Remove KILLNET Ransomware Virus (DECRYPT .killnet FILES)
All you need to know about Killnet ransomware
Contents
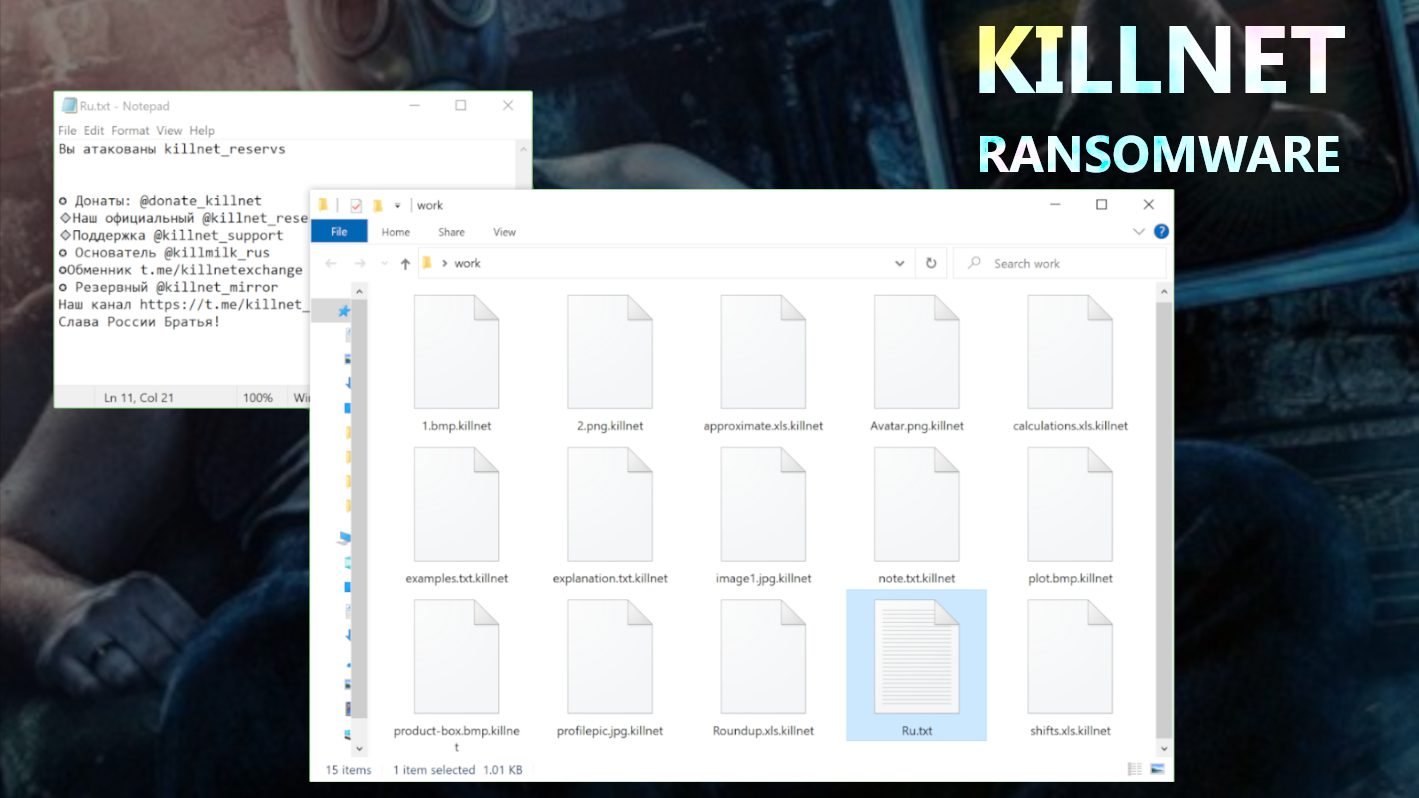
Killnet ransomware is a malicious computer virus designed to take files stored on a computer hostage. Differently than other existing ransomware, the Killnet hacktivist group seems to have created this threat solely to wreak havoc. After encrypting a file, the virus appends .killnet extension to its name before moving on to the next file. To explain it more graphically, files that were previously stored as 1.jpeg, 2.png, and 3.jpg automatically became 1.jpeg.killnet, 2.png.killnet and 3.jpg.killnet respectively.
