NEFILM ransomware seeks to encrypt your files
Contents
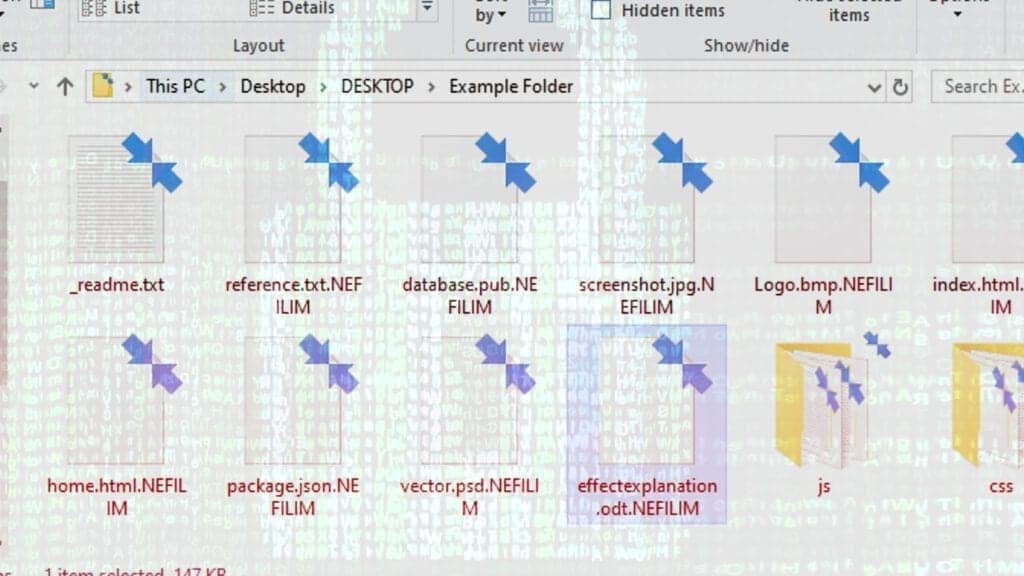
NEFILIM ransomware is a virus which originates from NEMTY ransomware family. It typically operates by encoding victim’s files on unsecured systems for the purpose of blackmailing – decryption of the files usually requires particular software which is possessed by the intruder. The encryption leaves all corrupted files with the .NEFILIM extension and by the time the action is completed, NEFILIM-DECRYPT.txt file appears on the user’s desktop.
The message which is found in the (NEFILIM-DECRYPT.txt) is quite straightforward – the victim has a choice – either to meet demands of the criminals or to take no action which, according to the criminals, will result in publicization of personal information within 7 days. The message (which is signed by jamesgonzaleswork1972@protonmail.com, pretty_hardjob2881@mail.com and dprworkjessiaeye1955@tutanota.com) also states that since the compromised files are encrypted using NEFILIM ransomware, it is not possible to regain access to original files using any third-party software.
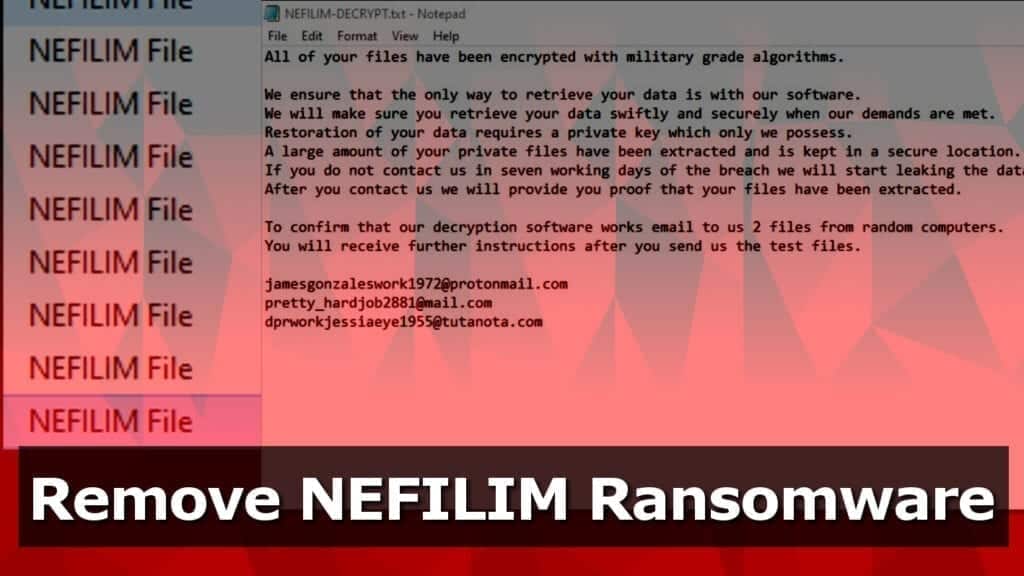
The intruders promise to provide the key needed to regain access to the files once the demands are met, but this course of action is not recommended, since putting yourself at the criminal’s mercy might lead to pointless financial losses – victim cannot be sure that the tools needed for .nefilim file decryption will be given.
