Remove Occamy Trojan (Virus Removal Guide 2021)
Occamy.C virus is dangerous remote access Trojan
Contents
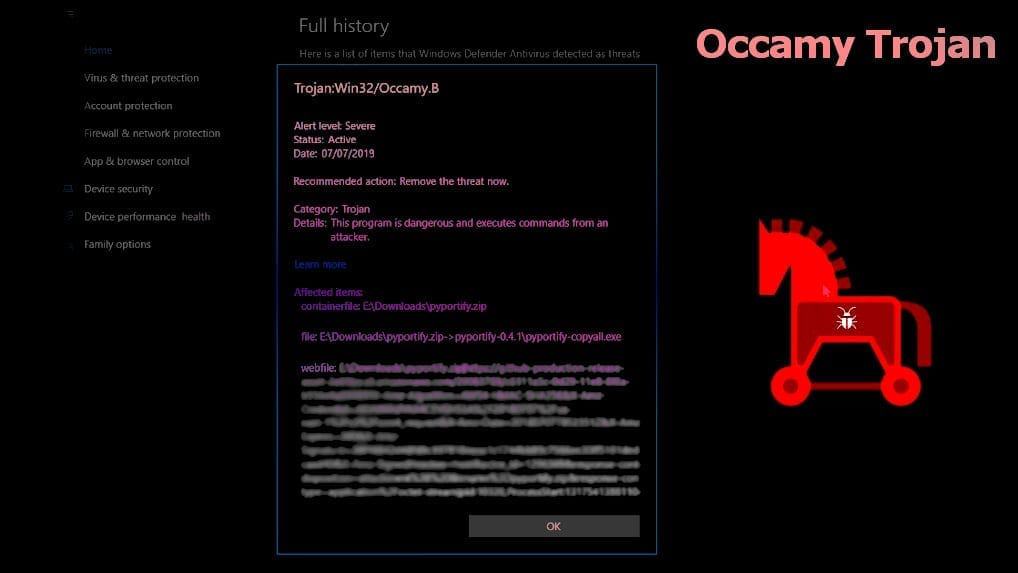
Occamy Trojan (also known as Occamy.C virus) is a computer malware designed to provide remote cyber criminals with remote access to the system. Various antivirus programs, as well as Windows Defender, detect this threat as Trojan:Win32/Occamy.C or Trojan:Win32/Occamy.B. The known executive file of this virus is nc.exe, but also can be named differently – lchrjspt.exe. Users mostly download this threat during piracy activities, such as downloading software crack or keygen.
Occamy Trojan is designed to work as a remote access program. Therefore, the cyber criminal behind it can use it to perform various malevolent actions on victim’s computer. See below for example activities similar viruses typically initiate on infected systems.
Some computer users on Reddit’s Piracy forum suspect Trojan Occamy.C to be false detection by Windows Defender. They often believe that such detections are nothing to worry about, however, However, we assure you that it isn’t, and if you noticed similar threat detection by Microsoft or another antivirus provider, take actions to eliminate the threat immediately.
Threat summary
| Name | Occamy Trojan |
| Also known as | Occamy.C, Occamy.B |
| Type | Remote Access Trojan (RAT) |
| Associated files | pyportify.zip, nc.exe, lchrjspt.exe |
| Danger | Very dangerous |
| Risk | Losing personal information, revealing login credentials, financial damage |
| Distribution | Software piracy: downloading cracks and keygens; opening infected email attachments, insecure web pages and downloads |
| Removal methods | Antivirus scan while in Safe Mode or System Restore. To repair virus damage on Windows OS files, consider downloading RESTORO |
| Additional details | Many users think Ocammy.C detection is a false positive |
Malicious activities by Occamy Trojan
- Disabling essential security programs;
- Data theft, for instance, passwords, login details, mouse/keyboard logs, web browsing history;
- Enrolling infected host into a botnet;
- Encrypting or corrupting files on infected system;
- Controlling and monitoring infected computer’s camera and microphone for eavesdropping and possible blackmail;
- Dropping additional malware on the system.
