NPSG virus demands ransom for data decryption
Contents
NPSG ransomware is a new (201th) variant of STOP/DJVU file-encrypting virus. The virus is capable of encrypting all of victim’s personal files with RSA encryption, making files inaccessible. The virus appends .npsg extension to encrypted files and saves _readme.txt note in affected file folders. The note demands paying $490 or $980 to cybercriminals in Bitcoin. The cryptocurrency wallet address isn’t provided – the victim must contact the attackers via helpmanager@firemail.cc or helpmanager@iran.ir, both provided in the note. The said ransomware is known to install AZORULT password-stealing Trojan on Windows systems, and both must be removed as soon as possible.
NPSG extension virus is coded in a way that allows it to bypass security software. What is more, the malicious program can delete system restore points from the computer, making it impossible to recover any data from the corrupted system. The aim of this virus is to rip victim’s access to important personal or work data in a blink of an eye – all so just so that the victim would start considering paying the ransom.
The ransom demand is provided in _readme.txt note, which briefly informs the victim about the cyber attack. The note suggests that all files including documents and databases have been encrypted, and that the only possible data recovery option is the NPSG decryption toolkit offered by the cybercriminals. The toolkit includes a decryption software and a unique key.
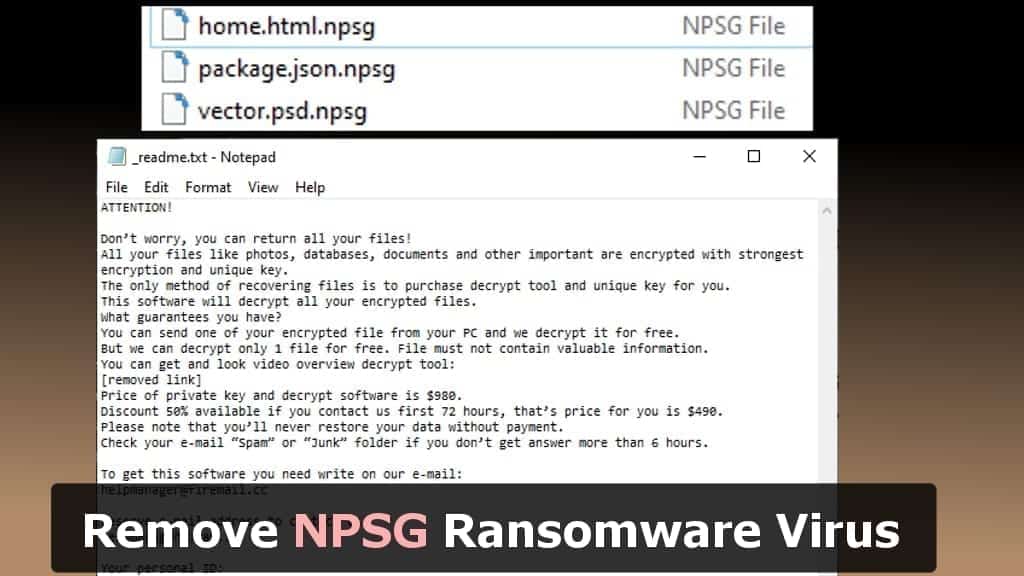
We, however, do not recommend paying the ransom to cybercriminals. By doing so, you simply encourage and support their filthy business model. What we recommend doing instead is taking care of the malware as soon as possible. You can remove NPSG ransomware virus and other malicious programs using instructions provided in this article.