Threat Summary
| Name | NEFILIM ransomware |
| Type | Ransomware; File-encrypting virus |
| Ransom note | NEFILIM-DECRYPT.txt |
| Encryption method | AES-128 + RSA-2048 |
| Ransom demand | Typically asks for $1000-$1800 in Bitcoin |
| Contact emails | jamesgonzaleswork1972@protonmail.com, pretty_hardjob2881@mail.com and dprworkjessiaeye1955@tutanota.com |
| Extension | .nefilim file extension |
| Decryption methods | No decryption tools available; restore files using data backup |
| Distribution methods | Spreads via malicious spam, infected downloads, deceptive installers |
| Removal | Remove using robust antivirus or anti-malware while in Safe Mode |
Unfortunately, it is true that in most of these kinds of cases the decryption without criminal’s intervention is impossible, unless the ransomware is still in development stages and has flaws which could be exploited in victim’s favor. NEFILIM virus uses AES 128 and RSA 2048 ciphers for data encryption and dynamically calls SystemFunction036 to generate new key per victim’s file.
Nevertheless, the only rational action you can take in this situation is to remove NEFILIM ransomware virus completely from your computer. Sadly, this action won’t help to restore your compromised files. However, you can always recover them from a backup. The only condition is that it needs to be created before the intrusion and held in a different location.
How ransomware infects your computer
Generally, all types of malware (including ransomware) can infect your computer in various ways – via trojans, illegitimate activation software (a.k.a. cracks), fabricated updaters, spam campaigns, unreliable download sources etc. Spam campaigns send deceitful emails, which might have infectious files or links attached to them.
Fake updaters can harm your system by exploiting outdated products and might install ransomware instead of the updates. Trojans are infamous for having many abhorrent capabilities, such as triggering additional malware installation. In fact, damaging files come in various formats, from Microsoft Office and PDF documents to executable files. Therefore, there is no single and effective method on how to identify these kinds of threats.
The easiest and most efficient way to infect victim’s computer is by exploiting people who use free file-hosting sites, various file sharing networks (Torrents, eMule, etc.) and in general – tend to download from the Internet inattentively. All of the before mentioned methods might be used to spread viruses, including NEFILIM ransomware.
Guide to remove NEFILIM ransomware virus
In order to keep your system safe from reoccurring intrusions and file encryptions, you need to remove the NEFILIM ransomware immediately. Certain preparation for the elimination is required beforehand, so follow closely. Follow the steps given below to boot your PC in Safe Mode, then proceed with the next steps to completely terminate the virus from your system.