Victims who suspect that the system might be infected with Occamy malware should immediately start their computer in Safe Mode, then activate and run trusted antivirus software. If you don’t have one yet, consider choosing Safe Mode with Networking and download one. You might want to check our software reviews section first.
Trojan distribution tricks
The majority of victims report founding Occamy Trojan on their computers after using software cracks or keygens downloaded from the Internet. This is nothing new, as these type of downloads are used to spread malware very frequently. For example, one of the most prevalent ransomware infections of 2020 that uses this distribution method is STOP/DJVU.
What is more, Occamy virus is often distributed via fake email spam campaigns. Typically, such campaigns leverage the name of well-known companies and pretend to be reaching out on their behalf. People are curious; unfortunately, attempts to please curiosity is mostly what results in unwanted system infection.
Such scam emails typically encourage the user to open the email attachment, which nowadays mostly comes in a form of a malicious Word document with code that can be executed by enabling Macros. If you fall for the trap and open such email attachment, consequently the malware will be downloaded and executed to run on your computer immediately.
You can also end up installing unwanted malware like Occamy.C by visiting highly untrustworthy Internet pages. Be aware that adult-industry and illegal download sites are the ones known to be serving malicious payloads most frequently. For your own safety, stay away from highly questionable sites and choose better web resources to explore instead.
What is more, it is ESSENTIALLY important to keep your computer OS and installed software up-to-date. Software developers issue updates to fix detected security vulnerabilities and overall improve general user experience, so there aren’t no reasons why not to install them. So do not postpone that Windows update – install it as soon as you can!
Remove Occamy.c Trojan virus manually
You can completely remove Occamy Trojan by using a trustworthy antivirus software. However, since this virus might attempt to disable security programs, you will need to boot your PC into Safe Mode first.
Below, we provide several methods to remove the discussed virus. You can either delete it using antivirus, or by rolling back your computer to a state prior the RAT infection. Alternatively, you can download RESTORO for fixing virus damage on default system components.
Please follow the guide provided below for succesful Occamy virus removal.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
Occamy Trojan Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in Safe Mode with Networking, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to start Windows in Safe Mode:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove Occamy Trojan files. It is very hard to identify files and registry keys that belong to the virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. We recommend using SYSTEM MECHANIC ULTIMATE DEFENSE , which can also restore deleted files. Additionally. we recommend repairing virus damage using RESTORO.
Special Offer
Compatibility: Microsoft Windows
See Full Review
RESTORO is a unique PC Repair Tool which comes with an in-built Avira scan engine to detect and remove spyware/malware threats and uses a patented technology to repair virus damage. The software can repair damaged, missing or malfunctioning Windows OS files, corrupted DLLs, and more. The free version offers a scan that detects issues. To fix them, license key for the full software version must be purchased.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before the malware infiltration.
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
Matt Corey is passionate about the latest tech news, gadgets and everything IT. Matt loves to criticize Windows and help people solve problems related to this operating system. When he’s not tinkering around with new gadgets he orders, he enjoys skydiving, as it is his favorite way to clear his mind and relax.
Recent Posts
Remove UIGD Ransomware Virus (DECRYPT .uigd FILES)
UIGD ransomware encrypts all files on a computer, asks for a ransom UIGD ransomware is…
Remove EYRV Ransomware Virus (DECRYPT .eyrv FILES)
EYRV ransomware takes your computer files hostage, demands a ransom EYRV ransomware is a destructive…
Private Internet Access Review 2022: Fast, Secure & Cheap VPN
Private Internet Access (PIA) VPN maintains its long-term role as a leader Private Internet Access…
Remove XCBG Ransomware Virus (DECRYPT .xcbg FILES)
XCBG ransomware aims to lock your files and demand a ransom XCBG ransomware is a…
Remove BPQD Ransomware Virus (DECRYPT .bpqd FILES)
BPQD ransomware encrypts all computer files, demands a ransom from the user BPQD ransomware is…
Remove KQGS Ransomware Virus (DECRYPT .kqgs FILES)
KQGS ransomware is a hostile computer virus designed to encrypt all of your files KQGS…