_encrypted ransomware aims to damage your files
Contents
_encrypted is the name of a virus that is categorized as ransomware – it aims to encrypt ordinary user‘s files. Users who experience this infection are usually unable to access personal files. The hackers behind the attack demand a ransom – $1000 to let the victim regain access to his files. The files affected can be identified easily since the virus appends ._encrypted to every file name that has been touched. After this is carried out, a ransom note called README_encrypted.txt is created that contains information regarding this crypto infection.
This guide explains what is the aim of _encrypted file virus and how you can safely eliminate it from your computer system, plus what further steps to take.

README_encrypted.txt contents
The message found in the ransom note is unambiguous, to say the least – victim‘s files have been encrypted and he needs to pay $1000 to regain access to them. To initiate the decryption process, the user needs to contact the cybercriminals behind the attack via a website on the Tor network. The victim is also provided with metadata.bin file that can be found in the user folder. However, at the time this article was written, the website address provided in _encrypted ransom note was blank. This is probably due to the fact that the malware is still in the development stages or released for testing purposes.
No matter the circumstances, it is important that you do not contact the hackers in cases like this. This is due to a couple of reasons. First, paying them money means escalating a problem even more. Since the hackers are completely profit-driven, they will not have the incentive to continue committing cybercrimes if it’s not profitable. Second, hackers simply cannot be trusted. If they see an opportunity to extort you even more (even after making the initial payment), they will definitely use it.
Unfortunately, usually, there is little the victim can do to regain access to his files using outside methods. It might be possible if there are known bugs or flaws that can be exploited in the user‘s favor. Other than that – it is a far stretch to manually retrieve encrypted files without hacker‘s interference. This is due to the fact that _encrypted, like most other types of contemporary ransomware, uses RSA+AES cryptography. To better understand what ransomware is doing to your files, you need to understand the basic principles of cryptography.
| Name | _encrypted virus |
| Type | Ransomware |
| Ransom note | README_encrypted.txt |
| Ransom amount | $1000 in Bitcoin |
| Contact | Via provided Onion website (Tor browser required) |
| Damage | Makes all files inaccessible by encrypting them. Drops ransom-demanding notes that suggest visiting the provided onion website for further instructions how to pay the ransom. |
| Detection names | TR/FileCoder.yvkux (Avira), Ransom:Win32/FileCoder.AB!MTB (Microsoft), Trojan-Ransom.Win32.Encoder.klv (Kaspersky), Trojan.GenericKD.44206852 (B) (Emsisoft) see full list on VT |
| Distribution | Spread via infected downloads (such as software cracks), deceptive email spam or malicious websites. |
| Removal | Remove ransomware using robust malware removal tool. For virus damage repair, scan with RESTORO. |
Effect on your files
RSA is an encryption system that has been created in the 1970s by British intelligence authorities. It was designed to ensure the safe transmission of information. Since then, it is one of the most successful asymmetric encryption systems. Meanwhile, AES cryptography is a system that was created at the start of this century and is still used by the U.S. government to this day. It uses a 4 stage-symmetric encoding system to ensure file safety.

So, it is quite apparent that the combination of these two military-grade encryption systems means that retrieving files manually or by using some sort of third-party software is just not an option. Using decryption tools from the internet might even cause more extensive damage to your system since they often contain various itself. Having this in mind, there are some things you can do. First, you need to remove _encrypted ransomware and all of its contents from your system. After that, you will be able to restore files from a backup.
Scan your system for FREE to detect security, hardware and stability issues. You can use the scan results and try to remove threats manually, or you can choose to get the full version of software to fix detected issues and repair virus damage to Windows OS system files automatically. Includes Avira spyware/malware detection & removal engine.