It is important, that the NEFILIM Ransomware removal should be done using trustworthy antivirus or anti-malware software, to ensure that, we recommend reading our reviews on them. As soon as the removal is complete, do not forget to change passwords for all websites and accounts saved in your browsers imminently.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
NEFILIM Ransomware Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
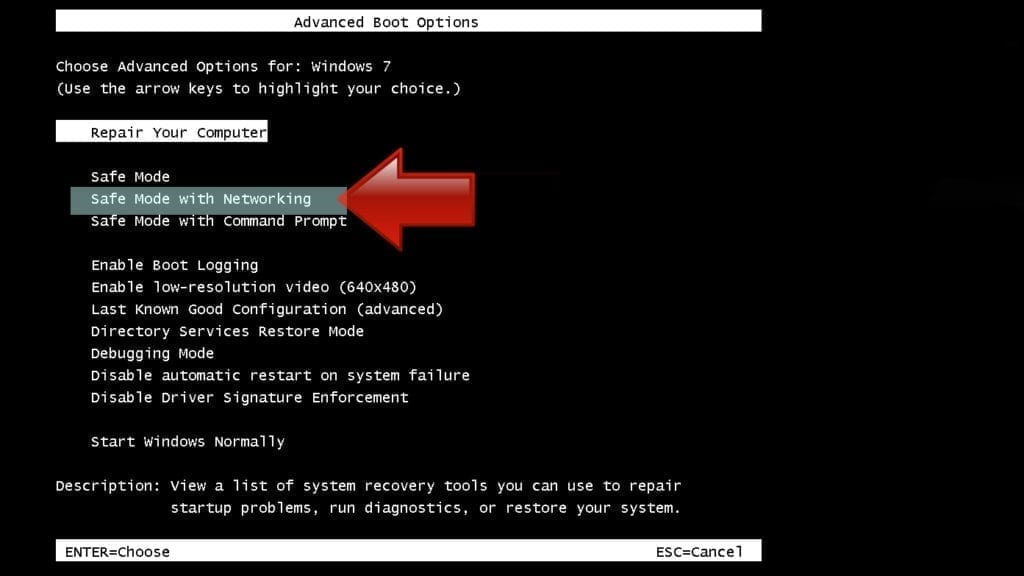
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
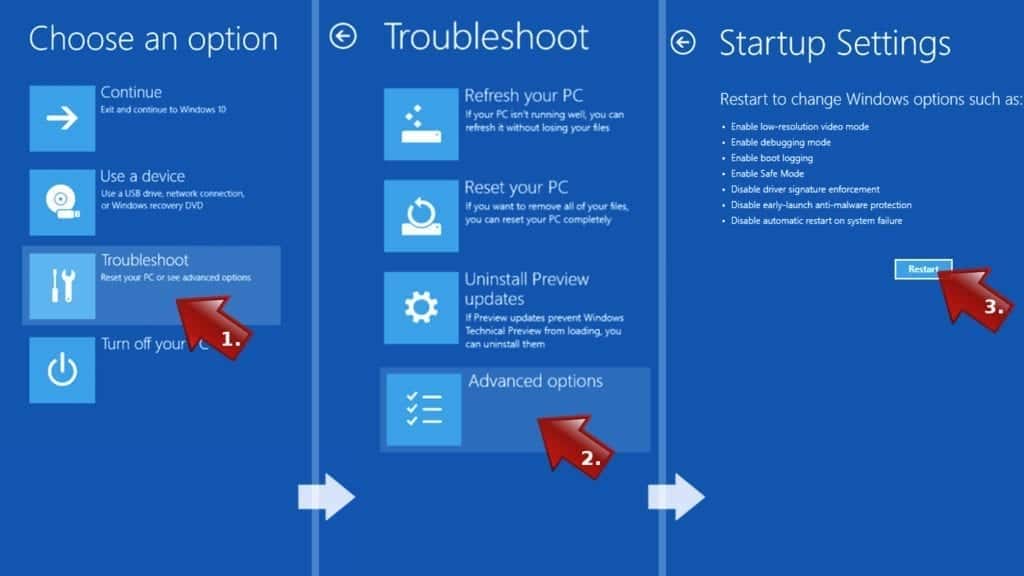
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
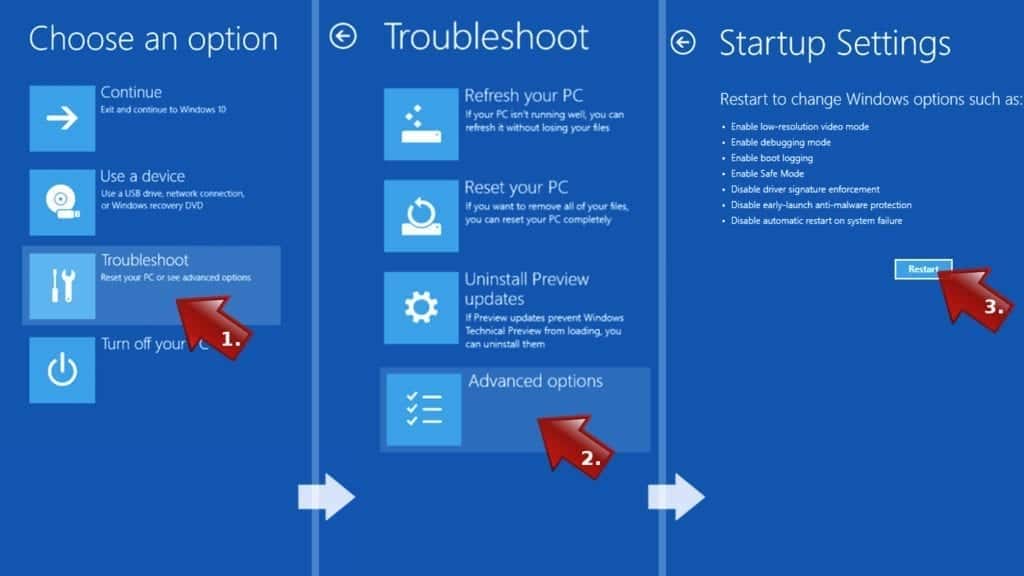
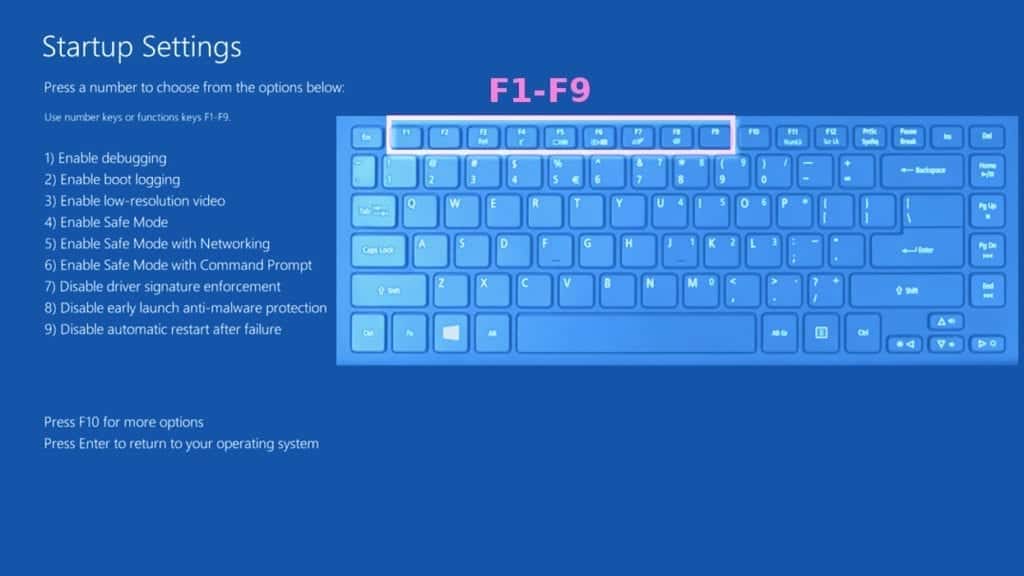