Threat Summary
| Name | NPSG ransomware |
| Type | File-encrypting virus |
| Origins | STOP/DJVU (201th version) |
| Targeted systems | Windows |
| Behavior | Encrypts files, restricts access to them and demands paying a ransom (according to instructions in _Readme.txt file) |
| Extension | Appends .npsg file extension to files |
| Ransom note | _readme.txt |
| Ransom demand | $490-$980 |
| Emails | helpmanager@firemail.cc and alternative: helpmanager@iran.ir |
| Distribution | Awaits victims in illegal online downloads, such as KMSPico |
| Decryption tools | STOP Decryptor can’t decrypt this extension at the moment |
| Removal | Remove using antivirus while in Safe Mode (see instructions below) |
Data recovery prospects
NPSG virus encrypts files either using online or offline keys. To put it simply, if you have been affected by the online key, there are no possibilities to recover data without data backups. If, however, you have been affected by the so-called offline encryption, then your chances to restore some data are higher. Lets us explain the situation in detail.
To find out whether your files have been encrypted by online or offline keys, you must check your personal ID, but NOT THE ONE IN THE RANSOM NOTE. You must go to C:/SystemID/PersonalID.txt and check the IDs stored there.
IF any of your IDs end in t1, it is a sign that your files have been encrypted with the offline key.