Virus distribution ways
When talking about _encrypted ransomware proliferation methods, we can argue that they are similar to other ransomware viruses. For the most part, they spread through downloads from untrustworthy websites. For example, downloading a crack, keygen, software activation tool, or else, from a Torrent might expose you to a cyberattack. Having this in mind, it is important to realize, that the benefit gained by downloading something illegally might be outweighed by potential damage done to your system. In fact, you should never use untrustworthy downloading websites and file-sharing platforms.
Another way that is used by the developers of _encrypted virus is malspam campaigns. To put it shortly, this is a social engineering scheme – hackers send thousands of deceitful emails to random internet users. These emails might contain various information – from resumes to business offers or special deals on software. Usually, the information inside these emails urges the user to interact with the contents of it (clicking a link or opening an attachment). Once this is done, the virus tries to breach through the system‘s security.
Although email services are getting better at filtering these kinds of messages into spam folders, you should always pay attention when opening emails and do not interact with any suspicious-looking ones.
Remove _encrypted ransomware
To ensure your system’s safety you need to remove _encrypted ransomware and all of its associated contents. This is crucial since malware like this could do more extensive damage to your PC – for example, download a AZORULT password stealer. We recommend you use a trustworthy anti-malware software that would be capable of dealing with this kind of task.
After that, you should take all of the necessary actions to make restore your system‘s health. RESTORO is a perfect tool for this kind of task, it will ensure that no virus-associated contents are present in your PC. To remove _encrypted virus follow the steps below:
OUR GEEKS RECOMMEND
Our team recommends removing malware using a professional antivirus software.
REMOVE THREATS WITH ROBUST ANTIVIRUS

Get INTEGO ANTIVIRUS for Windows to remove ransomware, Trojans, adware and other spyware and malware variants and protect your PC and network drives 24/7. This VB100-certified security software uses state-of-art technology to provide protection against ransomware, Zero-Day attacks and advanced threats, Intego Web Shield blocks dangerous websites, phishing attacks, malicious downloads and installation of potentially unwanted programs.
Use INTEGO Antivirus to remove detected threats from your computer.
GeeksAdvice.com editors select recommended products based on their effectiveness. We may earn a commission from affiliate links, at no additional cost to you. Learn more.
_encrypted ransomware virus Removal Guidelines
Method 1. Enter Safe Mode with Networking
Step 1. Start Windows in Safe Mode with Networking
Before you try to remove the virus, you must start your computer in Safe Mode with Networking. Below, we provide the easiest ways to boot PC in the said mode, but you can find additional ones in this in-depth tutorial on our website – How to Start Windows in Safe Mode. Also, see a video tutorial on how to do it:
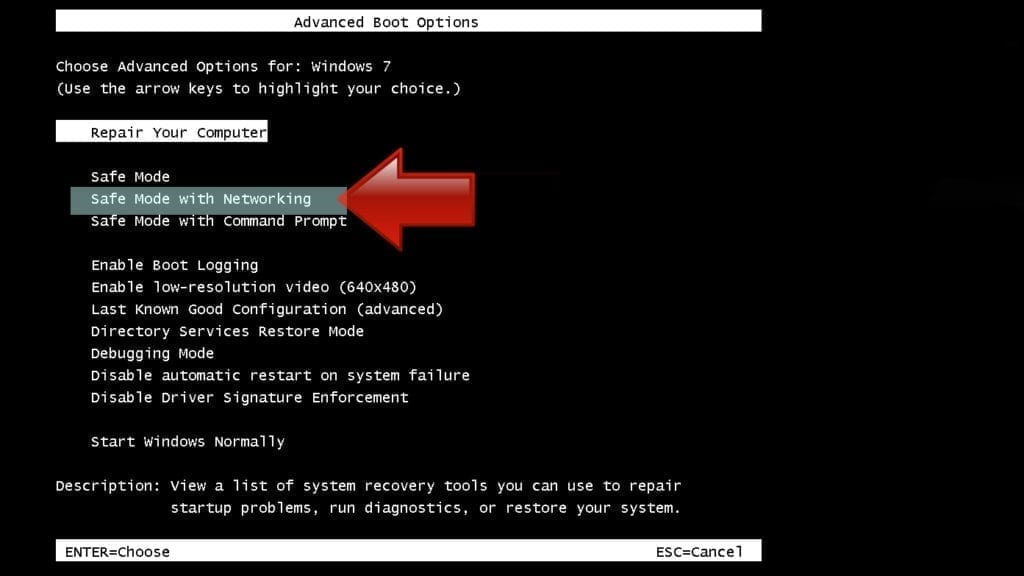
Instructions for Windows XP/Vista/7 users
- First of all, turn off your PC. Then press the Power button to start it again and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. This launches the Advanced Boot Options menu.