Having completed this first stage, the ransomware then creates a ransom note in Russian (Ru.txt), however, the note doesn’t demand a ransom payment. In addition to that, Killnet ransomware virus also removes the existing desktop wallpaper. However, the image it eventually replaces it with will depend on the particular ransomware version that infected the computer.
Further details about the virus
The purpose of the ransom note is to bring the victim up to speed about the Killnet ransomware virus attack. Instead of traditional email addresses that are usually left in various ransomware notes, the criminals behind this malware choose to leave Telegram account usernames instead. At the end of the message, they will include a pro-Russian solidarity closing remark.
Generally, ransomware viruses are developed by online rogues with the intention of seizing control of other people’s data in order to extort fees from them. Over the years, we have been able to monitor a series of ransomware viruses and how they encrypt data. Following our extensive research, we came to the conclusion that it is extremely difficult, if not impossible, to reverse encryption without the involvement of those behind the attack. In fact, the best way to avoid being extorted is to always keep a data backup on an external data storage device.
To make matters even worse for those at the receiving end, paying a ransom fee to the cybercriminals is not a guarantee that decryption tools will be sent to them as promised. In other words, it becomes a double loss to the victim. Because of that, victims are strongly advised never to comply with the demands of cybercriminals. It is also important to note that paying ransom fees to cybercriminals encourages them to continue constituting a nuisance. Therefore, the only way to ensure that cybercriminals are defeated is to completely stop ransom payments. However, in this case, the cybercriminals do not demand a ransom, which implies that the virus is developed and distributed with sole intention to cause harm and corrupt user files.
We advise computer users to remove Killnet ransomware virus without further delay in order to salvage other files that are yet to be encrypted. Also, removing it on time will enable the victim to commence retrieval efforts soon enough. The only viable way to recover such damaged files is by making use of your backup device. That is why we always emphasize on the importance of keeping a backup at all times. They could be in the form of unplugged storage devices kept in different locations and remote servers etc. Such backups can come handy after experiencing a ransomware virus attack.
Our team advises investing in a trustworthy antivirus solution to keep further cyberattacks at bay. Our top pick in AV industry at the moment is INTEGO Antivirus, which we have extensively described in this review.
About the Killnet hacktivist group
Killnet is a pro-Russian hacktivist group that is mostly known for their unsophisticated DDOS attacks and regular and despicable statements about NATO in their Telegram channels. The collective says their targets are anyone who supports Ukraine. The group has multiple Telegram channels just like those listed in the ransom note, where they find a medium to ramble and spread misinformation about the war and politics in general.
Ransomware Summary
| Name | KILLNET Ransomware Virus |
| Type | Ransomware; Crypto-malware; Virtual Extortion Virus |
| Extension | .killnet |
| Cybercriminal Telegram channels | @donate_killnet, @killnet_reservs, @killnet_support, @killmilk_rus, @killnet_mirror, @killnetexchange |
| Damage | The ransomware encrypts files on unprotected computers and appends .killnet extension to their filenames. The virus also changes desktop wallpaper and drops short ransom notes called Ru.txt throughout the computer. |
| Ransom note | Ru.txt |
| Ransom demand | No demand – the ransomware seems to be purely destructive, although the criminals accept “donations” |
| Distribution | Victims often download this ransomware along illegal torrent downloads, malicious online ads, or malware-ladden attachments in phishing emails. |
| Detection names | Ransom:MSIL/FileCoder.AD!MTB (Microsoft), IL:Trojan.MSILZilla.55545 (B) (Emsisoft), HEUR:Trojan-Ransom.MSIL.Agent.gen (Kaspersky), IL:Trojan.MSILZilla.55545 (BitDefender), Malware.AI.3384415825 (Malwarebytes), Ransom.Sorry (Symantec) see all detection name variations on VirusTotal |
| Removal | Remove ransomware and related malware from your PC using trustworthy software like INTEGO Antivirus. |
Intego Antivirus for Windows
Award-winning antivirus solution for your PC.
