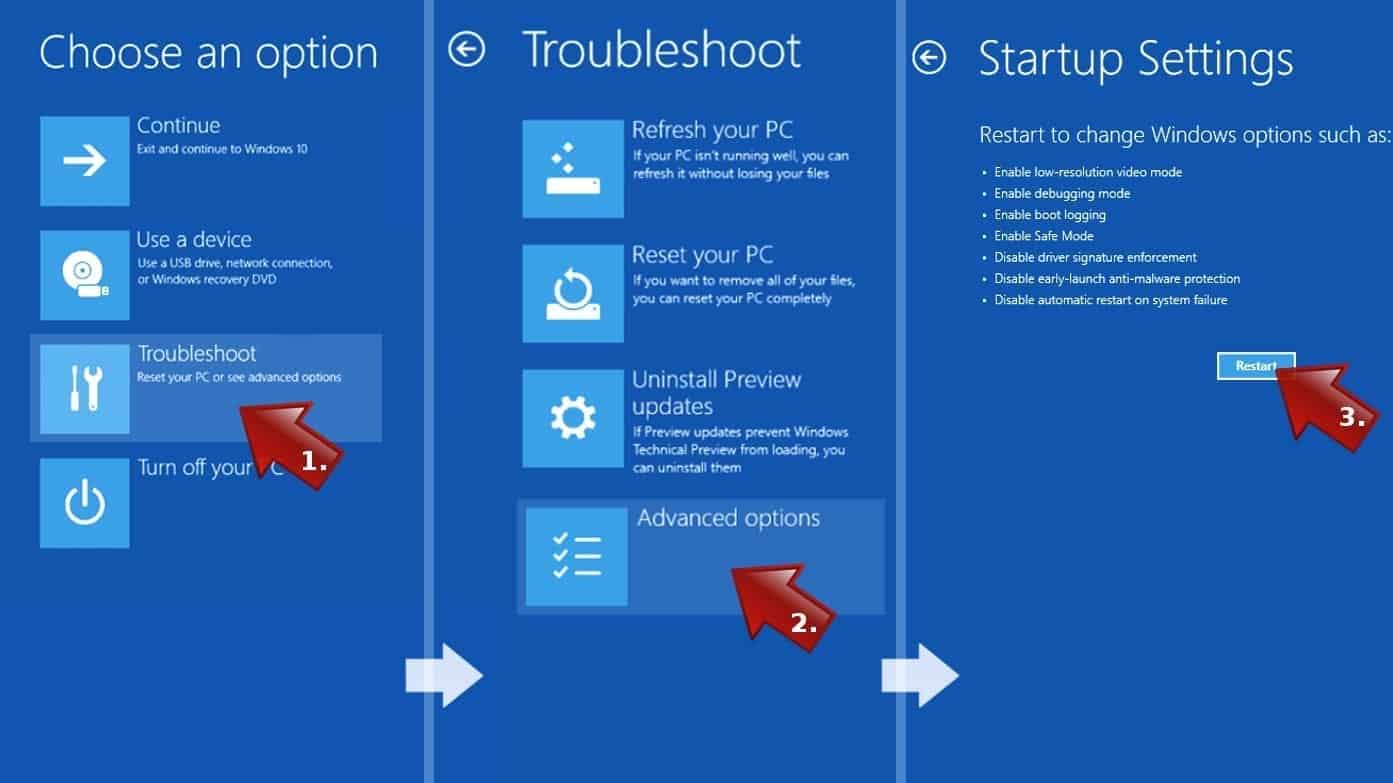
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

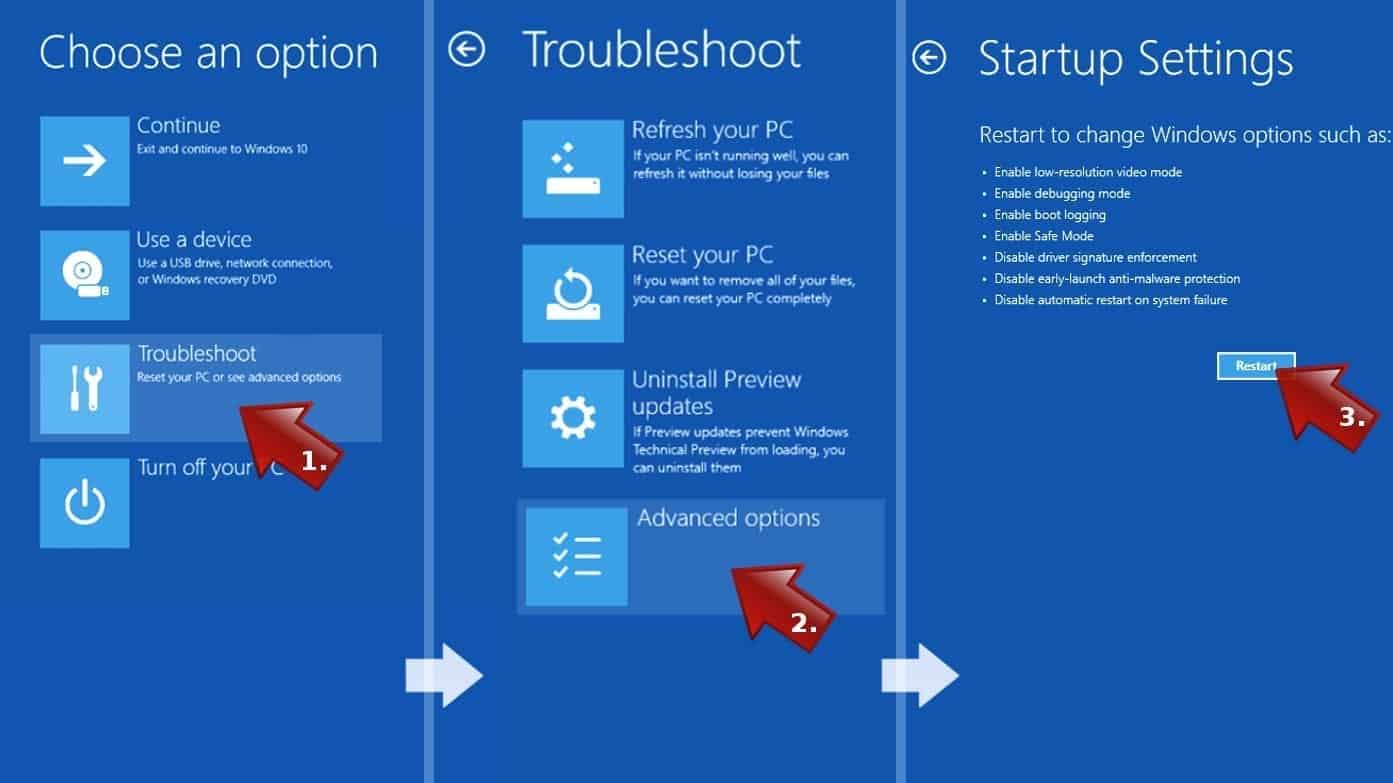
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
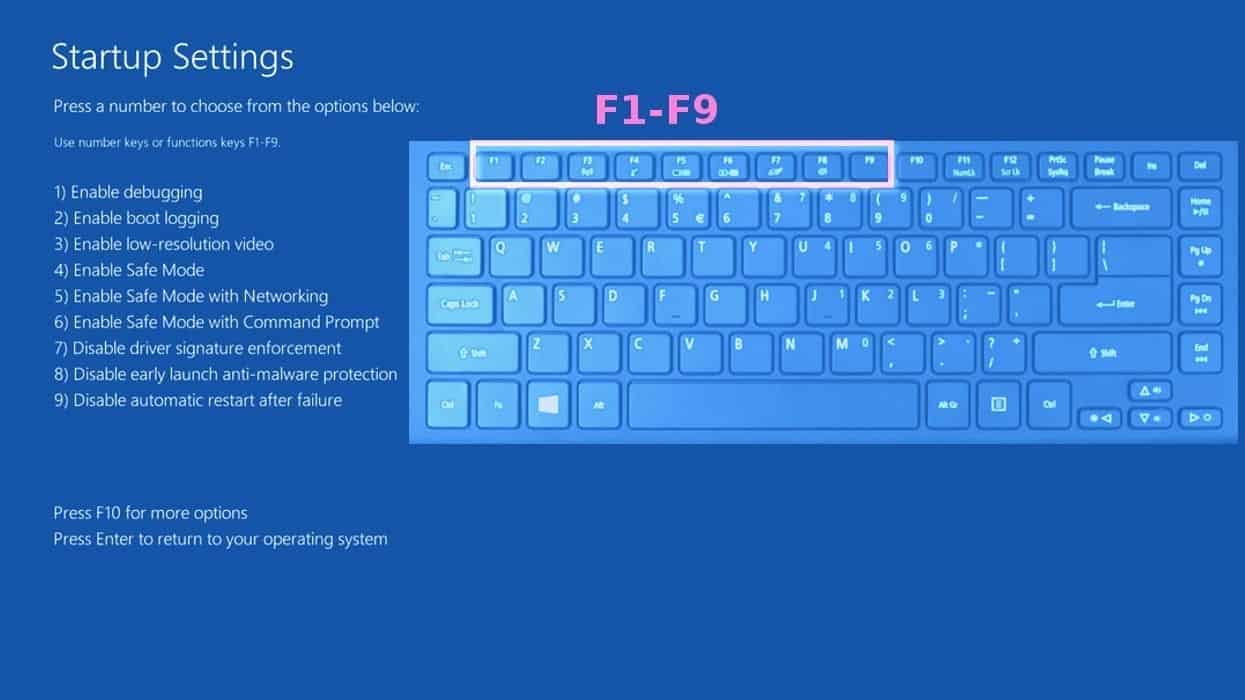