- Use arrow keys on the keyboard to navigate down to Safe Mode with Networking option and press Enter.
Instructions for Windows 8/8.1/10 users
- Open Windows Start menu, then press down the Power button. On your keyboard, press down and hold the Shift key, and then select Restart option.

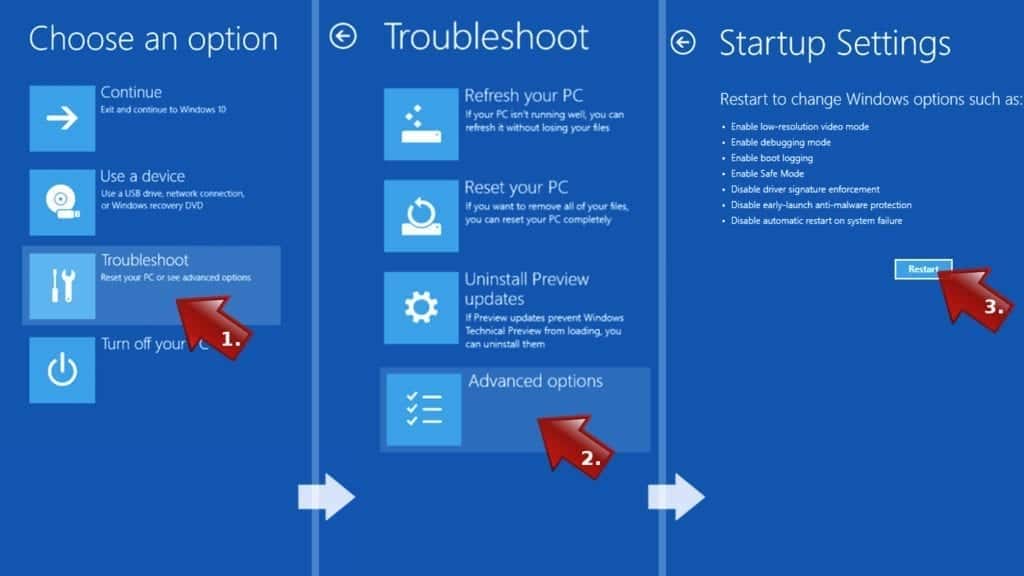
- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
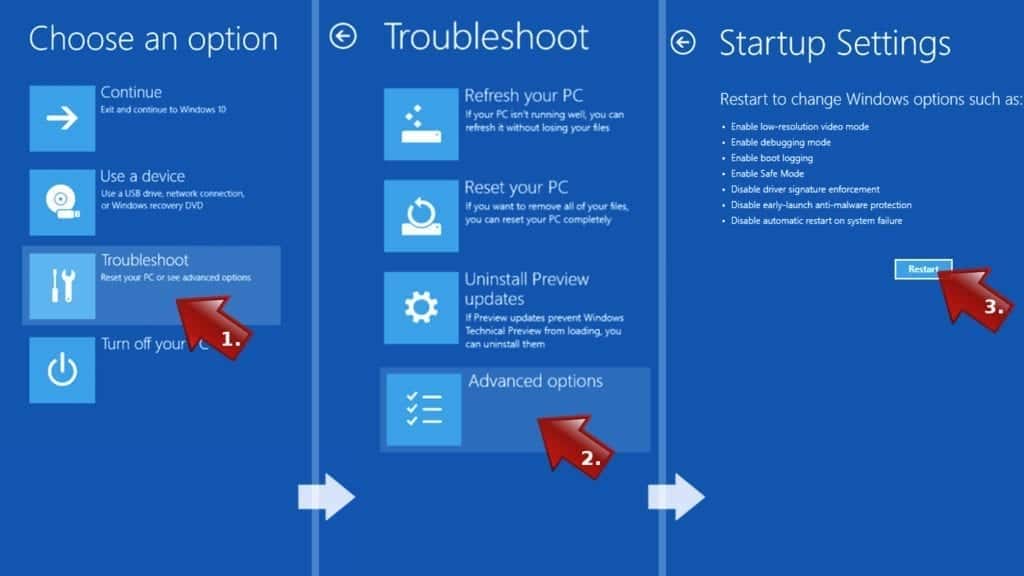
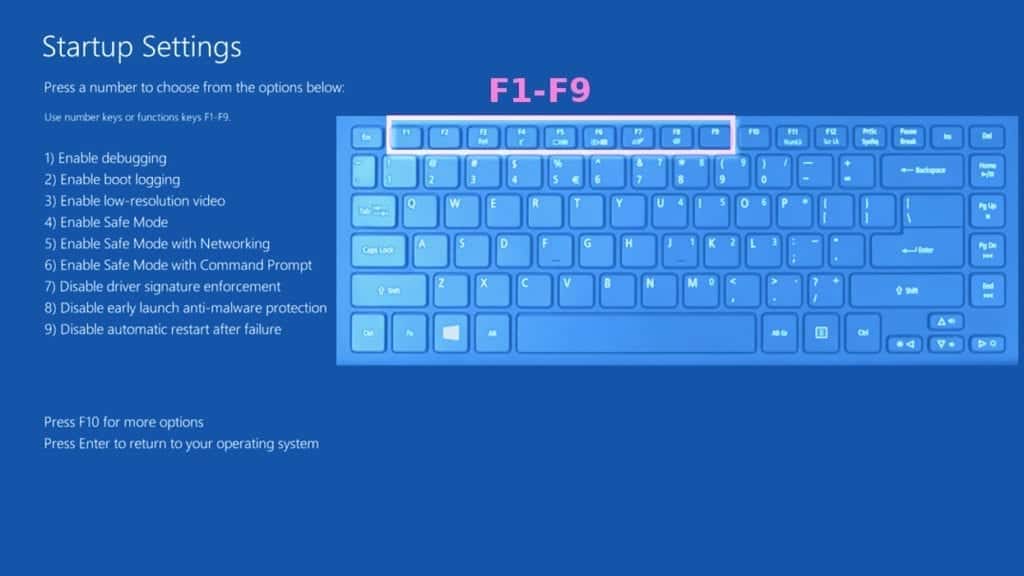
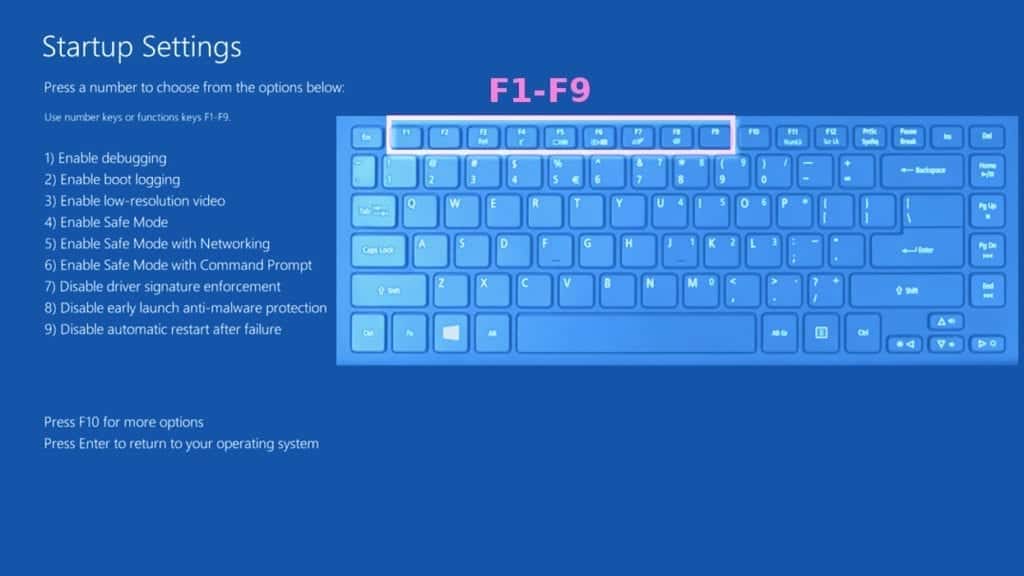
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Networking. In this case, it is the F5 key.