Robust security software that provides robust 24/7 real-time protection, Web Shield that stops online threats/malicious downloads, and Prevention engine that wards off Zero-Day threats. Keep your PC safe and protected against ransomware, Trojans, viruses, spyware and other forms of dangerous programs.
How ransomware infects computers
Different types of malware, including ransomware viruses, are often spread via phishing and other social engineering tactics that are deceptive in nature. The cybercriminals that create them usually bundle them together with cloned software content. Such compromised files can be in diverse forms such as executables (including .exe), archives (including RAR and ZIP, etc.), JavaScript, PDF, and Microsoft Office documents, among similar others. Once a user opens an infected file in their computer, it triggers a ransomware attack.
Cybercriminals use diverse distribution methods to spread malware. Still, the common ones are deceptive drive-by downloads, malware embedded in emails and attachments, online scams, online torrent platforms, P2P sharing networks, illegal program activation (“cracks” and fake tools), fake updates, etc.
How to effectively safeguard computers against ransomware virus infections
As you can see from the list of malware distribution channels highlighted above, illegal software downloads should be shunned. Those in need of software programs should go to the official pages of the brand’s copyright owners or their authorized distribution partners to source for it. Also, trying to use “cracks” or cloned versions of software copies is risky and should be avoided entirely.
Additionally, emails and accompanying attachments that land in your inbox should always be inspected in a cautious manner. You should consider if the email is related to you or your activities. Is the originating address genuine or spoofed? If otherwise, please avoid opening the accompanying links/attachments because doing so could result in system infections.
It is crucial to install genuine antivirus from recognizable brands on your computer and keep it updated. Therefore, it is necessary to perform regular scans so that possible threats can be detected in a timely manner and removed.
Remove Killnet ransomware virus and recover data
For those whose computers may have become infected with the described malware already, we strongly advise that you use INTEGO Antivirus to remove Killnet ransomware virus. All you need to do is to install it and run it for a full scan. INTEGO Antivirus for Windows will also ensure that your computer remains protected as we advance.
Follow the instructions provided below to prepare your PC for the malware removal procedure.
OUR GEEKS RECOMMEND
Our team recommends a two-step rescue plan to remove ransomware and other remaining malware from your computer, plus repair caused virus damage to the system:
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
KillNet Ransomware Virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove KillNet Ransomware Virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
REPAIR VIRUS DAMAGE
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.
Norbert Webb is the head of Geek’s Advice team. He is the chief editor of the website who controls the quality of content published. The man also loves reading cybersecurity news, testing new software and sharing his insights on them. Norbert says that following his passion for information technology was one of the best decisions he has ever made. “I don’t feel like working while I’m doing something I love.” However, the geek has other interests, such as snowboarding and traveling.
Recent Posts
Remove POZQ Ransomware Virus (DECRYPT .pozq FILES)
Beware Of POZQ Ransomware Virus Attack POZQ ransomware virus is a file-encrypting malware that has…
Remove BOZQ Ransomware Virus (DECRYPT .bozq FILES)
BOZQ Ransomware Virus Scare: The Need to Secure Your PC BOZQ ransomware virus is a…
Remove BOWD Ransomware Virus (DECRYPT .bowd FILES)
BOWD Ransomware Virus Scare & How to Secure Your Computer BOWD ransomware virus is the…
Remove POWD Ransomware Virus (DECRYPT .powd FILES)
POWD Ransomware Virus: The Need to Protect Your Computer POWD ransomware virus was created by…
macOS Ventura is out: All the cool features to know
October 24: Update day for iOS, iPadOS, and MacOS Apple announced back in June, at…
Remove NURY Ransomware Virus (DECRYPT .nury FILES)
NURY ransomware virus: a data-encrypting threat NURY ransomware is a malicious computer virus created by…