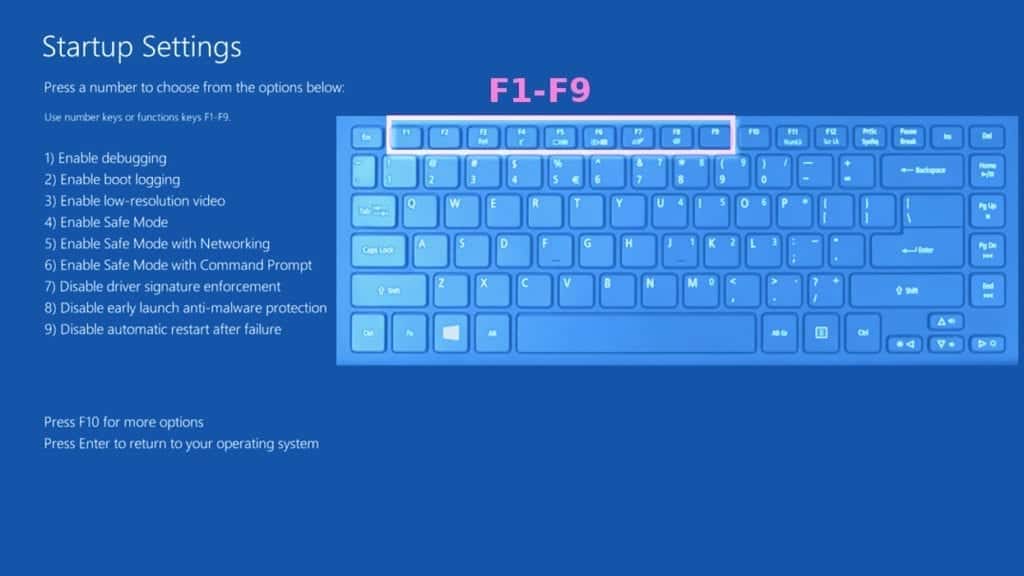
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove NEFILIM Ransomware files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
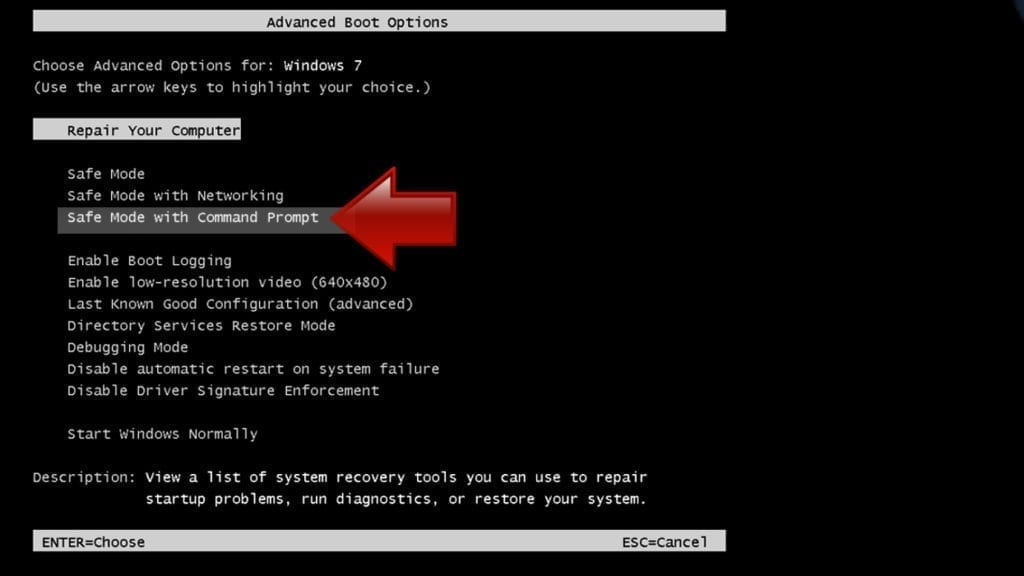
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
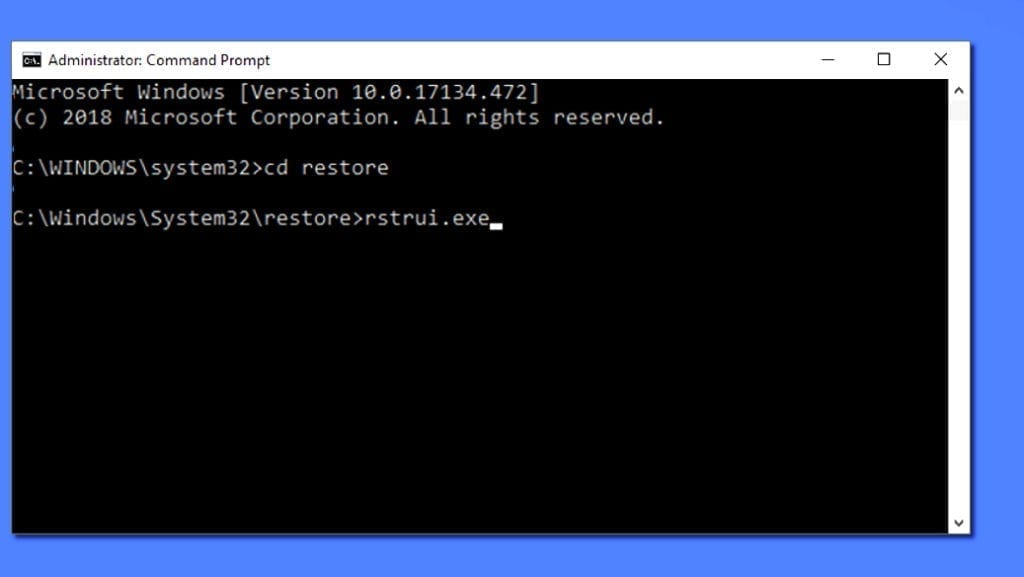
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
