NitroHack virus modifies a JavaScript file to steal account tokens
Contents
Cyberspace has recently been hit by a new Discord malware, also known as NitroHack. This virus was particularly developed to apply malicious changes to JavaScript files to illegally gather victims’ tokens. It spreads as a fake software crack for the premium Nitro service on Discord.
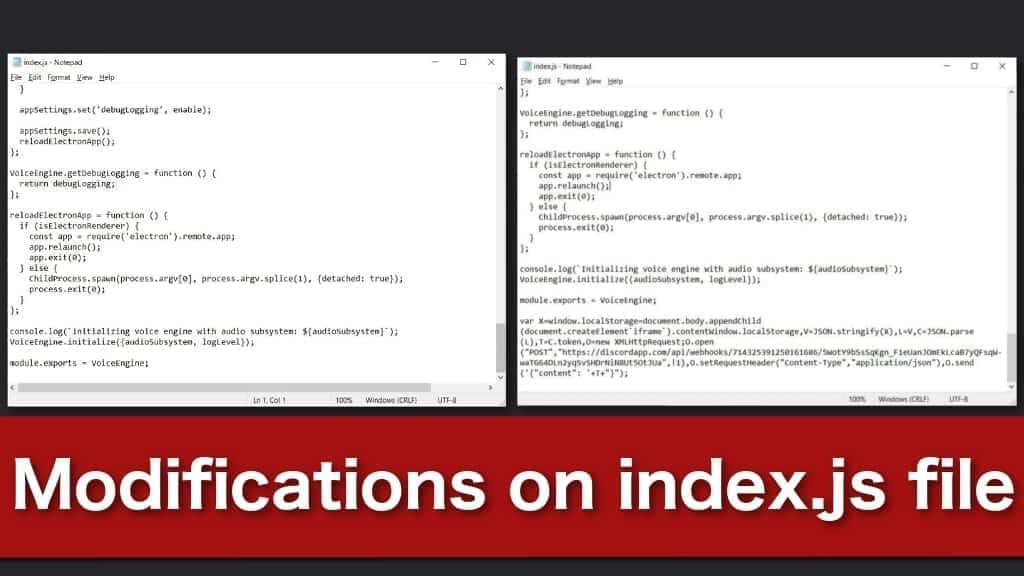
This malware primarily aims to embed malicious code into index.js file and make the same changes in files on public test builds and alpha clients. People can manually check if their accounts are affected — open the file via Notepad and search for suspicious codes after “module.exports = VoiceEngine;” line.
Even though professional antivirus systems are capable to detect the malware, they usually do not identify the modifications in the JavaScript files. This way NitroHack can remain on the system performing malicious activities.

People who try to get rid of the malware should not only scan their systems with a top-notch antivirus but also uninstall Discord fully and then reinstall it again. This way the JavaScript file is restored to the primary state — no malicious code inside.
Files on the infected systems should contain malware codes. In other words, it allows the attackers to receive victims’ tokens every time they log into their Discord account. Additionally, it scans the databases of Yandex, Chromium, Safari, and others for password-related information.
Furthermore, NitroHack malware is programmed to launch https://discordapp.com/api/v6/users/@me/billing/payment-source URL and try to gather saved payment information. People risk exposing their credit card details, full name, billing address, and other sensitive data.
Malware persistence — it distributes itself via direct Discord messages on infected accounts
Another notable feature of the virus is its ability to distribute itself. Cybercriminals have programmed the malware to spread links to fake Discord Nitro software cracks via direct messages. Thus, infected accounts are used for further spread of the virus.
If people on the targeted account’s friend list click on the link, they start an automatic installation of NitroHack malware. This feature of the virus allows to create a never-ending stream of infections unless people start to identify malicious links.
It is essential to never open any links that look suspicious — even if they come from your friends. Hackers are highly skilled and create messages that look legitimate. Thus, people should refrain from clicking on any types of links in general, unless they are sure about their safety.
Additionally, many people continue to browse on peer-to-peer (P2P) networks for software cracks. Cybersecurity’s community highly encourages people to stay away from such pages and never download any applications to stop the spread of NitroHack and other malware.
Discord recently attracted new malware developments
Discord application has recently become an epicenter of new viruses. Apart from the latest NitroHack virus, researchers have warned users about another password-stealing cyber threat — AnarchyGrabber malware that has a new version, called AnarchyGrabber3.
All variants of Discord virus now are exploiting the easy access to JavaScript files. Experts consider it to be one of the main factors why this popular gaming chat service received so much attention from cybercriminals. In addition, such attack techniques allow the malware to stay on the system undetected for a longer period of time.
Furthermore, regular computer users who are not highly advanced in IT would never even notice the NitroHack or similar malware infection. It simply modifies the Discord client and then does not run again. Thus, even if the virus executable is detectable, the client modifications are not.
Such well-developed infections may run on the attacked computer for excessive periods of time. In fact, it continues to send account tokens, collect sensitive data and distribute itself via direct messages until a new Discord update overwrites the malicious code inside index.js file.
Likewise, it is essential to refrain from clicking on any suspicious links inside Discord application and outside of it. As evident, it is essential to have a running antivirus at all times. Yet, people should be aware of the latest cybersecurity news and check their systems for malware manually as well.

Scott Bolton is a senior content strategist in our Geek’s Advice team. He is exceptionally passionate about covering the latest information technology themes and inspire other team members to follow new innovations. Despite the fact that Scott is an old-timer among the Geeks, he still enjoys writing comprehensive articles about exciting cybersecurity news or quick tutorials.
Leave a Reply