Step 2. Remove files associated with the virus
Now, you can search for and remove _encrypted ransomware virus files. It is very hard to identify files and registry keys that belong to the ransomware virus, Besides, malware creators tend to rename and change them repeatedly. Therefore, the easiest way to uninstall such type of a computer virus is to use a reliable malware removal program. In addition, we suggest trying a combination of INTEGO Antivirus (removes malware and protects your PC in real-time) and RESTORO (repairs virus damage to Windows OS files).
Method 2. Use System Restore
In order to use System Restore, you must have a system restore point, created either manually or automatically.
Step 1. Boot Windows in Safe Mode with Command Prompt
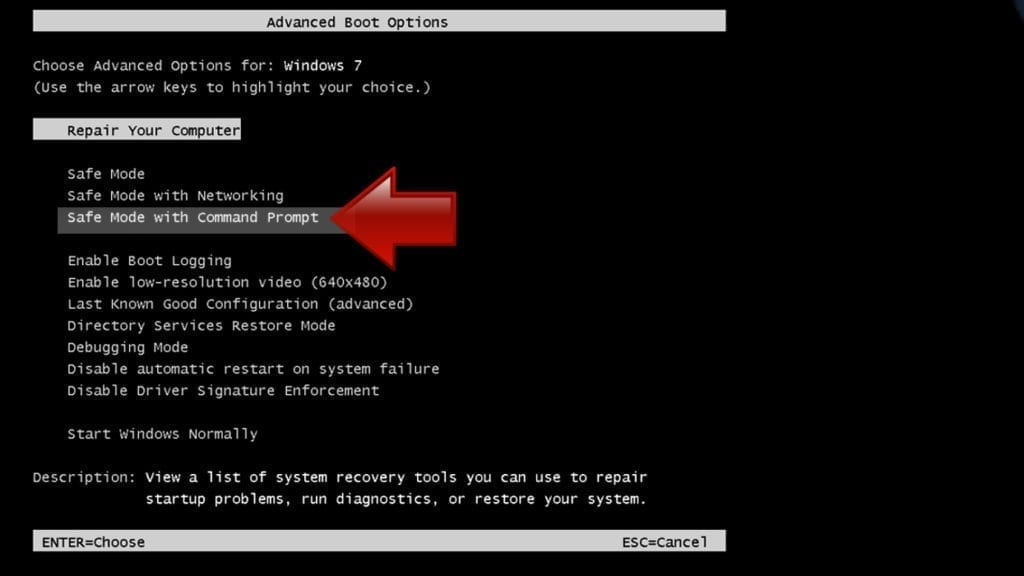
Instructions for Windows XP/Vista/7 users
- Shut down your PC. Start it again by pressing the Power button and instantly start pressing F8 button on your keyboard repeatedly in 1-second intervals. You will see Advanced Boot Options menu.