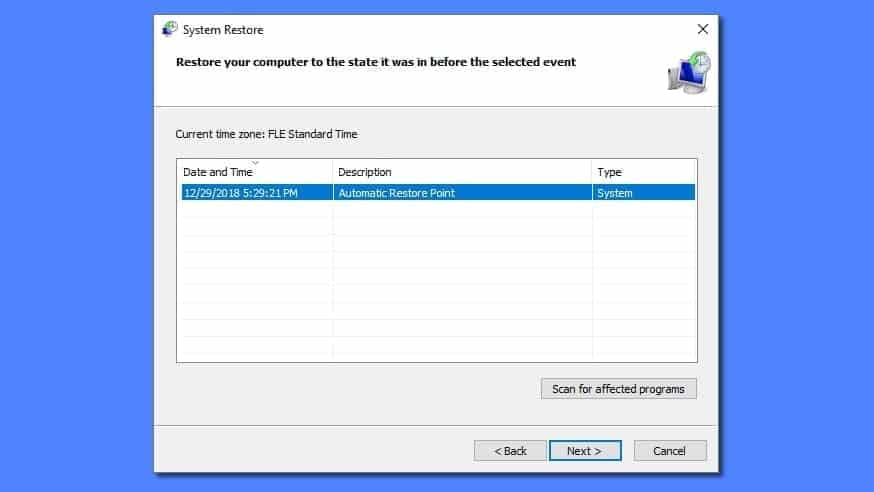
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
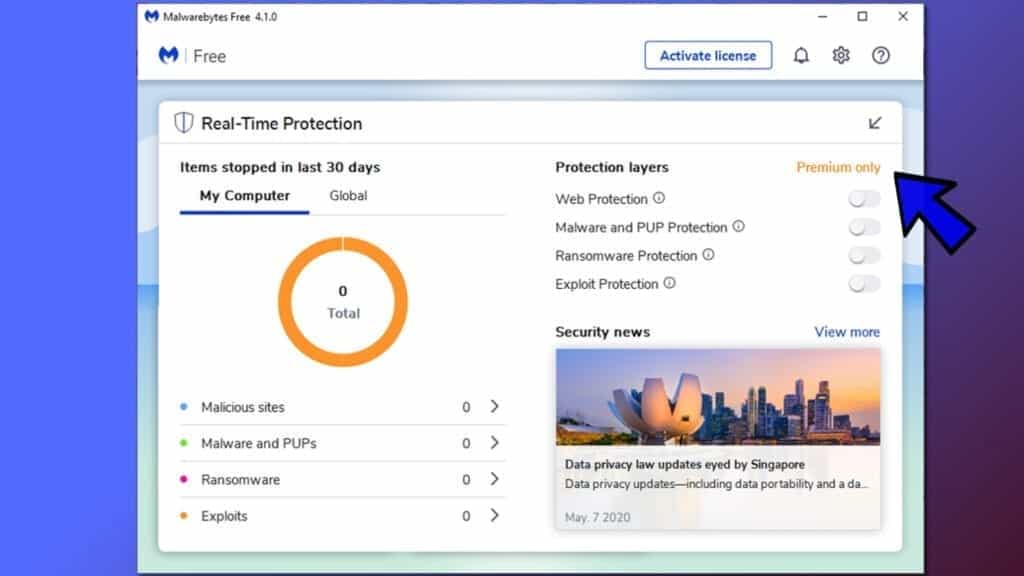
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
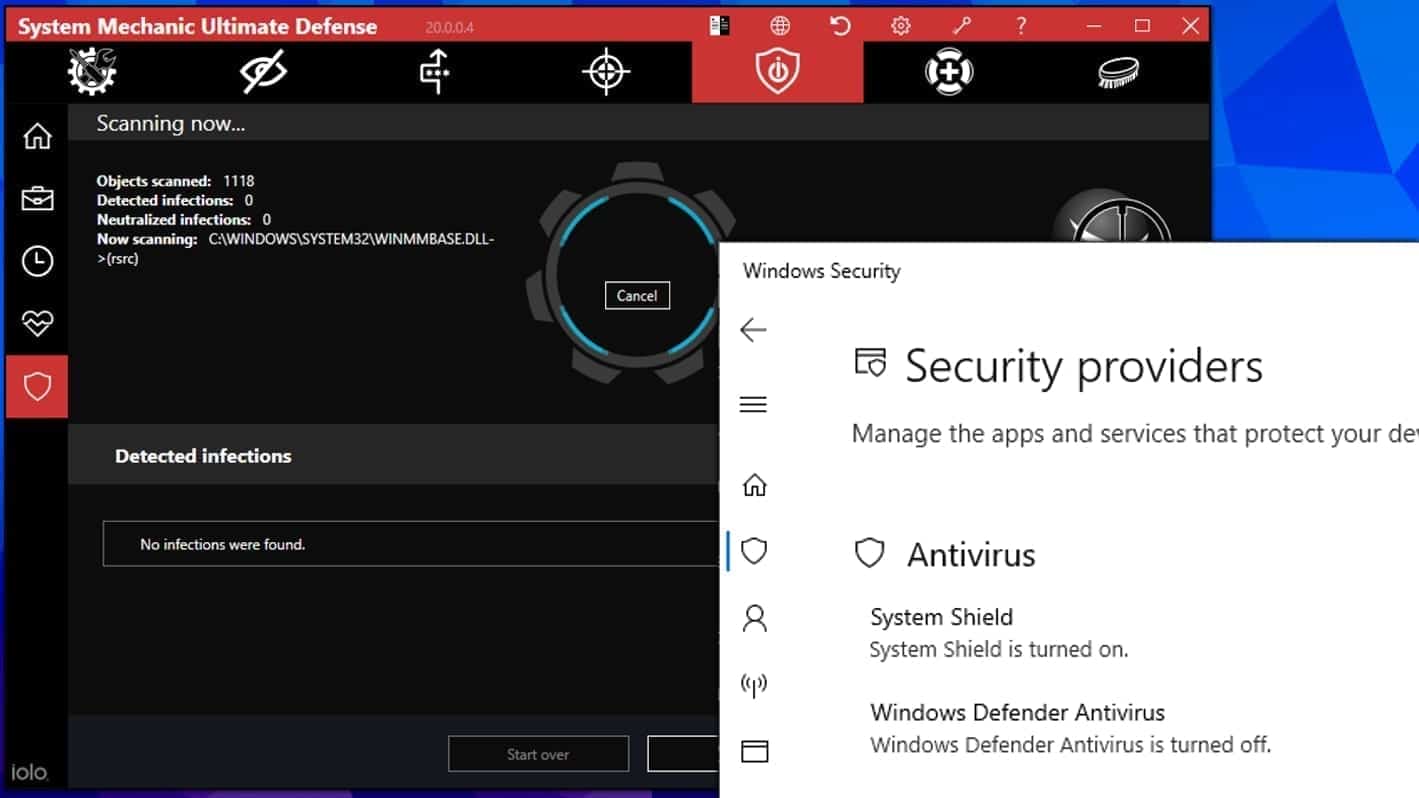
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Matt Corey is passionate about the latest tech news, gadgets and everything IT. Matt loves to criticize Windows and help people solve problems related to this operating system. When he’s not tinkering around with new gadgets he orders, he enjoys skydiving, as it is his favorite way to clear his mind and relax.

Thanks so much – removed the malware, need to restore files somehow! Did anyone have any success??