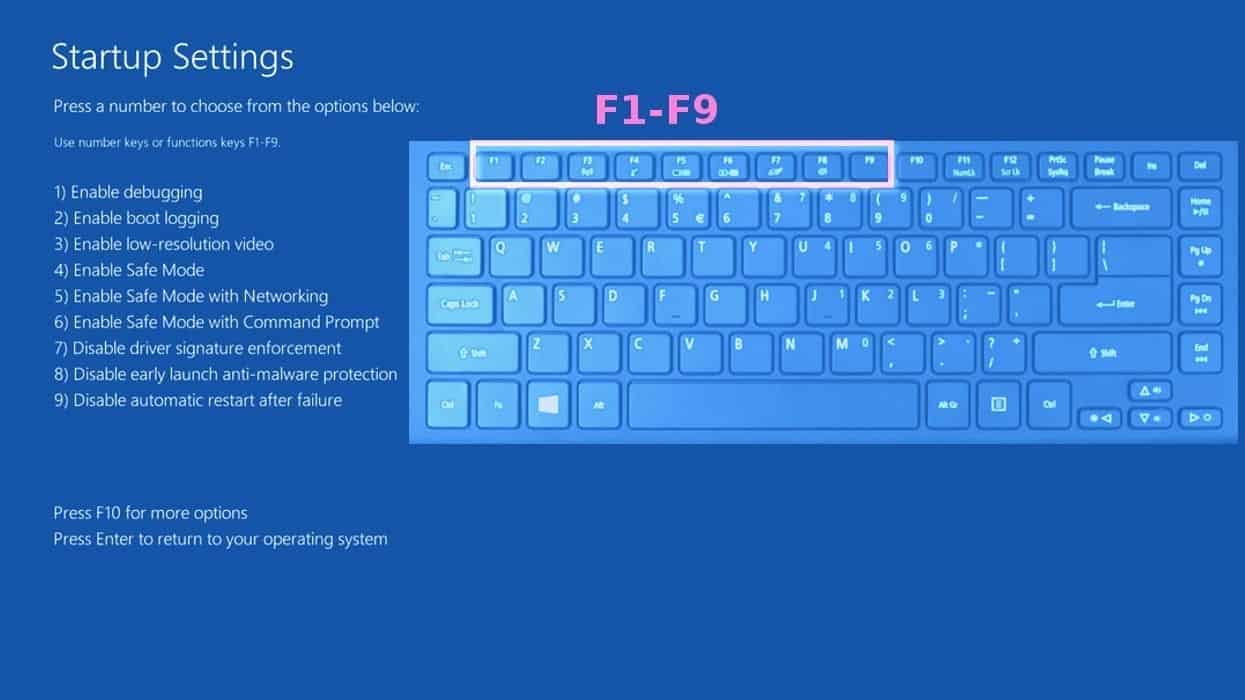
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove WACATAC TROJAN files. It is very hard to identify files and registry keys that belong to the virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. We recommend using SYSTEM MECHANIC ULTIMATE DEFENSE , which can also restore deleted files. Additionally. we recommend repairing virus damage using RESTORO.