- Using arrow keys on the keyboard, navigate down to Safe Mode with Command Prompt option and press Enter.
Instructions for Windows 8/8.1/10 users
- Launch Windows Start menu, then click the Power button. On your keyboard, press down and hold the Shift key, and then choose Restart option with the mouse cursor.

- This will take you to Windows Troubleshoot screen. Choose Troubleshoot > Advanced Options > Startup Settings > Restart. Tip: If you can't find Startup Settings, click See more recovery options.
- In Startup Settings, press the right key between F1-F9 to enter Safe Mode with Command Prompt. In this case, press F6 key.
Step 2. Start System Restore process
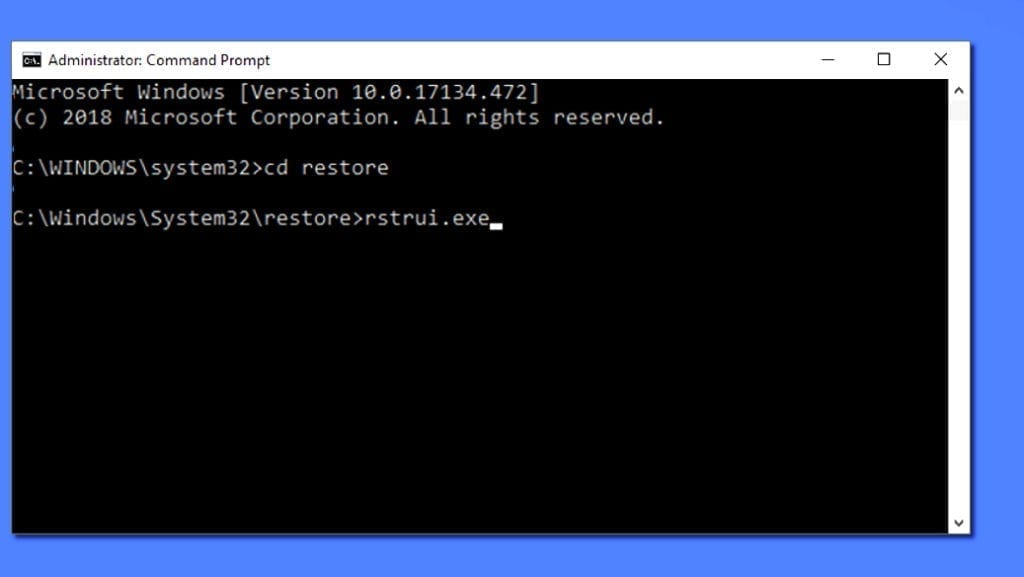
- Wait until system loads and command prompt shows up.
- Type cd restore and press Enter, then type rstrui.exe and press Enter. Or you can just type %systemroot%system32restorerstrui.exe in command prompt and hit Enter.
- This launches System Restore window. Click Next and then choose a System Restore point created in the past. Choose one that was created before ransomware infection.
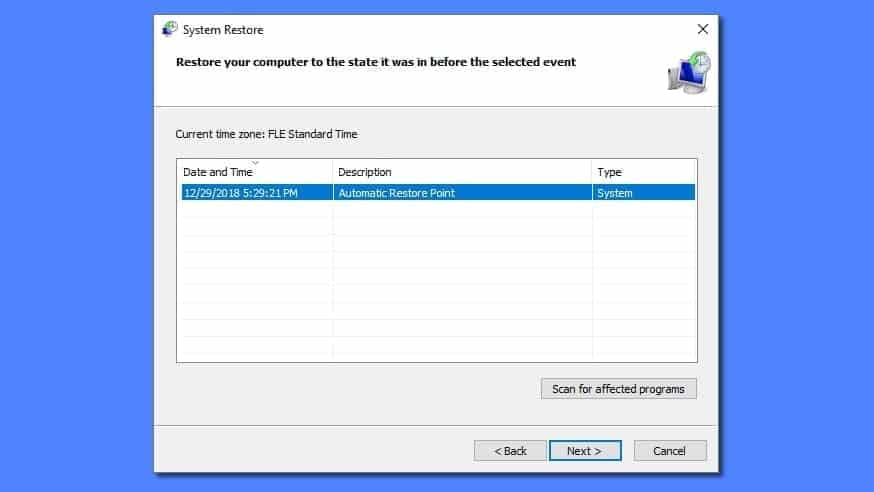
- Click Yes to begin the system restoration process.