Victims of offline encryption should wait until someone subject to the same encryption pays a ransom and shares the keys with the cyber security experts. Then STOP Decryptor will be updated (check for news here). However, if your ID or IDs end in any other character combination, then chances to recover files are extremely low.
Malware spreads in traditional ways
NPSG ransomware is essentially similar to its precursors TOPI, REHA, NOSU, and BTOS. It tends to hide in malicious downloads, especially ones that are designed to activate software licenses illegally. We’re talking about tools such as KMSPico, various software cracks and keygens. Therefore, if you’ve been looking for a PS or similar crack lately, there are no wonders why you’re dealing with a ransomware attack now.
Variants of STOP/DJVU, however, haven’t been noticed in malicious spam campaigns or injected in legitimate websites. It seems that the developers of this ransomware have opted out these infection vectors from their distribution scheme.
Remove NPSG ransom-demanding virus as soon as possible
Remove NPSG ransomware virus now to secure your computer system from further damage. As we have mentioned earlier, the virus carries password-stealing Trojans alongside it, so running a trustworthy antivirus tool will pick up such malicious programs as well. You must run your security software in Safe Mode to eliminate malware efficiently. The tutorial on that is provided down below.
Use these NPSG ransomware virus removal steps to cleanse your computer system. After that, concentrate on password replacement – such task is essential for your privacy. Finally, try to find these data backups you’ve created earlier. You can plug them in ONLY after you’re 100% sure the malware has been banished from your computer.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
NPSG Ransomware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
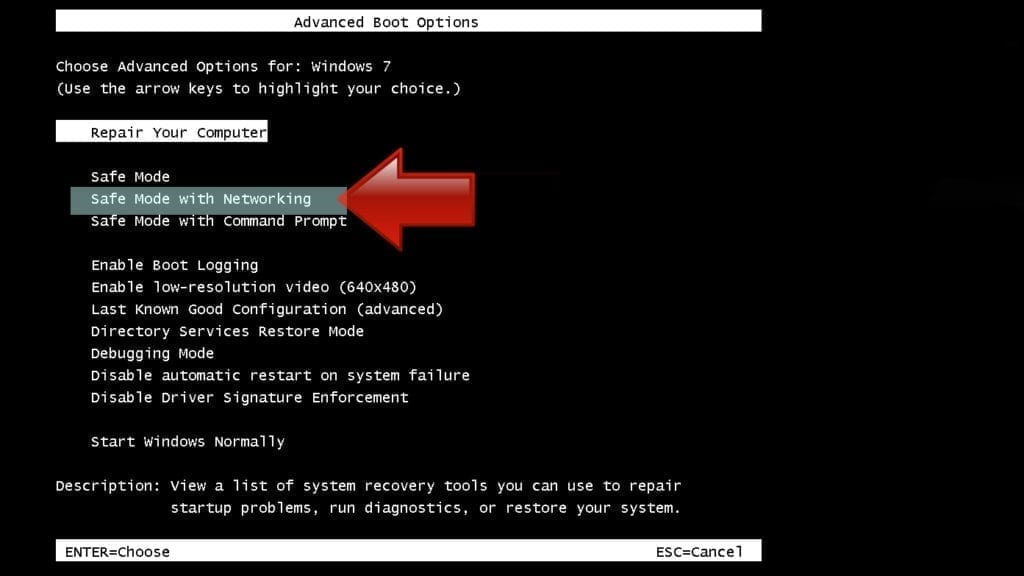
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
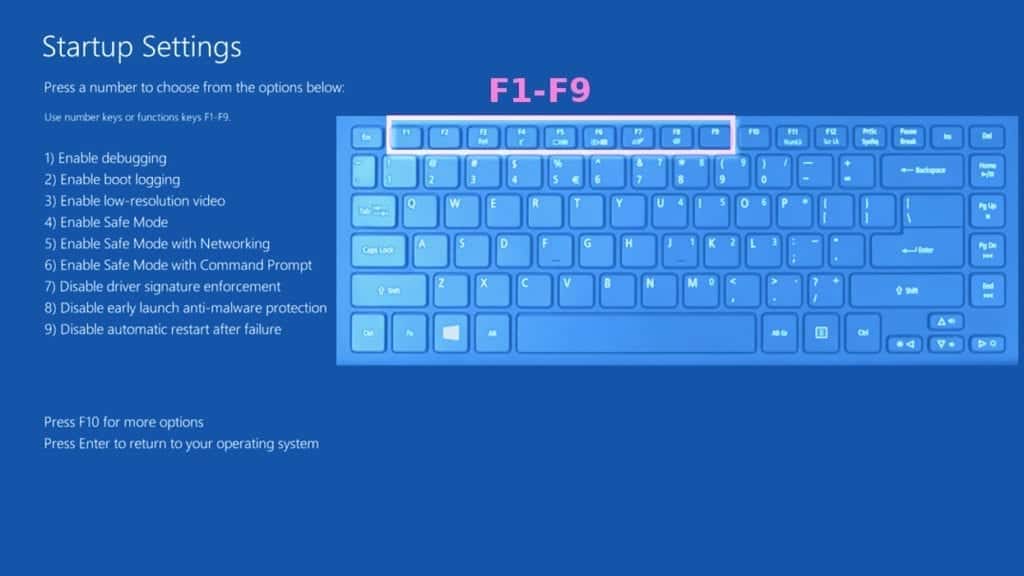
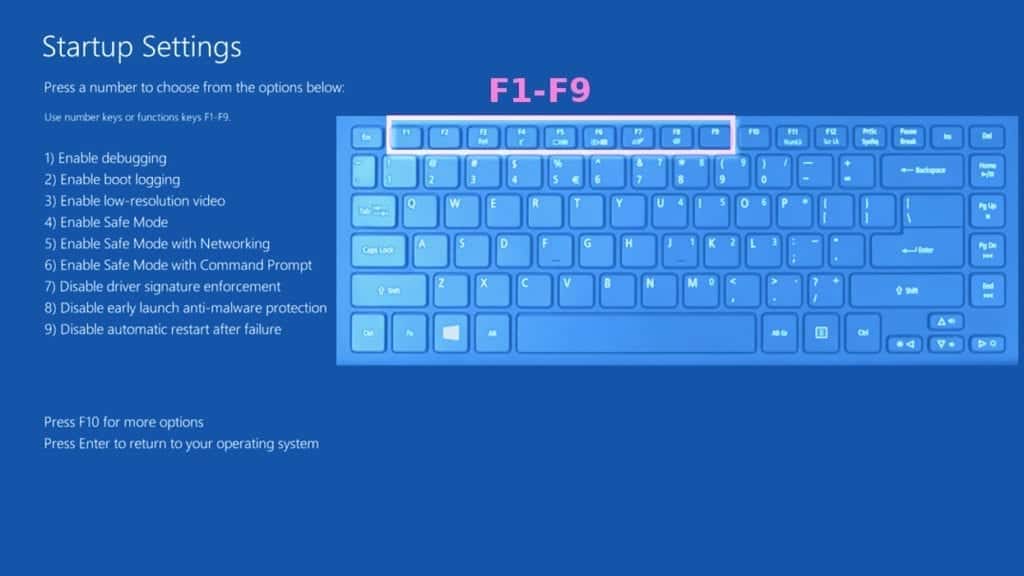
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
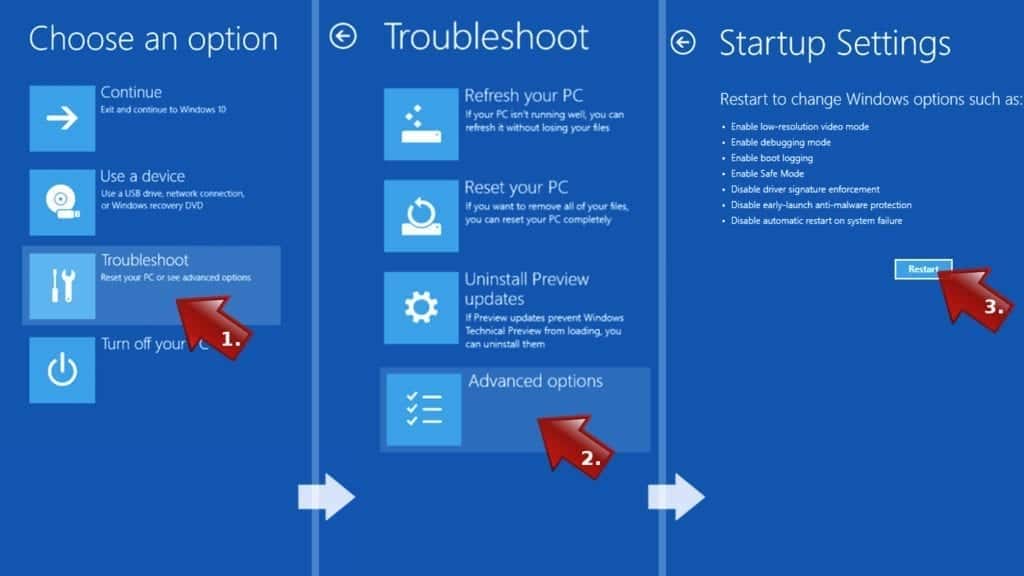