Special Offer
Compatibility: Microsoft Windows
See Full Review
RESTORO is a unique PC Repair Tool which comes with an in-built Avira scan engine to detect and remove spyware/malware threats and uses a patented technology to repair virus damage. The software can repair damaged, missing or malfunctioning Windows OS files, corrupted DLLs, and more. The free version offers a scan that detects issues. To fix them, license key for the full software version must be purchased.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
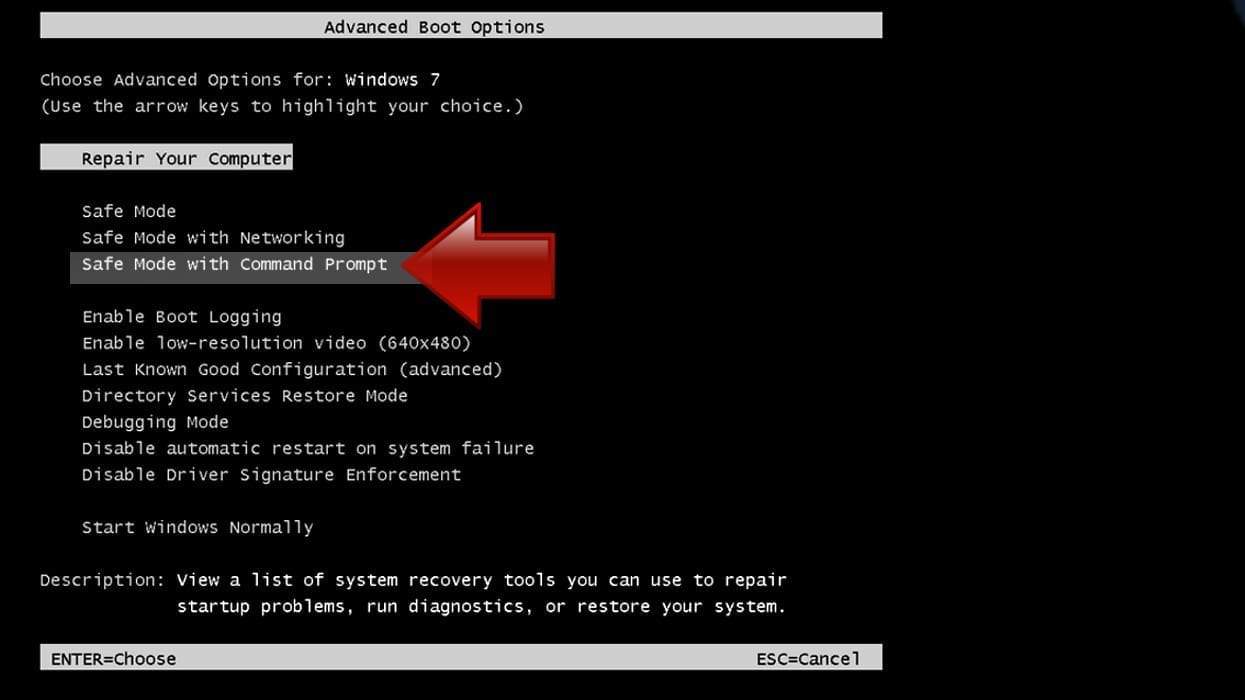
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.

- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before the malware infiltration.
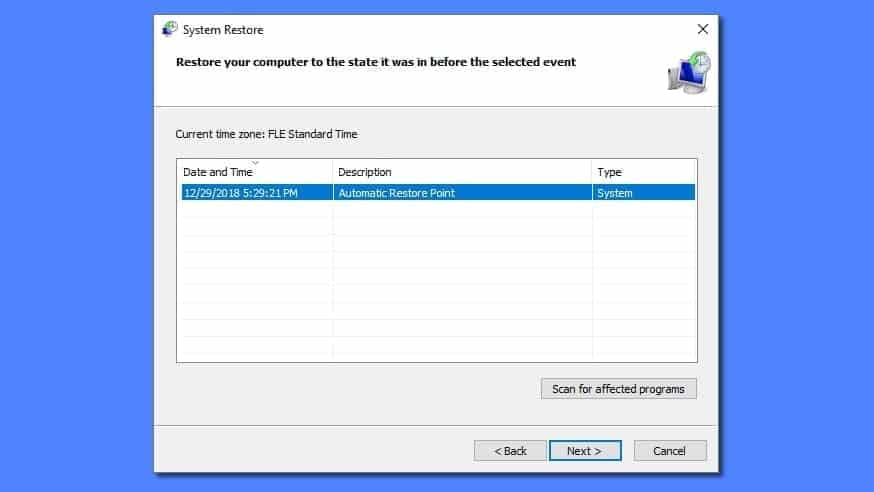
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
Something you can have as a note. I play online PC games and use legal addons from curse forge /overwolf website and app. I was updating my addons today and apparently they have malware scripts like this one. I did get infected and took all necessary actions immediately but it may have been too late from infecting my network. I have been fixing it all day. So i read this article and will try Restoro. So i just want to put the message out there about the site and for people to really pay attention and understand what can happen. Maybe you can spread the word also. Thank you for the post article. Very informative.