After restoring the system, we recommend scanning the system with antivirus or anti-malware software. In most cases, there won't be any malware remains, but it never hurts to double-check. In addition, we highly recommend checking ransomware prevention guidelines provided by our experts in order to protect your PC against similar viruses in the future.
Alternative software recommendations
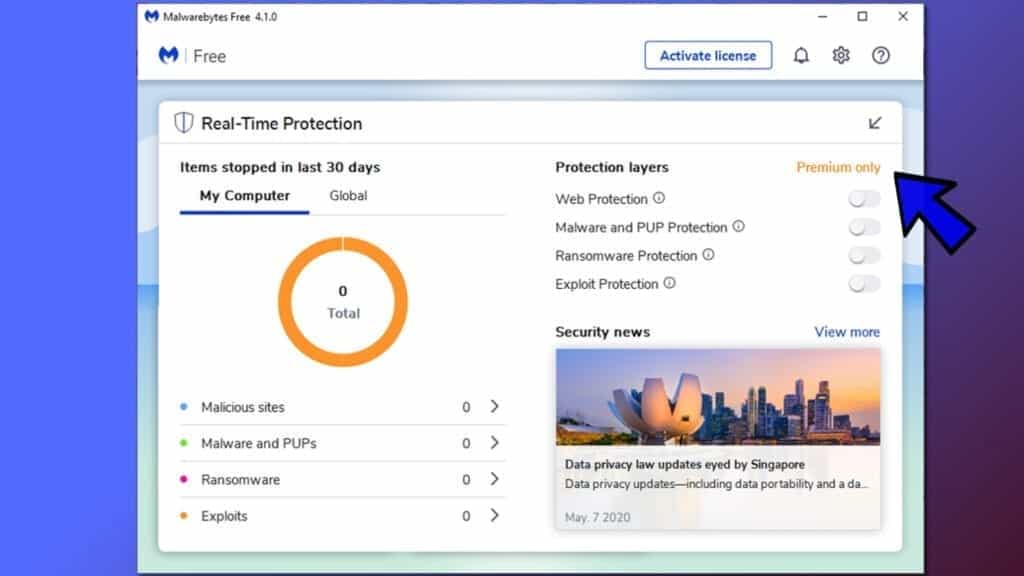
Malwarebytes Anti-Malware
Removing spyware and malware is one step towards cybersecurity. To protect yourself against ever-evolving threats, we strongly recommend purchasing a Premium version of Malwarebytes Anti-Malware, which provides security based on artificial intelligence and machine learning. Includes ransomware protection. See pricing options and protect yourself now.