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove NPSG Ransomware files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
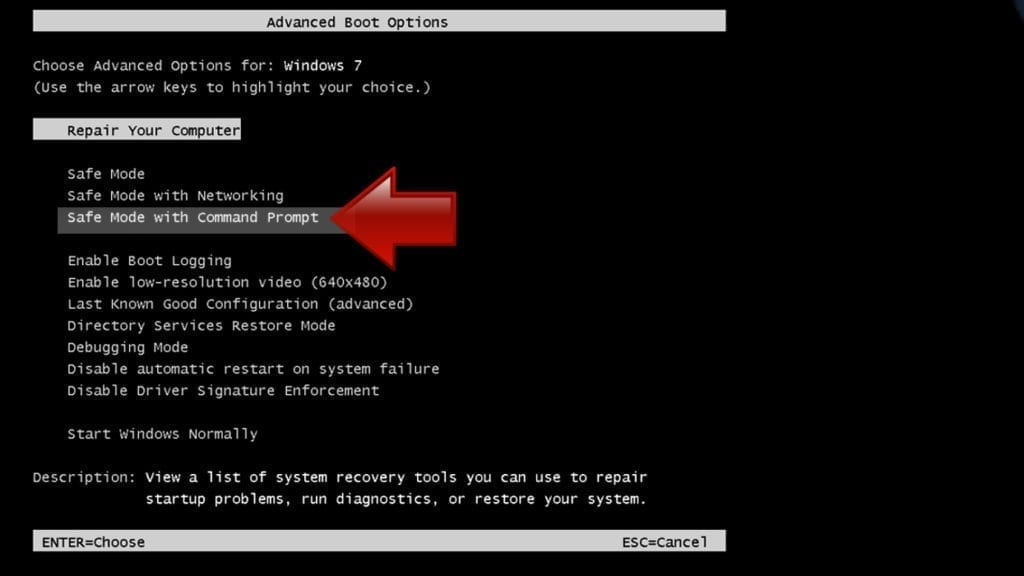
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
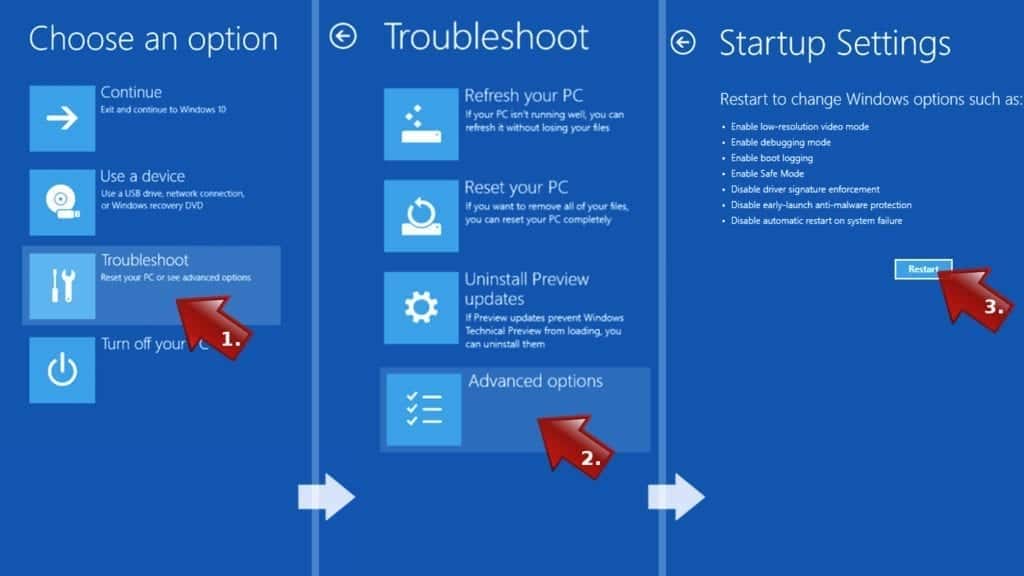
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
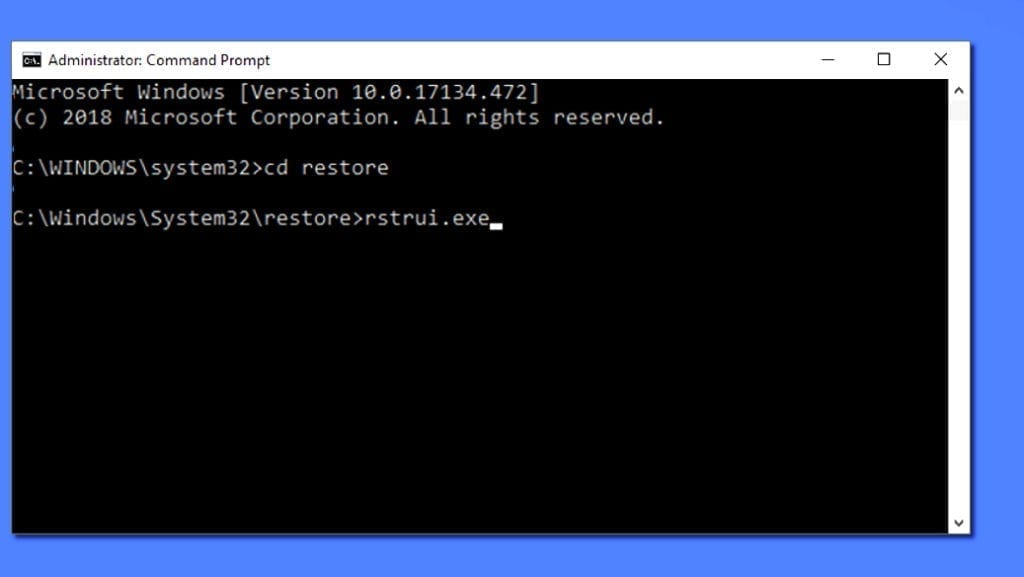
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
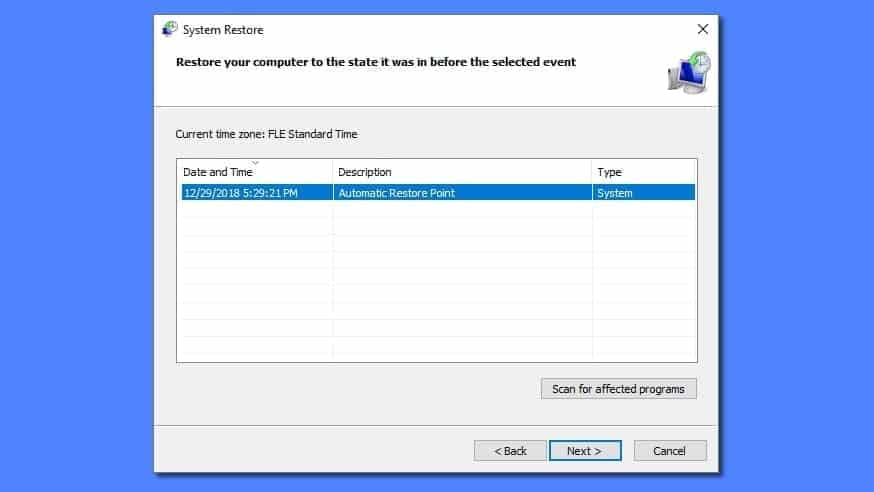
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
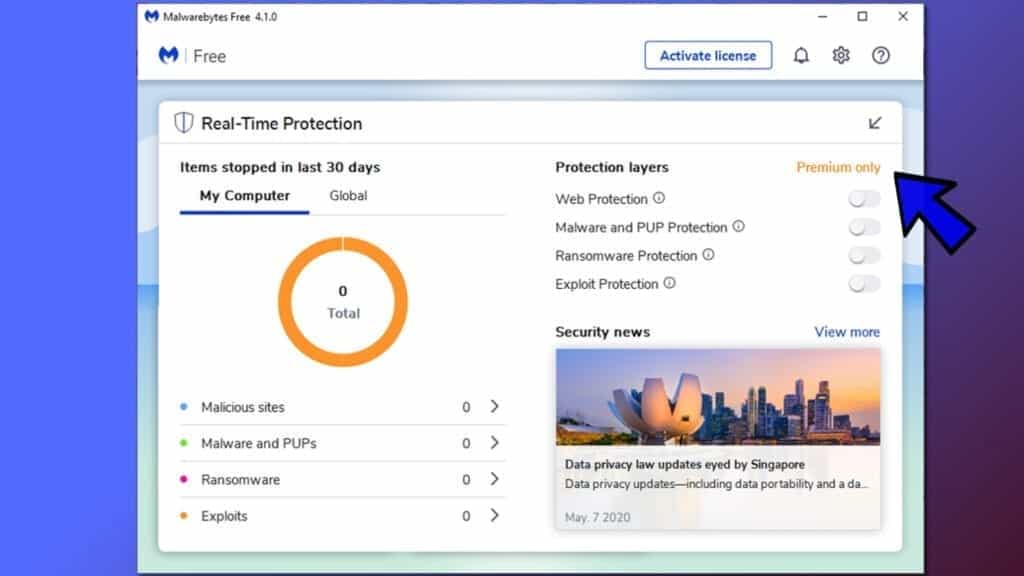
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
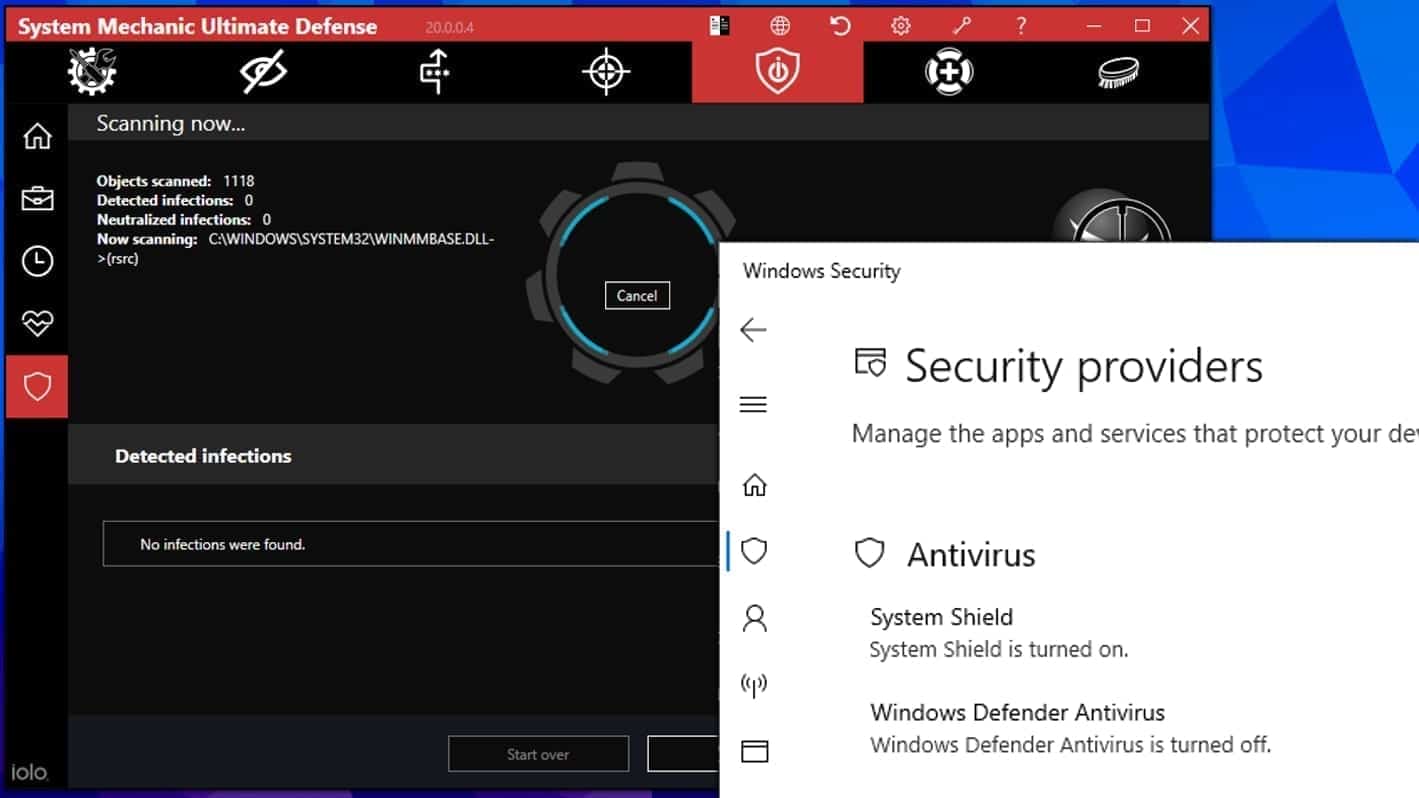
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.

Leave a Reply