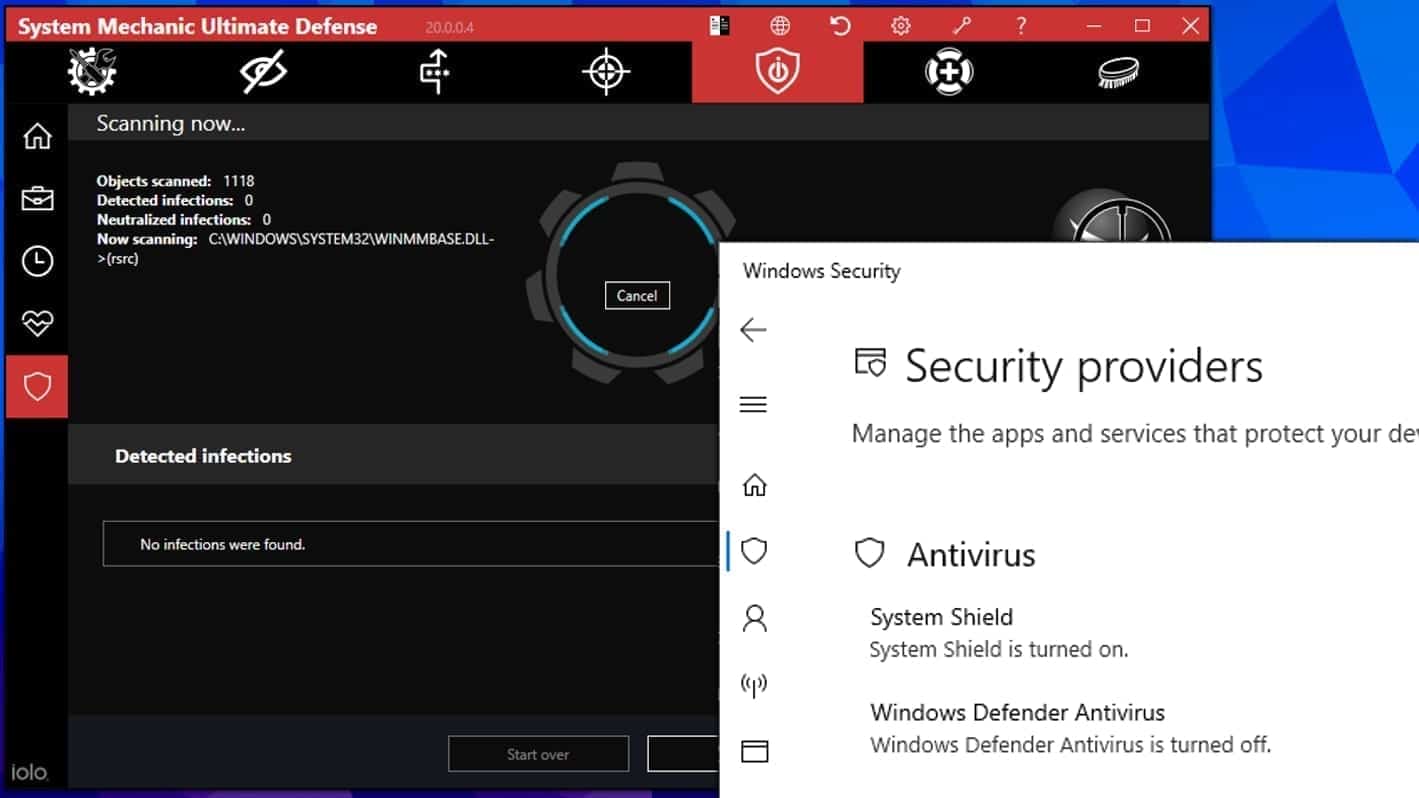
System Mechanic Ultimate Defense
If you're looking for an all-in-one system maintenance suite that has 7 core components providing powerful real-time protection, on-demand malware removal, system optimization, data recovery, password manager, online privacy protection and secure driver wiping technology. Therefore, due to its wide-range of capabilities, System Mechanic Ultimate Defense deserves Geek's Advice approval. Get it now for 50% off. You may also be interested in its full review.
Disclaimer. This site includes affiliate links. We may earn a small commission by recommending certain products, at no additional cost for you. We only choose quality software and services to recommend.

Matt Corey is passionate about the latest tech news, gadgets and everything IT. Matt loves to criticize Windows and help people solve problems related to this operating system. When he’s not tinkering around with new gadgets he orders, he enjoys skydiving, as it is his favorite way to clear his mind and relax.
Leave a Reply